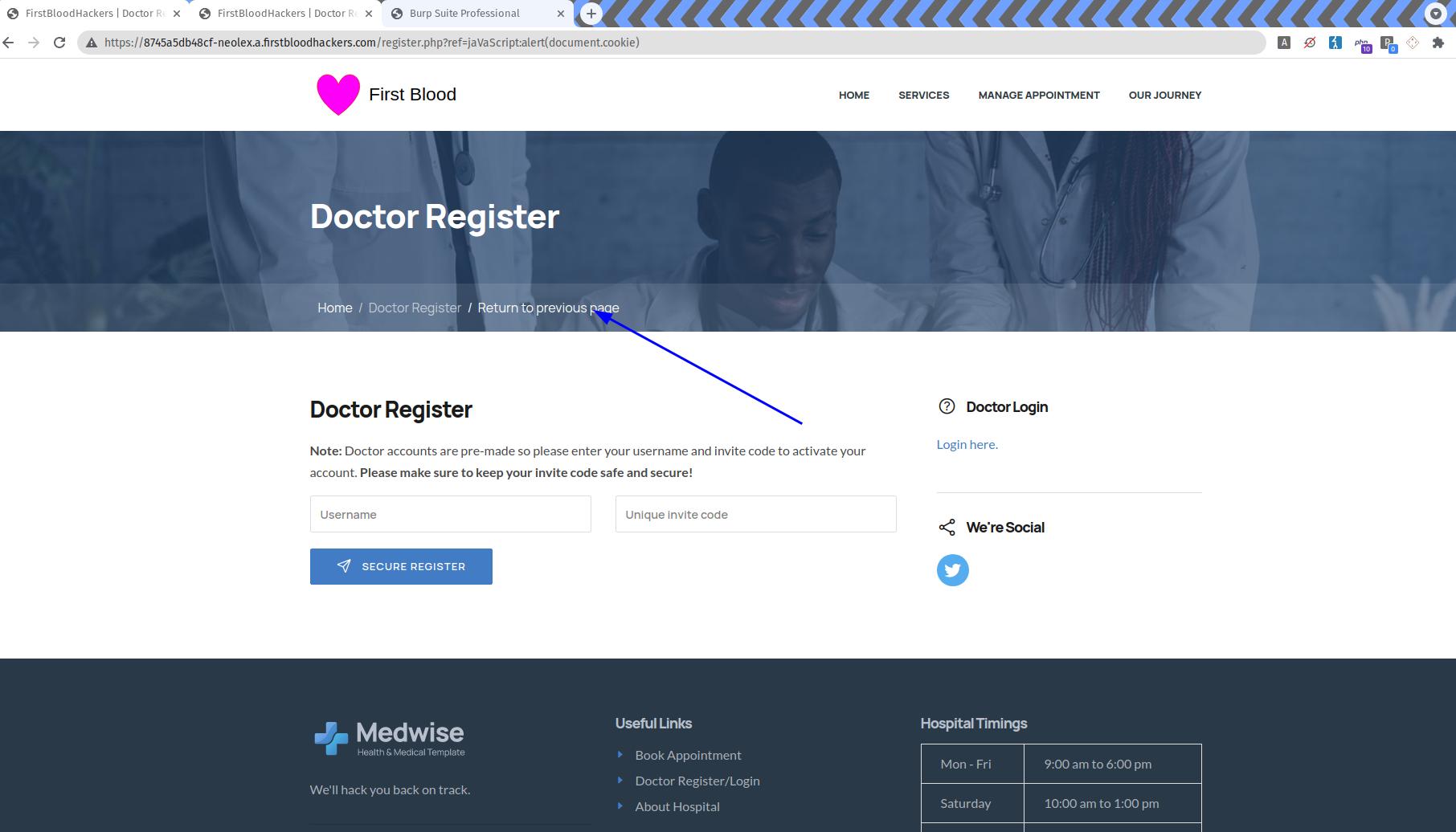
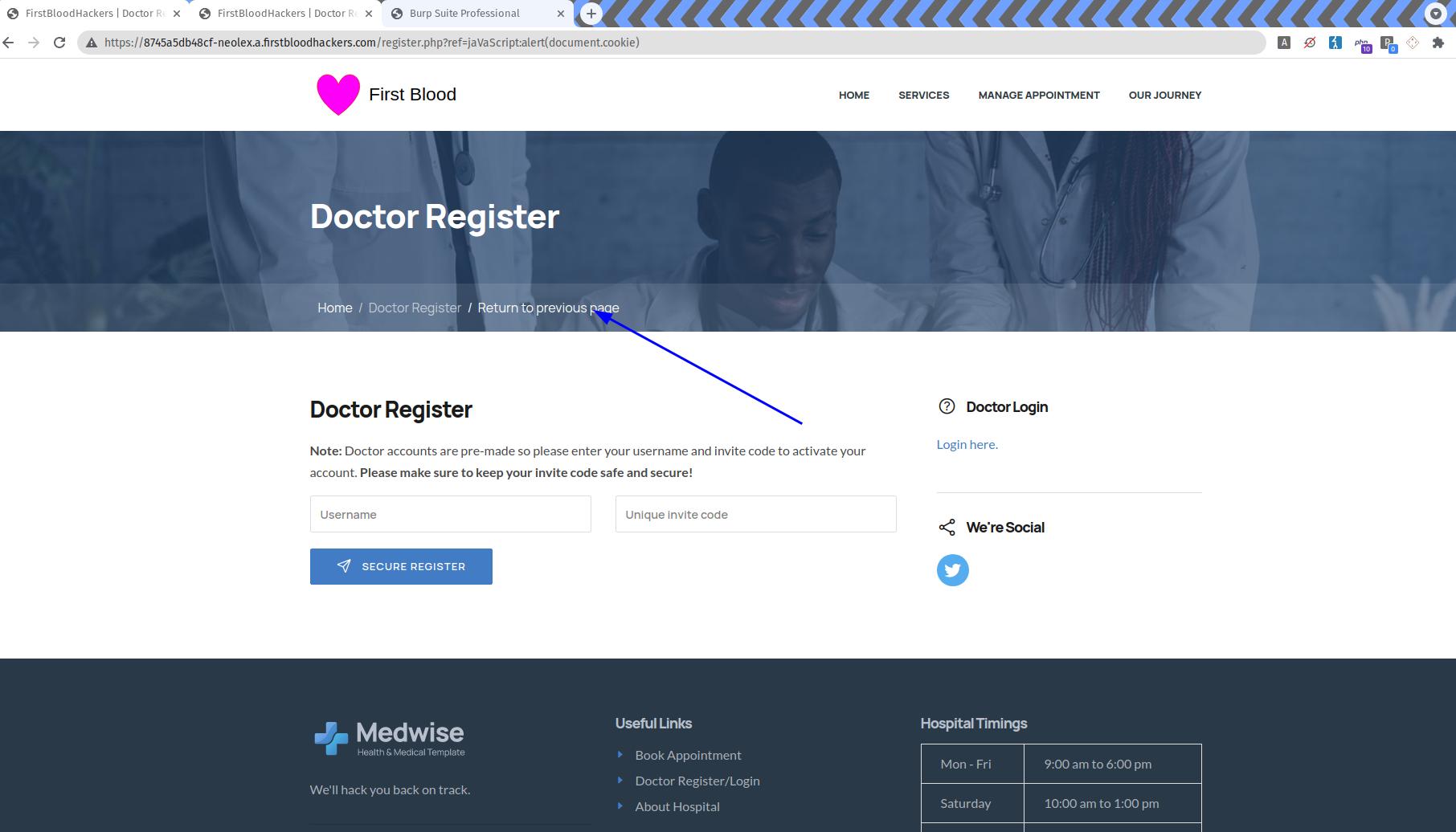
FirstBlood-#565 — Reflected XSS inside ref parameter on /register.php
This issue was discovered on FirstBlood v2
This report has been reviewed and accepted as a valid vulnerability on FirstBlood!
On 2021-10-26, neolex Level 2 reported:
Description
The ref parameter is vulnerable to reflected XSS
The value is reflected inside a <a> tag inside the webpage.
It can be use to open redirect but also can be upgraded to reflected xss with javascript uri
The javascript keyword is replaced by nope but the replace is case sensitive, and because javascript uri are case insentive we can bypass the filter by using an uppercase inside the javascript word.
Step to reproduce
Impact
The impact is XSS, an attacker can execute javascript inside user's browser and they can steal cookies.
This report has been publicly disclosed for everyone to view
P3 Medium
Endpoint: /register.php
Parameter: ref
Payload: jaVasCript:alert(document.cookie)
FirstBlood ID: 32
Vulnerability Type: Reflective XSS
The parameter ?ref on register.php was poorly fixed and can be bypassed in various ways. Firstly the developer failed to use strtolower() when comparing strings, and the use of characters such as %09 will also bypass the filter.
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports