FirstBlood-#436 — A doctors invite code is easily guessable and grants anyone access to the doctor portal and patient PII data
This issue was discovered on FirstBlood v2
This report has been reviewed and accepted as a valid vulnerability on FirstBlood!
On 2021-10-25, xnl-h4ck3r Level 4
reported:
Summary
It is possible due to a number of vulnerabilities that an attacker is able to register on the app and obtain all patient PII data.
On endpoint /register.php it says:
Note: Doctor accounts are pre-made so please enter your username and invite code to activate your account
- Firstly, an invite code of
test is easily guessable while they are testing their new version.
- Secondly, an invite code can be used multiple times so an attacker has the opportunity to make use of this code even if used before.
- Thirdly, an attacker is able to register using any user name, not just a Doctor account that has been pre-made (although likely usernames are on
/doctors.html).
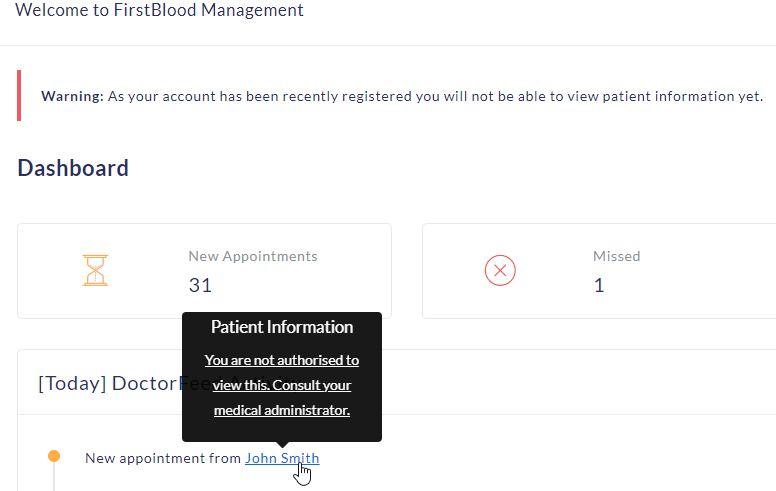
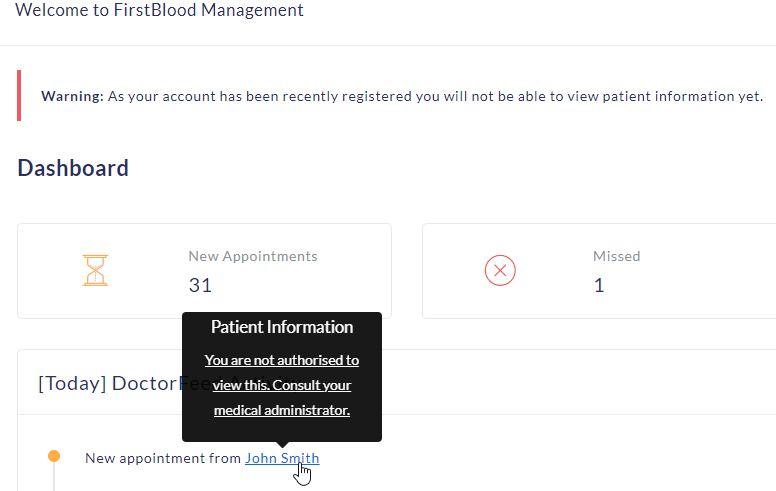
Once registered, the attacker can then access the Management panel on /drpanel/index.php. The user is informed with Warning: As your account has been recently registered you will not be able to view patient information yet.
The attacker has access to patients full names who have appointments that day, and who have cancelled appointments.
Steps To Reproduce
- Go to
/register.php, enter a user name and Unique invite code of test
- Log in as the new user, and observe the message below:
Impact
Authorisation controls can be bypassed allowed new users access to patient appointment PII data
This report has been publicly disclosed for everyone to view
P3 Medium
Endpoint: /register.php
Parameter: n/a
Payload: test
FirstBlood ID: 24
Vulnerability Type: Auth issues
The old invite code was deleted but when testing FirstBlood v2 the developers accidentally left the test code working.
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports