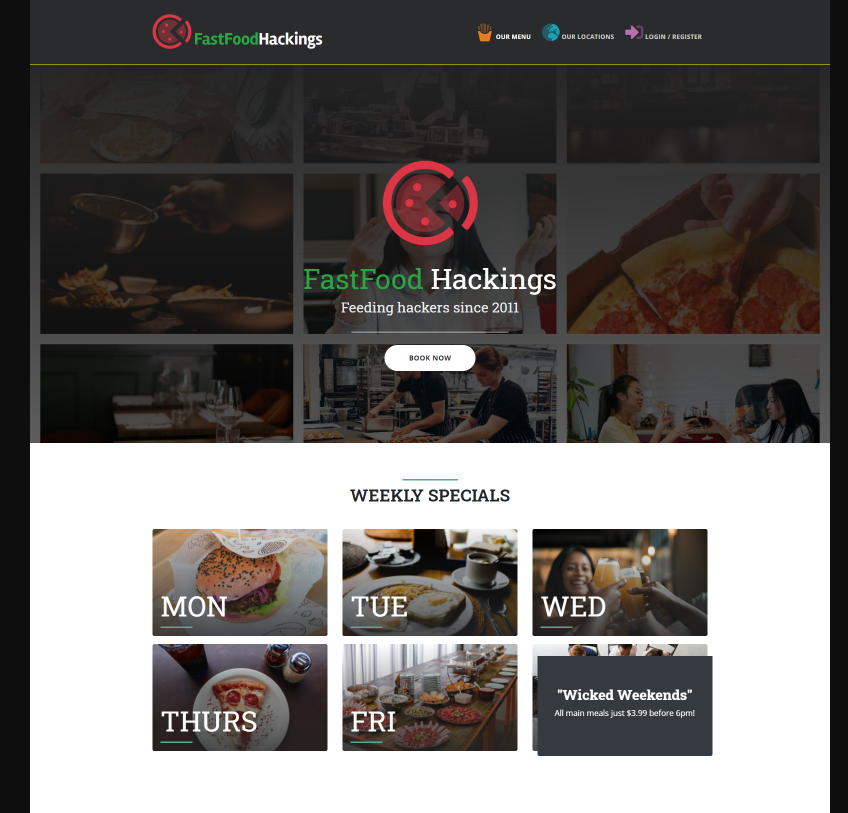
Learning about web application vulnerabilities
New or experienced, learn about various vulnerability types on custom made web application challenges based on real bug bounty findings! Learn about new techniques and bypasses whilst embracing the mindset of a hacker.
You have knowledge on what type of vulnerability you should be looking for but are you able to find it?
There are no flags to find and instead you're learning about the various mistakes developers make when developing and how vulnerabilities arise from this.
The stage is yours, take it and have some fun!
Browse free challenges
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports