You are viewing our old website
We are busy working on a brand new website and platform. All of the content on this website is considered out-dated, however challenges and our members section are working as before. Stay tuned for updates!
FirstBlood-#586 — Open Redirect on logout.php endpoint [Bypass]
This issue was discovered on FirstBlood v2
This report has been reviewed and accepted as a valid vulnerability on FirstBlood!
On 2021-10-26, holybugx Level 5
reported:
Description
Hello Sean,
The developer tried to fix the previously reported Open Redirect by converting \ to . However, this issue has not been properly patched, and an attacker can bypass this.
/drpanel/logout.php?ref=/\/attacker.com —Location—> //attacker.com
/drpanel/logout.php?ref=/\/attacker.com —Location—> /./attacker.com
Steps To Reproduce
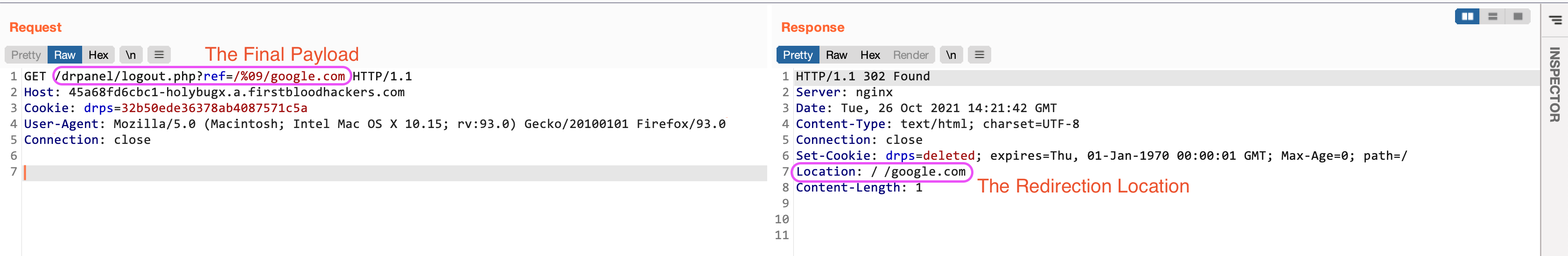
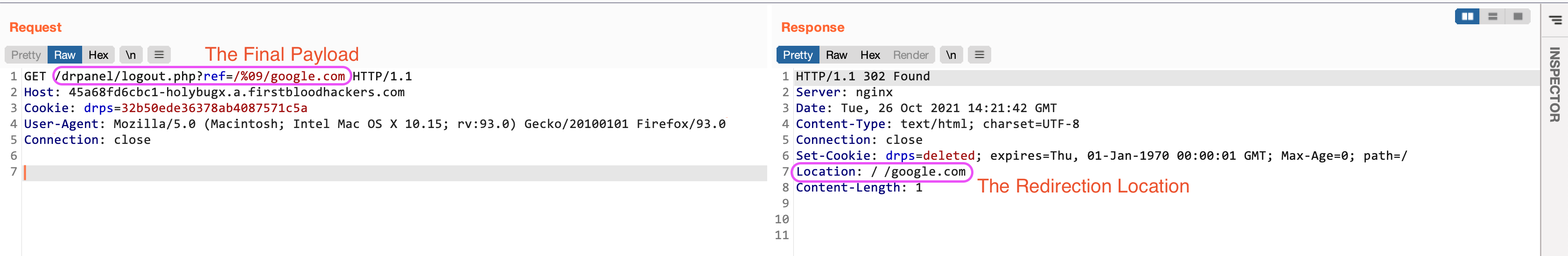
- Use the following payload to bypass the checks:
/drpanel/logout.php?ref=/%09/attacker.com
Notes
- The
%09 is the URL Encoded value of the tab character
- This payload only works on Chromium-Based browsers.
Impact
- Open Redirect leading to various phishing attacks.
Remediation
- Implement proper URL Validators.
Kind Regards,
HolyBugx
This report has been publicly disclosed for everyone to view
P4 Low
Endpoint: /drpanel/logout.php
Parameter: ref
Payload: /%09/google.com
FirstBlood ID: 18
Vulnerability Type: Open Redirect
The open redirect bug on logout.php was fixed but the code still failed to filter out certain characters such as %09 and thus the endpoint is still vulnerable to open redirect. This vulnerability only affects chrome.
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports