FirstBlood-#210 — Reflective XSS on Register page leading to leak of PII data
This issue was discovered on FirstBlood v1
This report has been reviewed and accepted as a valid vulnerability on FirstBlood!
On 2021-05-12, xnl-h4ck3r Level 4
reported:
Summary
An XSS vulnerability exists on /register.php that allows an attacker to craft a URL which if clicked by a user can automatically leak the users drps cookie token to the attacker and using this they can access patient PII data. No other user interaction is needed.
The ref parameter can be used to display a Return to previous page link. The href attribute of the link is vulnerable to XSS and can also be used as an Open Redirect, e.g. ref=/\/attacker.com.
Steps to Reproduce
- Log in as an admin user.
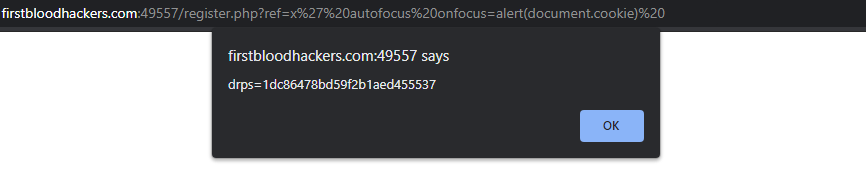
- Click the link
http://firstbloodhackers.com:49557/register.php?ref=x%27%20autofocus%20onfocus=alert(document.cookie)%20
- Observe the payload fires and displays the cookie:
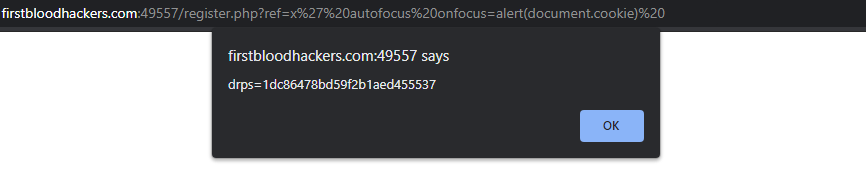
NOTE: This cookie can be sent to attackers server
- Clear all cookies and go to the web app again but do not log in.
- Add the cookie shows in Step 3 and go to
/drpanel/index.php and observe that you are now logged in as admin and view patient data.
Impact
If an attacker can phish a user to click the link containing the payload, they can view all patient PII data.
This report has been publicly disclosed for everyone to view
P3 Medium
Endpoint: /register.php
Parameter: ref
Payload: x%27%20autofocus%20onfocus=alert(document.cookie)%20
FirstBlood ID: 4
Vulnerability Type: Reflective XSS
The parameter "ref" is vulnerable to XSS on register.php. The developer made use of htmlentities but this is inadequate as the HREF is wrapped in single quotes.
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports