FirstBlood-#7 — PII leak via /drpanel/drapi/qp.php?name=sanjay
This issue was discovered on FirstBlood v1
This report has been reviewed and accepted as a valid vulnerability on FirstBlood!
On 2021-05-09, codersanjay Level 3 reported:
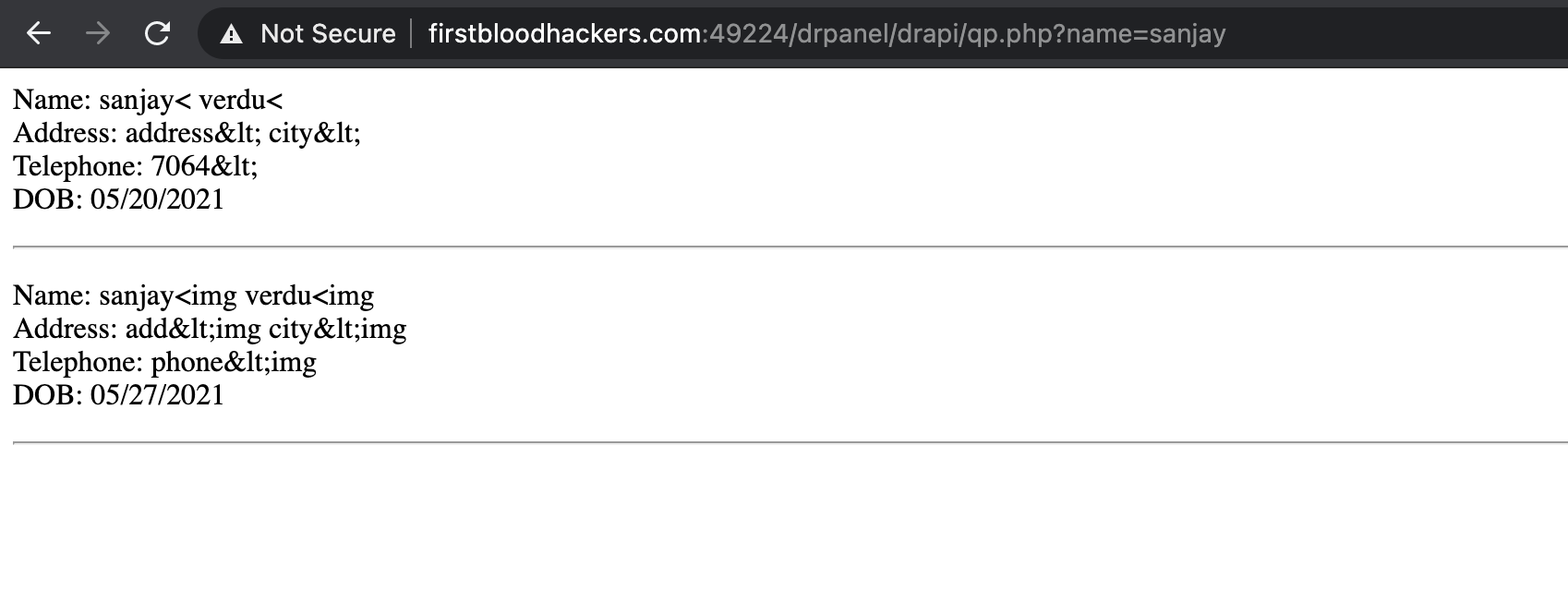
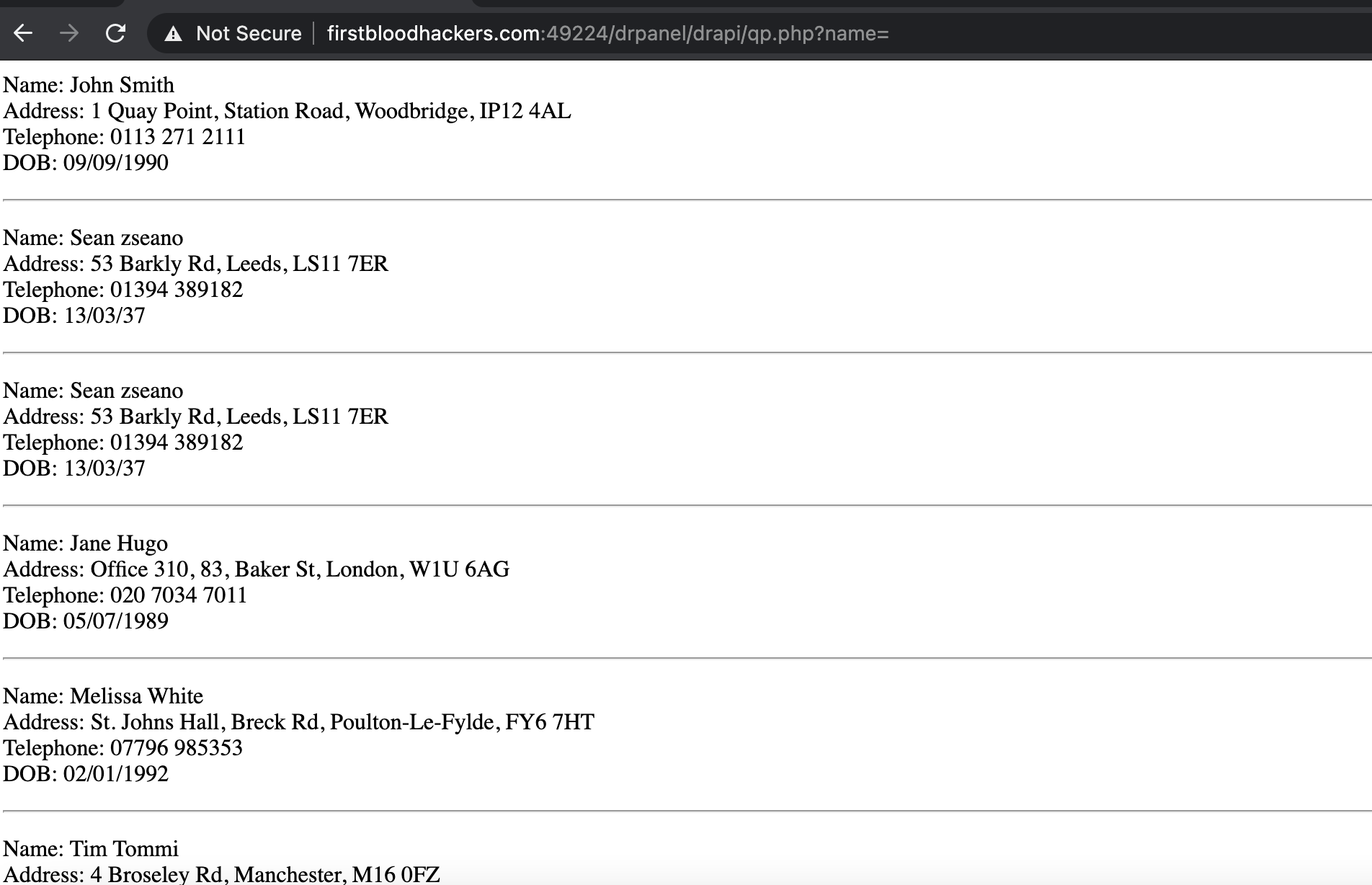
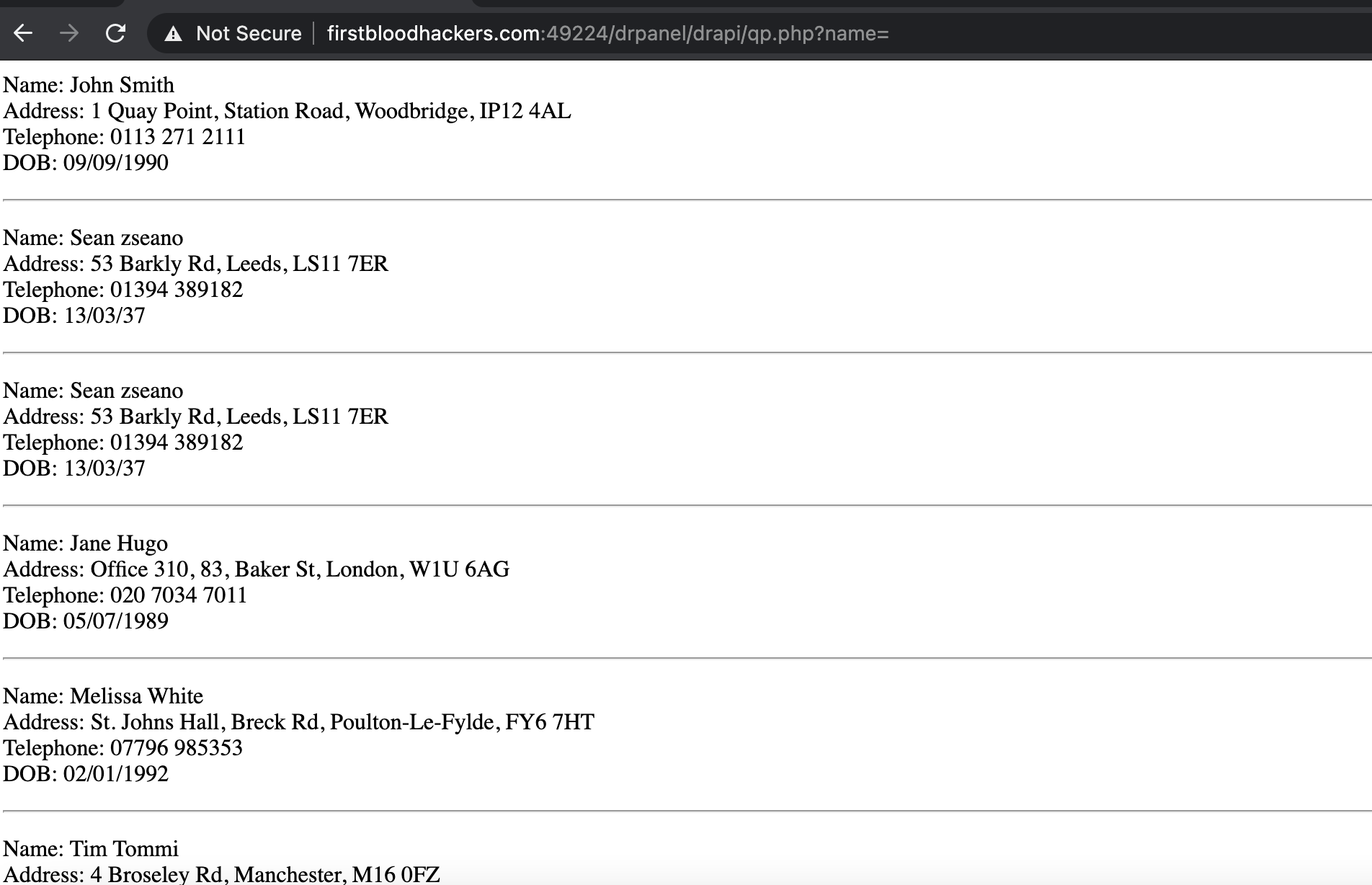
Even a non login person can view paatients PII data via below link.
http://firstbloodhackers.com:49224/drpanel/drapi/qp.php?name=sanjay
Impact
PII leak of patient.
Note:empty value in name will give all patient details.
This report has been publicly disclosed for everyone to view
P1 CRITICAL
Endpoint: /drpanel/drapi/qp.php?name=sanjay
Parameter: name
Payload: sanjay
FirstBlood ID: 12
Vulnerability Type: Auth issues
If the request method is changed from POST to GET, then the endpoint /drapi/qp.php becomes available to ANY user due to an application logic error
 Report Feedback
Report Feedback
@zseano
Creator & Administrator
Nice find codersanjay! You're the first to discover this and this is the very first bounty we've awarded.. congratulations!!!
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports 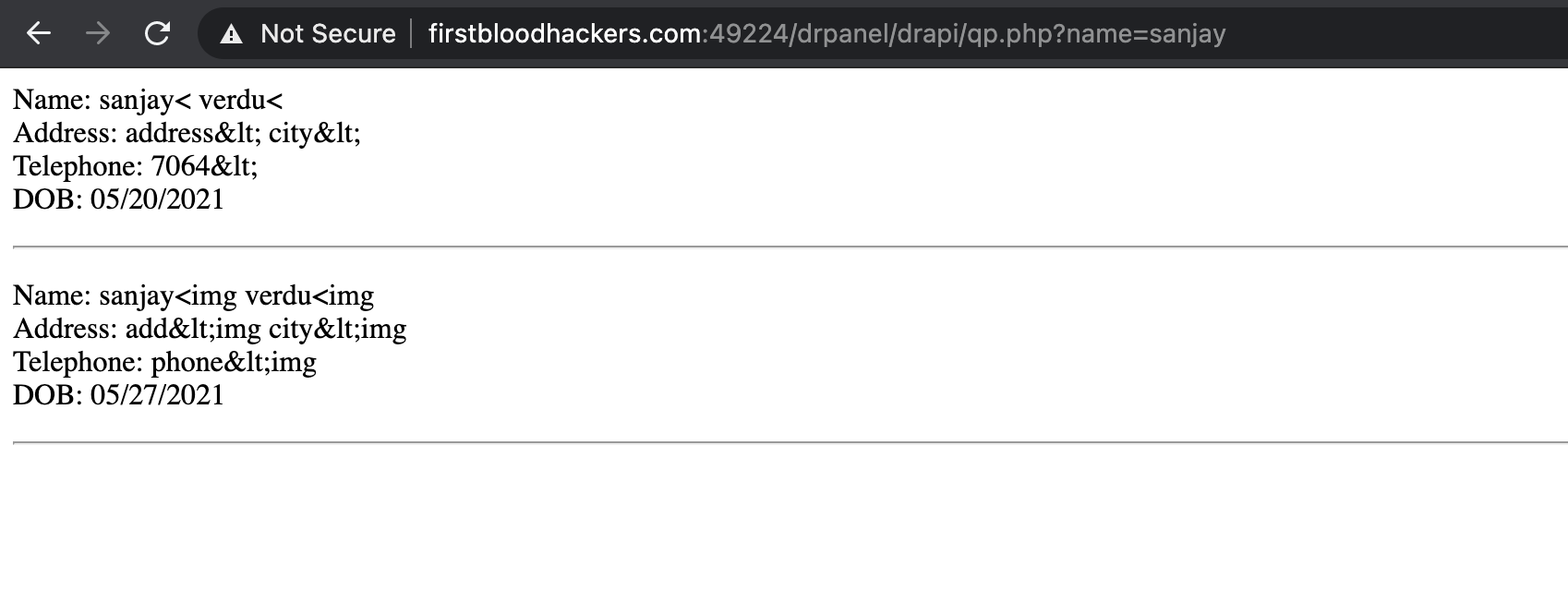
 Report Feedback
Report Feedback