Hello firstblood team! I've found a business logic flaw in the "Book Appointment" feature.
Summary
Business logic vulnerabilities are flaws in the design and implementation of an application that allow an attacker to elicit unintended behavior. This potentially enables attackers to manipulate legitimate functionality to achieve a malicious goal.
By using a hidden parameter in the book-appointment page, it is possible to choose the doctor. This shouldn't be an available option, since it is not part of the form.
By abusing this parameter, we can even book "unavailable" doctors.
Steps to reproduce
- proxy requests through burp suite
- go to https://0a71d31af52a-lumbridge7.a.firstbloodhackers.com/book-appointment.php
- fill the form, intercept request and click on "book appointment" to trigger the POST request
- add to the body of the request the param "drId=1" (or any other doctor id with the status unavailable*)
- send request
- Appointment booked with doctor, regardless of their status being "unavailable" or not.
This can be tested with many drId, since it's an easily guessable single digit numeric value.
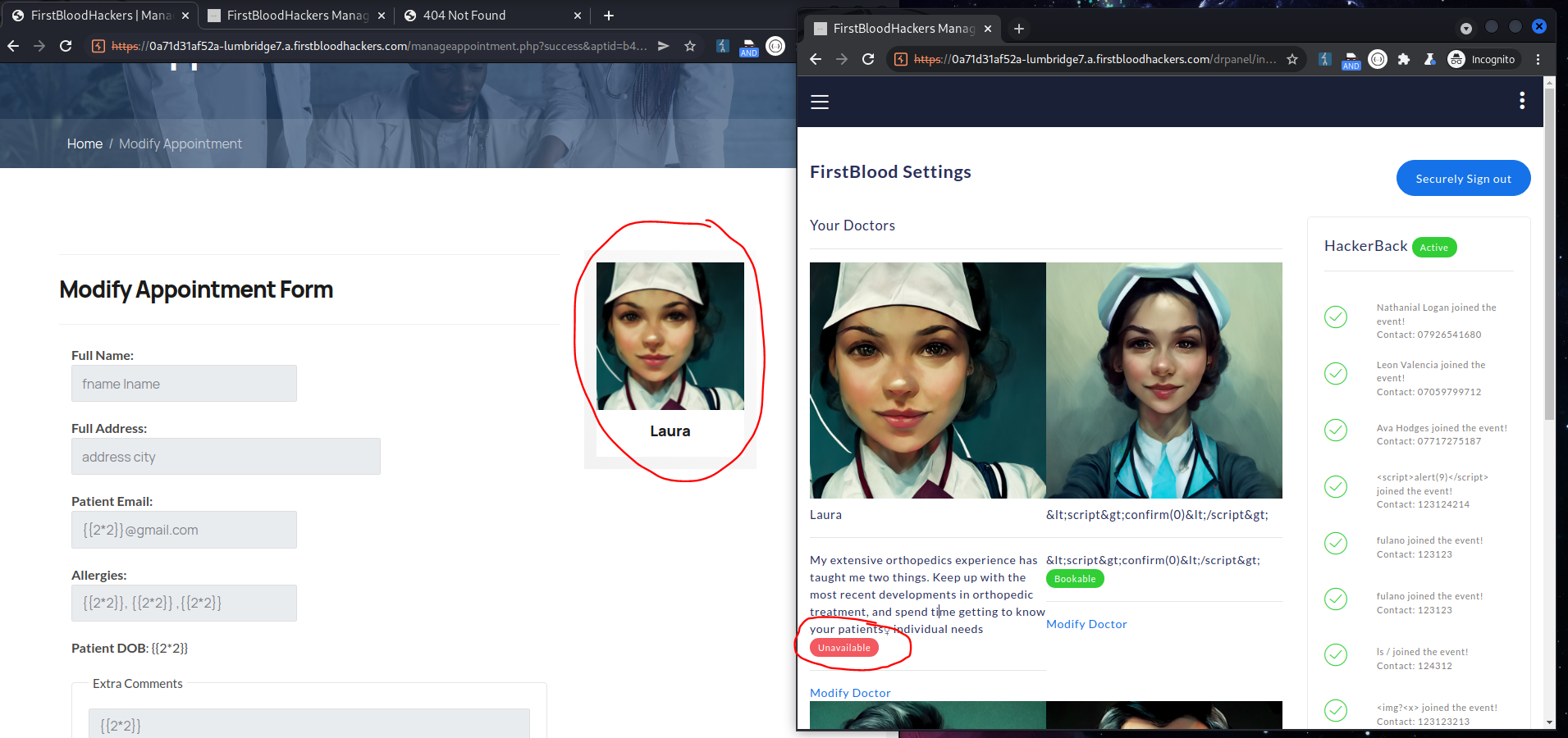
Getting a doctor with status unavailable
For testing purposes, access the doctor dashboard and set any doctor with the status = unavailable.
grab the drId from the url.
i.e., https://0a71d31af52a-lumbridge7.a.firstbloodhackers.com/drpanel/edit-doctor.php?id=4
id=4 is the drId we'll use to book the appointment.
POC
Impact
Anyone can book appointments with Unavailable doctors.
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports 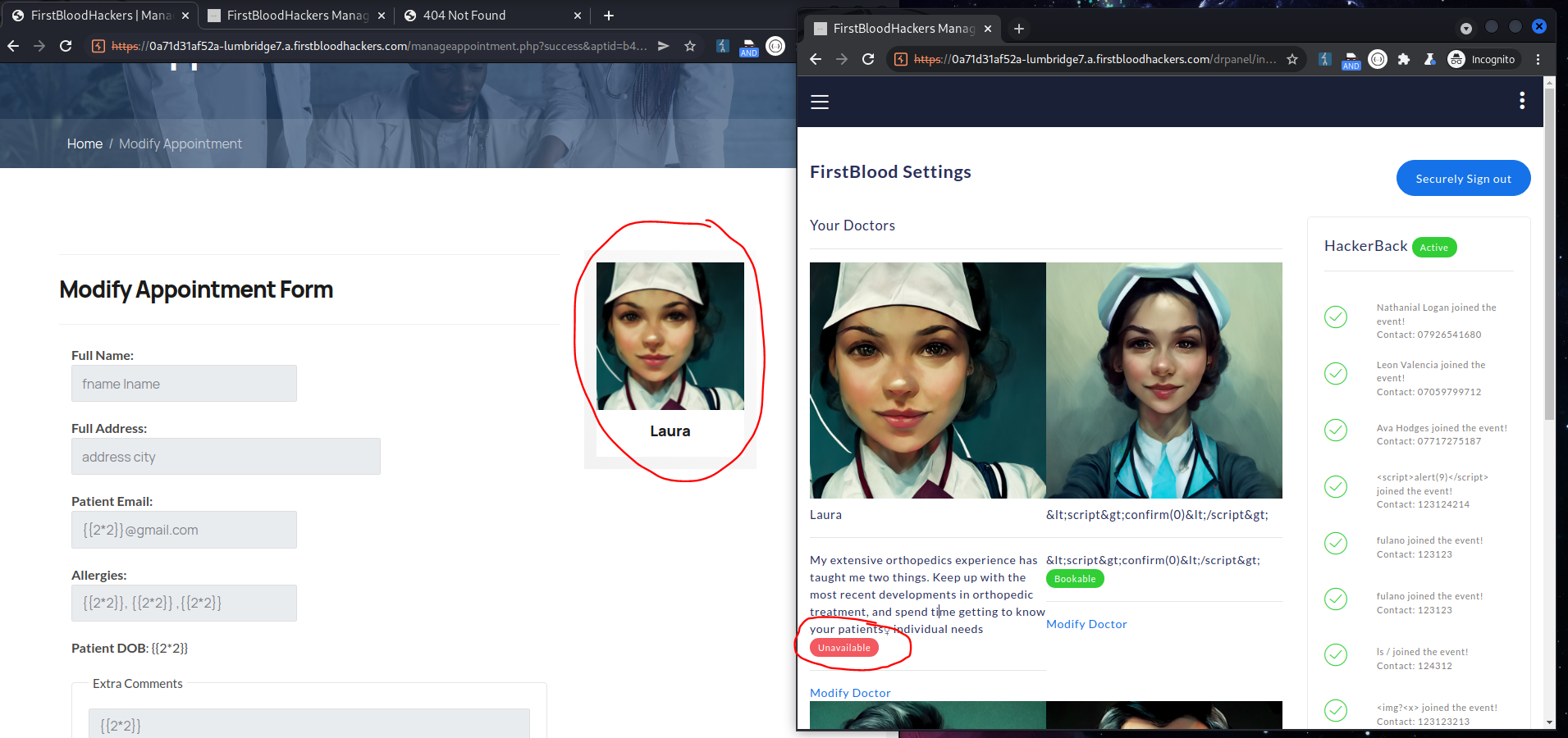
 Report Feedback
Report Feedback