FirstBlood-#870 — Swagger UI reveals unauthenticated endpoint leaking sensitive data
This issue was discovered on FirstBlood v2
This report has been reviewed and accepted as a valid vulnerability on FirstBlood!
On 2021-10-29, sumyth Level 2 reported:
Hi,
Please find a brief description of the vulnerability below,
Summary
On firstbloodhackers.com, it is possible to find hidden endpoints using basic directory fuzzing to reveal a Swagger API endpoint. The endpoint discloses a method which in turn reveals sensitive information related to vaccination without requiring any kind of authentication.
Steps to Reproduce:
-
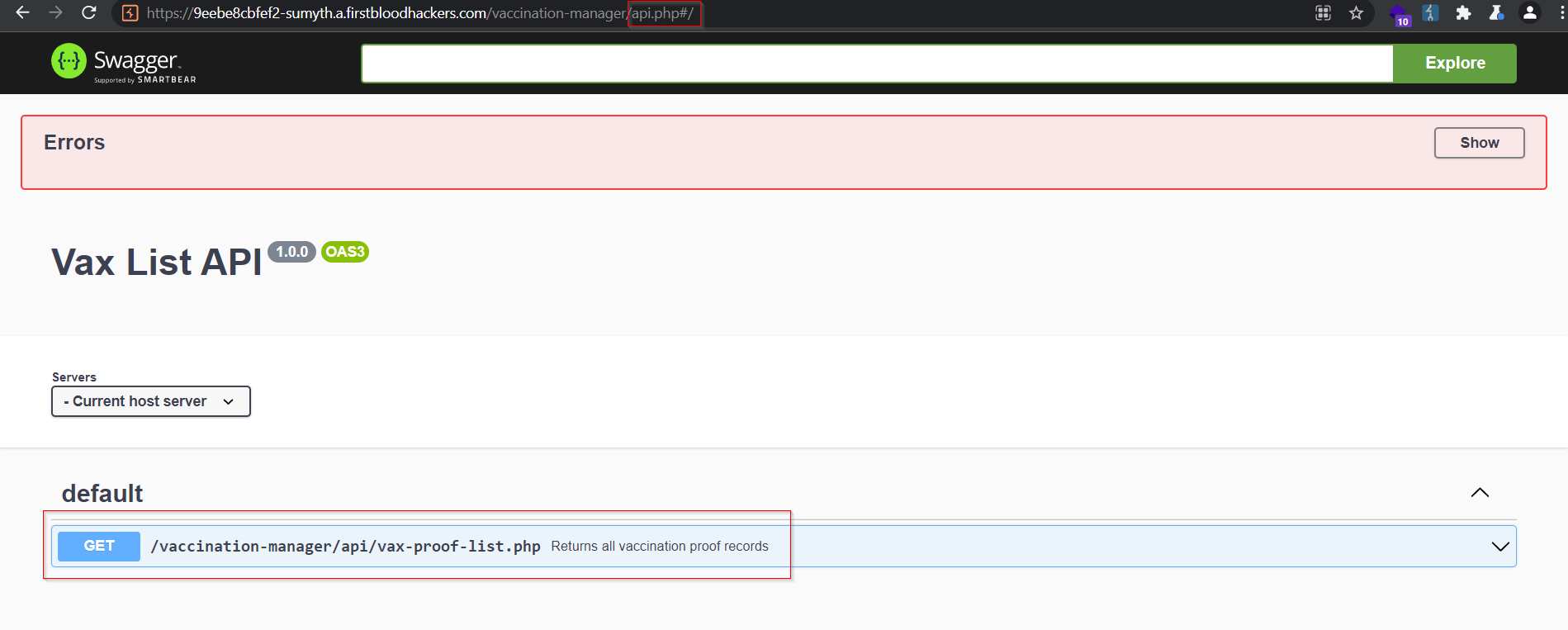
Visit the Swagger UI endpoint at - <truncated>.a.firstbloodhackers.com/vaccination-manager/api.php
-
Observe the API method listed,
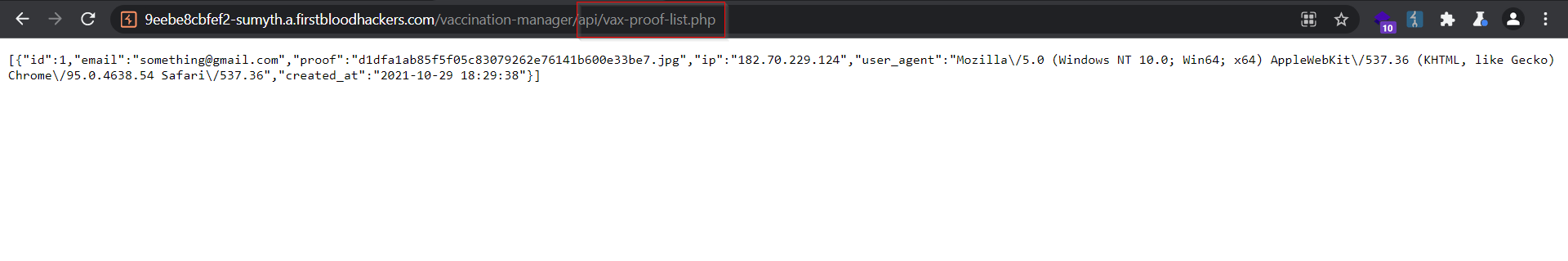
- Copy the method URL and open it in a new tab. Observe that it reveals the sensitive data regarding vaccination certificates uploaded including email, filename, IP.
Impact
Unauthorized access to API endpoints poses the threat of disclosing sensitive PII information.
This report has been publicly disclosed for everyone to view
P1 CRITICAL
This report contains multiple vulnerabilities:
- Information leak/disclosure
- Information leak/disclosure
FirstBlood ID: 31
Vulnerability Type: Information leak/disclosure
The endpoint api.php can be found under the vaccination manage portal directory which allows for user interaction and results in PII leak on vax-proof-list.php
FirstBlood ID: 37
Vulnerability Type: Information leak/disclosure
The endpoint /vaccination-manager/api/vax-proof-list.php leaks PII without any authentication. The intended solution was to find it via swagger-ui at /vaccination-manager/api.php
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports