The BugBountyHunter website and membership platform will be closing in the next few days and our website plus membership platform, including all material such as BARKER, FirstBlood etc will become inaccessible. We will be sharing a blog post detailing what's to come in the future and will add a link here when available. Thanks for all your support over the years, i've truly enjoyed mentoring and helping others with their bug bounty journey. ~zseano
FirstBlood-#830 — Patients can still change their application email
This issue was discovered on FirstBlood v2
This report has been reviewed and accepted as a valid vulnerability on FirstBlood!
On 2021-10-29, 0x1452 Level 3 reported:
Hey!
Summary
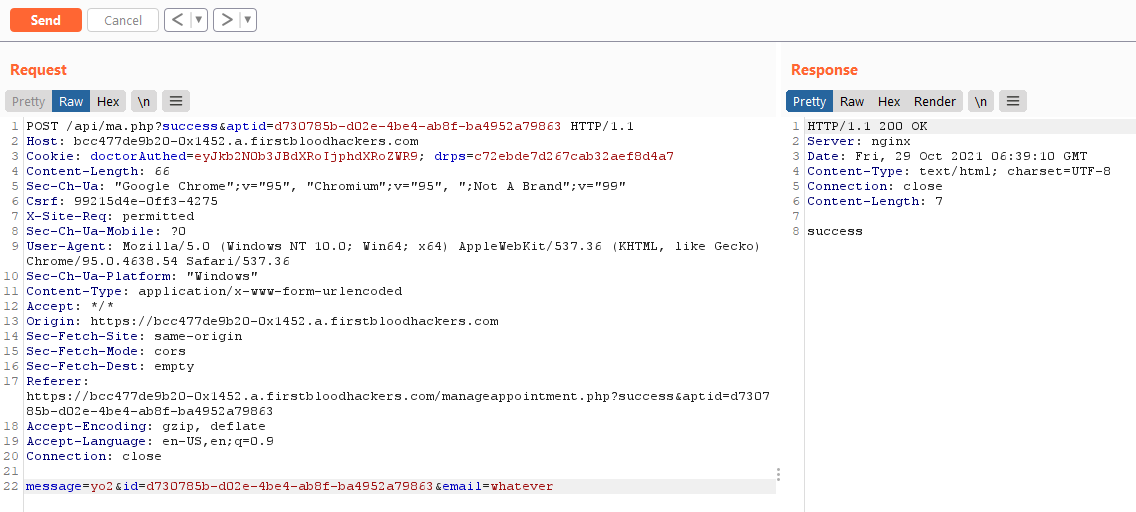
In the previous version it was reported that patients were able to edit their email on applications if the doctorAuthed=eyJkb2N0b3JBdXRoIjphdXRoZWR9 cookie was present. This cookie is automatically set after trying to register, even if it fails.
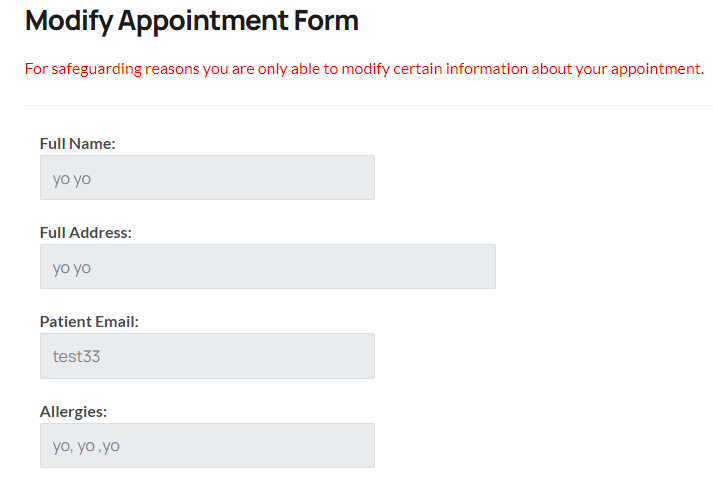
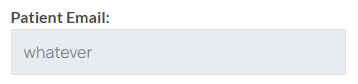
This issue is still present and the UI still tells us that we're not supposed to be allowed to edit our email:
Steps to reproduce
- Try to register at
/register.php (doesn't matter if it's valid or not). Alternatively, set the cookie doctorAuthed=eyJkb2N0b3JBdXRoIjphdXRoZWR9 manually.
- Book an appointment at
/book-appointment.php
- Copy the appointment ID and submit it at
/yourappointments.php
- Notice that the UI only lets you edit your message. Click on Modify Appointment.
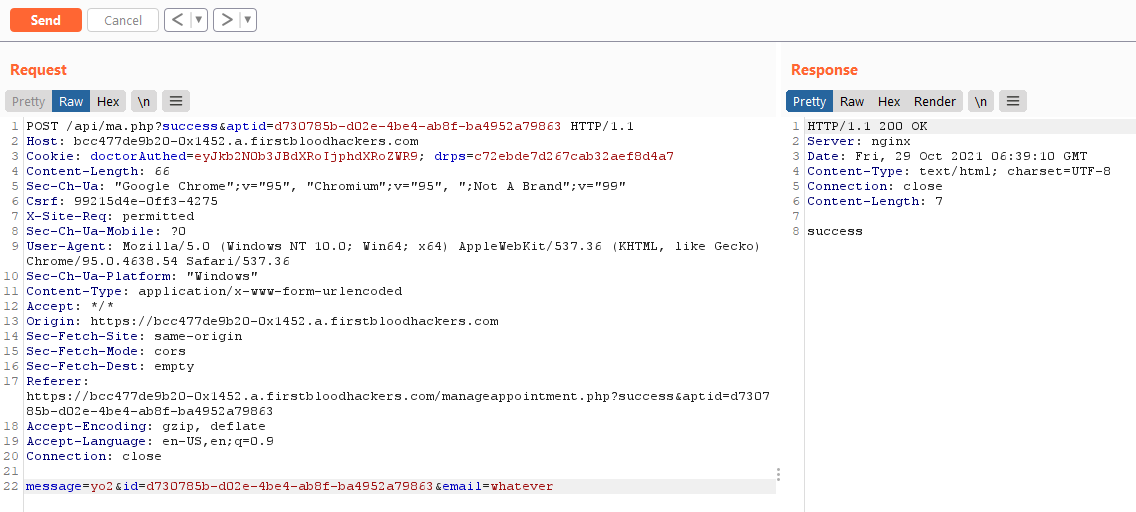
- Repeat the request to
/api/ma.php in a tool like Burp but add the parameter email=whatever to the body
- Repeat step 3 or directly navigate to
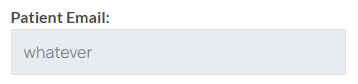
/manageappointment.php?success&aptid=:aptid and notice that the email got changed to whatever
This report has been publicly disclosed for everyone to view
P3 Medium
Endpoint: /api/ma.php
Parameter: email
Payload: anything
FirstBlood ID: 33
Vulnerability Type: Application/Business Logic
Our mistake: We did not intentionally leave the code to change emails if the correct values were set, however it created interesting results because most discovered this but missed bug ID 20 and 21 and whilst it was not possible to modify via integer, if the ID was known it would still work.
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports