FirstBlood-#275 — Register as non admin doctor
This issue was discovered on FirstBlood v1
This report has been reviewed and accepted as a valid vulnerability on FirstBlood!
On 2021-05-15, twsec Level 2 reported:
i really cracked my head from this, at first i thought there must be some bypass or hidden api endpoint, but all it was some OSINT
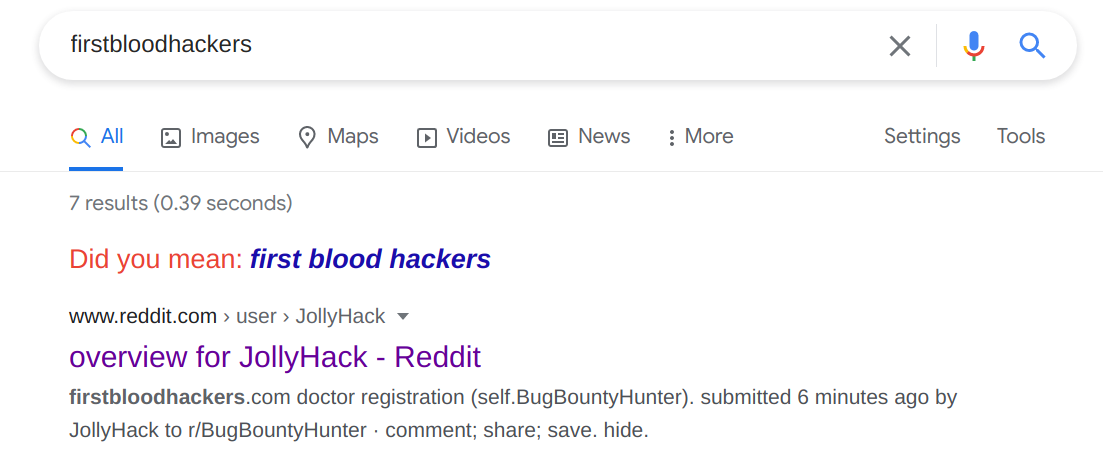
we google firstbloodhackers and we get
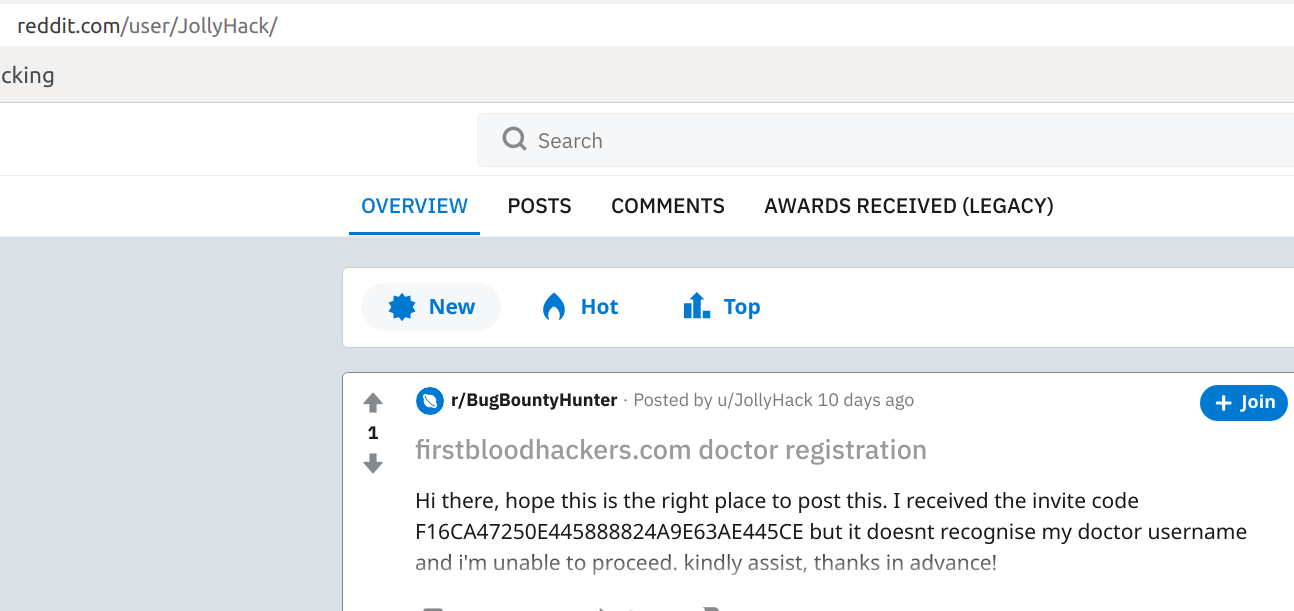
a reddit link we open it and
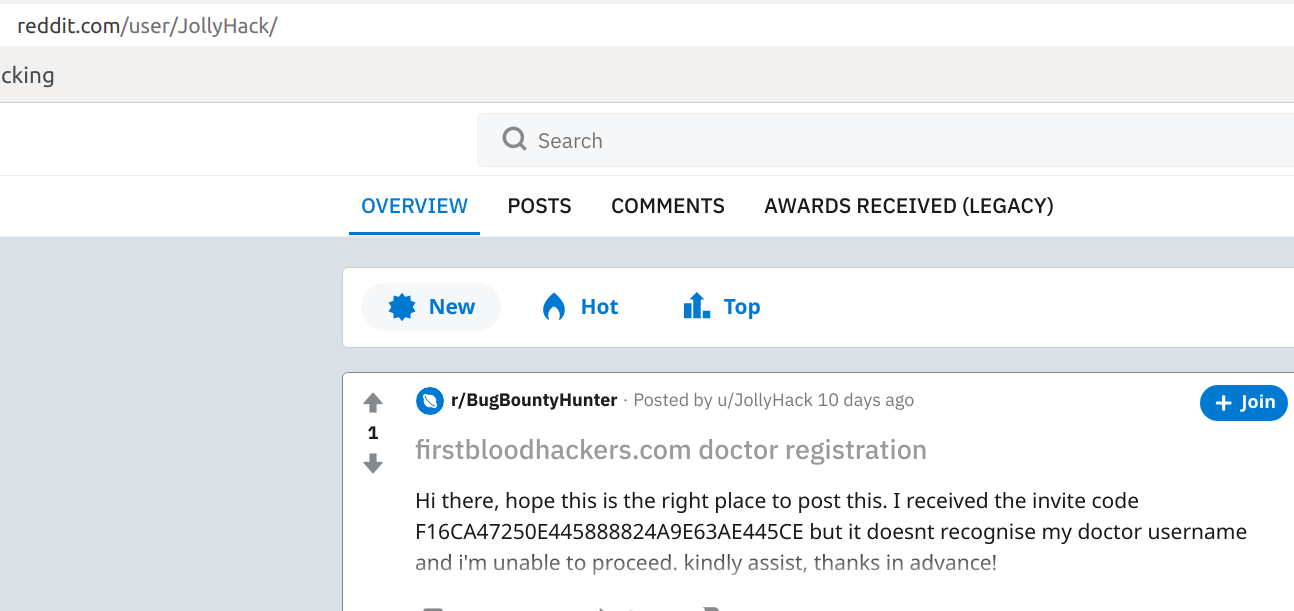
and we find the invite code
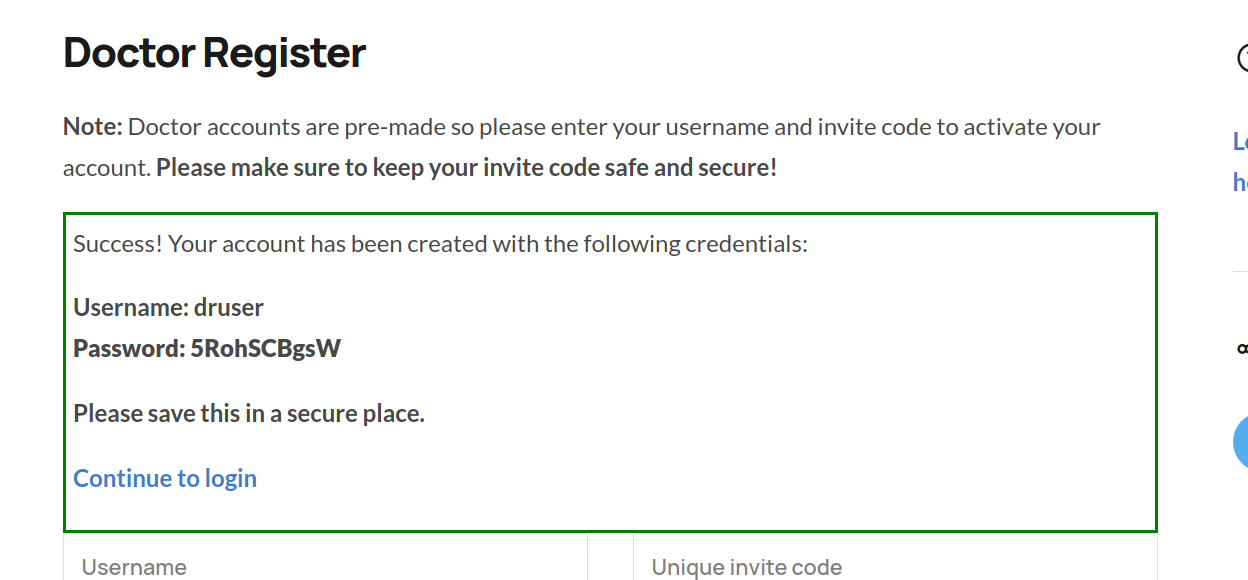
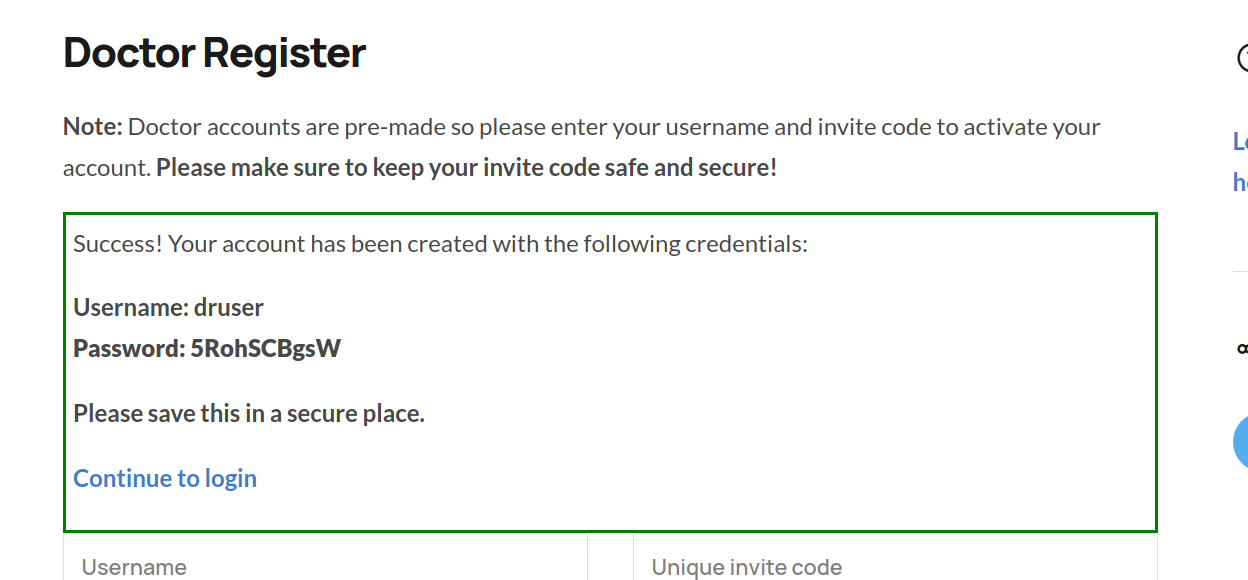
then we use the invite code and register a new doctor
This report has been publicly disclosed for everyone to view
P2 High
Endpoint: /register
Parameter: unique invite code
Payload: F16CA47250E445888824A9E63AE445CE
FirstBlood ID: 15
Vulnerability Type: Auth issues
A doctors invite code is leaked on the internet which if used grants anyone access to the doctor portal. The invite code should expire after use.
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports