FirstBlood-#635 — DrAdmin ATO by using doctor account.
This issue was discovered on FirstBlood v2
This report has been reviewed and accepted as a valid vulnerability on FirstBlood!
On 2021-10-26, vishal Level 2 reported:
Discription : drAdmin ATO by using doctor account.
Steps to Reproduce:
- visit /register.php

2.give any user name and in invite code enter test as below.
-
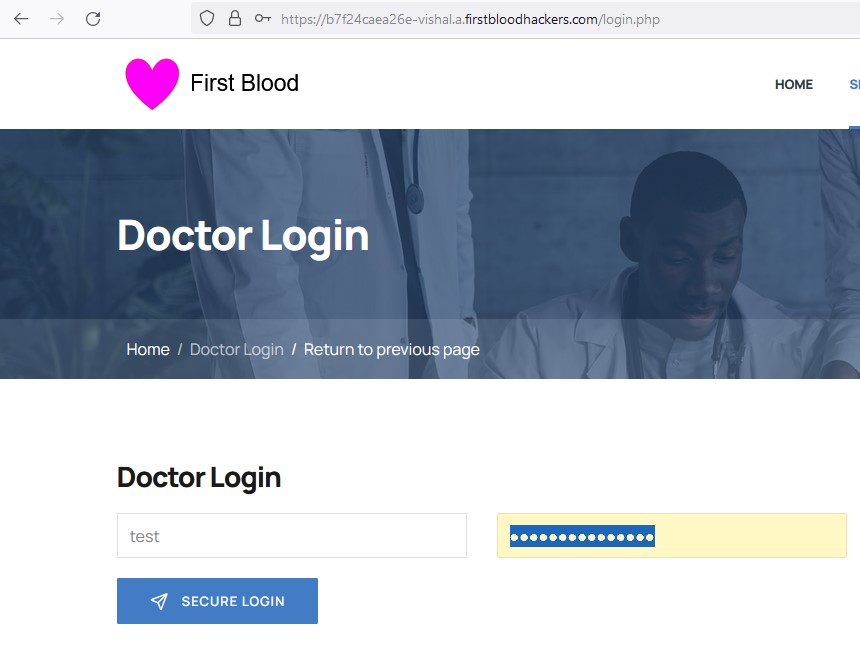
use the credential's you got to login at /login.php. you will get access to dr panel.

-
VIew-source code of page you will notice . there is a function to editpassword named editpassword and it uses POST method, header it set etc.

-
After Playing for while in repeater . I got the response for which i was waiting .

Now all you need to do is do to /login.php and enter updated password you just got for drAdmin username & you will be login as drAdmin which a admin account.
Impact: doctor can takeover admin doctor account .
Lastly if anything is missing just ping me,
regard's Vishal.
This report has been publicly disclosed for everyone to view
P1 CRITICAL
Endpoint: /drpanel/drapi/editpassword.php
This report contains multiple vulnerabilities:
FirstBlood ID: 24
Vulnerability Type: Auth issues
The old invite code was deleted but when testing FirstBlood v2 the developers accidentally left the test code working.
FirstBlood ID: 27
Vulnerability Type: Application/Business Logic
It is possible to edit the admins password (dradmin) from /drapi/editpassword as it's only looking for the username. Usernames can be enumerated when logging in as trying 'drAdmin' results in a different error. The username can also be found from FirstBlood v1.
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports